EXCLUSIVE: THE GUARDIANS BETRAYED — HOW YOUR CYBERSECURITY TOOLS BECAME THE ENEMY'S WEAPON
In a stunning reversal of digital trust, the very tools millions rely on to secure their code have been weaponized against them. This is not a minor data breach; this is a systemic collapse of the software supply chain, starting at its most sacred point: the security scanner itself.
The attack began on March 19th, targeting Trivy, a ubiquitous open-source vulnerability scanner embedded in countless automated development pipelines. Hackers from the shadowy TeamPCP group executed a masterstroke of deception, Trojanizing the tool's official GitHub Actions and Docker images. Every scan performed didn't find flaws—it CREATED them, deploying malware that vacuumed up SSH keys, cloud credentials, and crypto wallets in a silent, automated heist. Assigned the critical identifier CVE-2026-33634 with a devastating 9.4 severity score, this was a zero-day exploit of unimaginable scale.
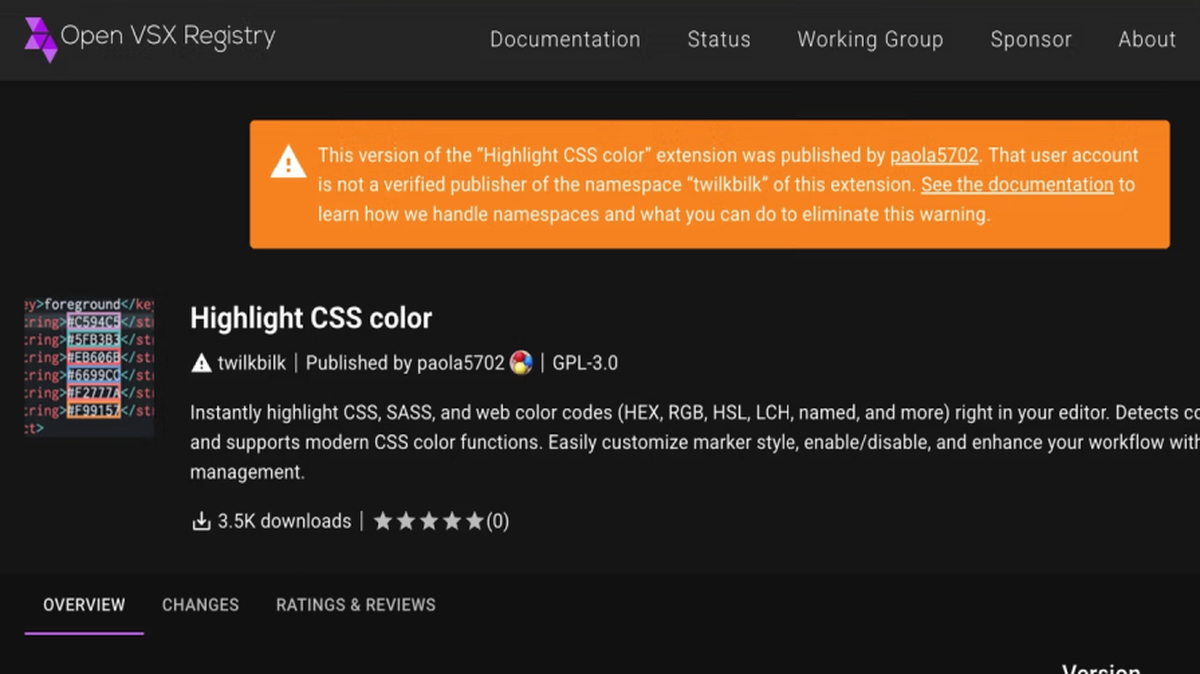
But the nightmare was just beginning. Within days, the contagion spread. On March 23rd, the same attackers compromised GitHub Actions for Checkmarx's AST and KICS tools—cornerstones of application security testing. They even poisoned associated OpenVSX extensions. The very next day, the LiteLLM AI gateway, which uses Trivy's code, had malicious versions uploaded to the PyPI repository. Each incident lasted mere hours, but in the world of automated DevOps, that's an eternity for malware to spread.
"Think of it as poisoning the well at the source," explains a senior incident responder from a top-tier firm. "They didn't just exploit a vulnerability; they hijacked the mechanism designed to find vulnerabilities. The automation we depend on for speed became the vector for a self-replicating catastrophe, leading to persistent backdoors in critical systems like Kubernetes clusters."
This is the ultimate phishing scheme, but for machines. Your automated build process, trained to trust these tools, willingly executed the enemy's code. The implications for blockchain security are particularly dire, as automated pipelines managing crypto assets were directly in the crosshairs. This attack proves that no layer of the modern tech stack is safe, turning defenders' expertise against them.
We are entering a new era where security tools themselves will be the most high-value targets. The next major ransomware campaign won't start with a phishing email to an employee; it will begin with a poisoned commit in a trusted scanner's repository. The walls have not just been breached—they have been recruited.
When your sentinels are taking orders from the enemy, who do you trust?