Cybersecurity researchers have identified a significant evolution in the ongoing GlassWorm malware campaign, marking a dangerous escalation in its method of propagation through the Open VSX registry. The campaign, which has persistently targeted developer ecosystems, has shifted its strategy from directly embedding malicious loaders to a more sophisticated, transitive delivery model. According to a report from software supply chain security firm Socket, the threat actor is now exploiting the `extensionPack` and `extensionDependencies` features within Visual Studio Code extensions. This technique allows initially benign-looking extensions to be updated later with dependencies that pull in separate, malicious GlassWorm-linked components. This method effectively establishes trust with the developer first before deploying the payload, making detection more challenging.
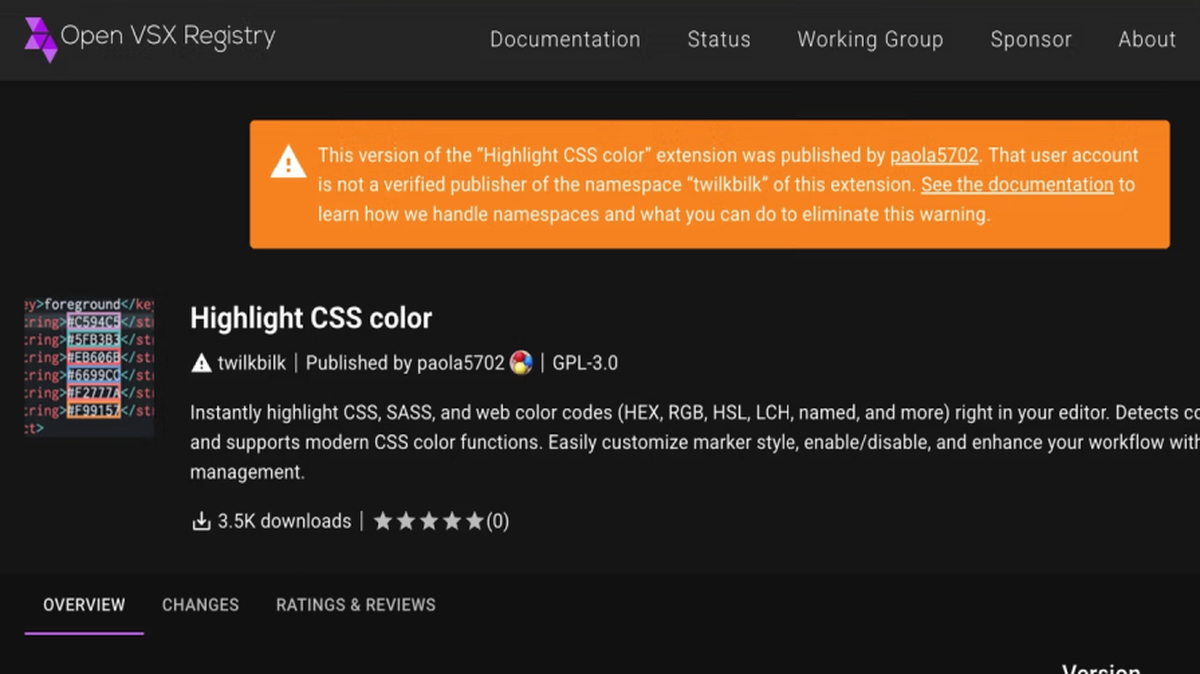
The scale of this latest offensive is substantial. Socket reported discovering at least 72 additional malicious extensions uploaded to the Open VSX registry since January 31, 2026. These extensions are carefully crafted to impersonate popular and trusted developer tools, including linters, code formatters, code runners, and utilities for AI-powered coding assistants like Clade Code and Google Antigravity. By masquerading as legitimate productivity tools, the attackers increase the likelihood of developers unknowingly installing them. The Open VSX registry has since taken action to remove the identified malicious packages, but the incident underscores the persistent threat to open-source software repositories.
GlassWorm is a persistent threat campaign known for infiltrating developer platforms, primarily the Microsoft Visual Studio Marketplace and the open-source alternative, Open VSX. Its malicious extensions are designed to steal sensitive secrets, drain cryptocurrency wallets, and co-opt infected developer systems into proxy networks for further criminal activities. While Koi Security first brought widespread attention to the campaign in October 2025, evidence suggests these tactics, such as using invisible Unicode characters to hide malicious code, were present in npm packages as early as March 2025, indicating a longer and more coordinated operation.
The latest iteration retains the campaign's known technical signatures while adding new layers of evasion. The malware continues to perform system checks to avoid infecting machines with a Russian locale, a common tactic to minimize scrutiny from certain regions. It also utilizes Solana blockchain transactions as a dead drop resolver—a method to fetch the actual command-and-control (C2) server address—enhancing the infrastructure's resilience against takedowns. Notably, this new wave of extensions employs heavier code obfuscation and rotates through multiple Solana addresses, making static analysis and blocking efforts more difficult for defenders. This evolution highlights the adaptive nature of supply chain threats targeting the software development lifecycle.