THE DOCTOR IS OUT: HOW "SECURITY BY DENIAL" IS CREATING A MASSIVE CORPORATE VULNERABILITY
For years, enterprise cybersecurity was personified by a single, infamous figure: Doctor No. This gatekeeper's sole function was to block every new tool, from AI assistants to file-sharing apps, with a reflexive "No." It looked like vigilance. In 2024, it's revealed as the company's greatest self-inflicted vulnerability.
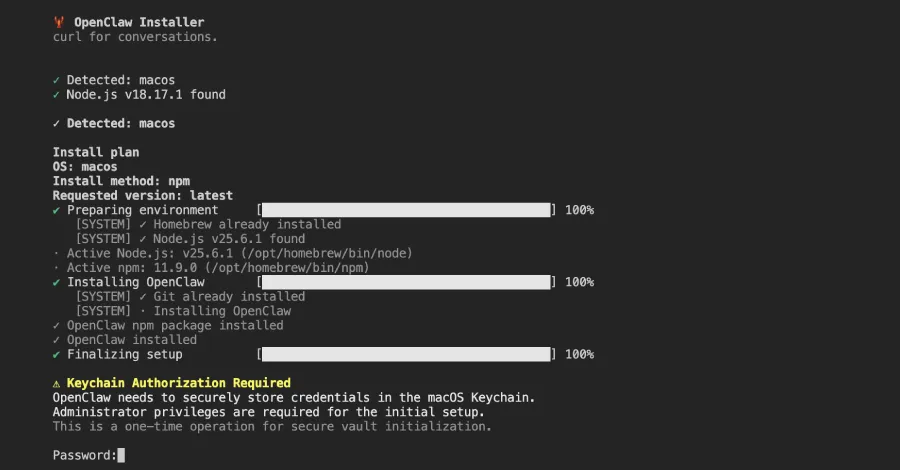
This culture of blanket denial has backfired catastrophically. By refusing to securely enable business-critical tools, these departments have driven entire teams to use shadow IT—unvetted, unmonitored applications that are a paradise for phishing and malware. The very data breach they feared becomes inevitable, not through a sophisticated zero-day exploit, but through an unsecured backdoor they forced employees to create.
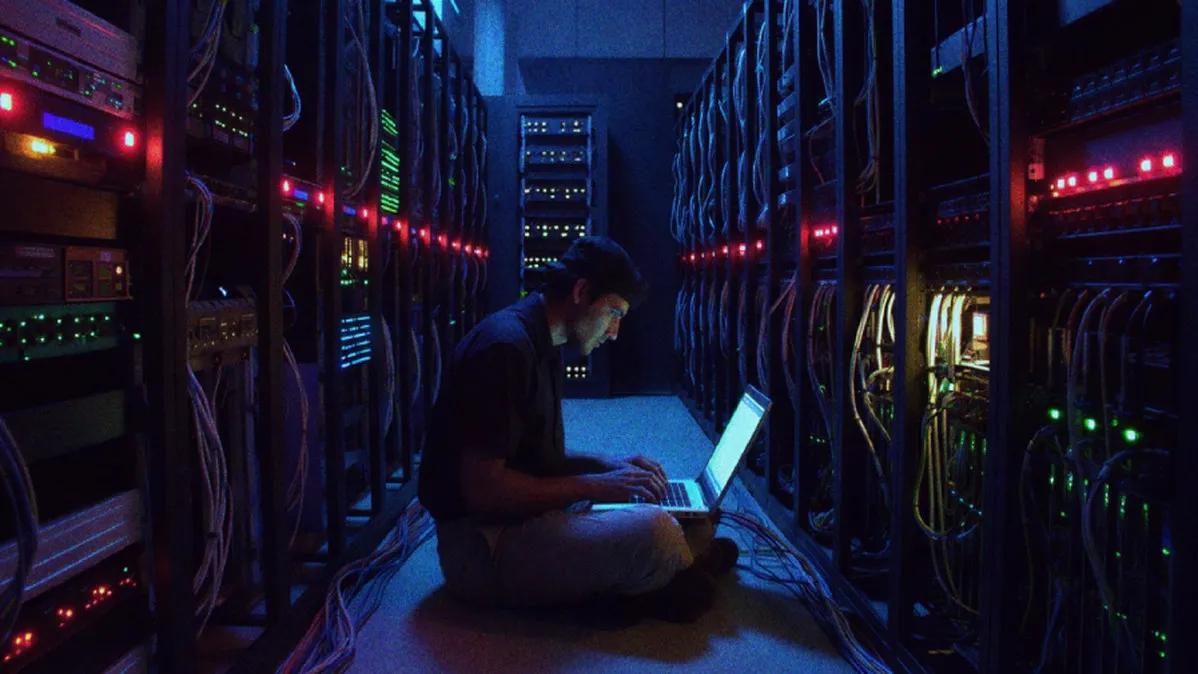
"Doctor No creates a false sense of security," explains a veteran CISO at a Fortune 500 firm. "You haven't mitigated risk; you've just lost visibility. When teams go around you, you have no logging, no policy control, and no way to detect a ransomware exploit until it's too late. True cybersecurity is about secure enablement, not just obstruction."
This matters because the threat landscape has evolved. Modern ransomware gangs use advanced phishing campaigns targeting employee frustration with clunky, approved tools. A single click on a malicious link in an unofficial app can lead to a crippling cascade. Meanwhile, the promise of blockchain security for verification and crypto for transactions is ignored, leaving companies using obsolete, vulnerable systems.
We predict a wave of major incidents traced directly to this obstructive culture. The CISO role will pivot from gatekeeper to business enabler, architecting secure frameworks for the tools the business demands.
The era of saying "No" is over. Now, it's about building a "Yes, securely."