Cybersecurity researchers have uncovered a sophisticated malicious campaign targeting developers through the npm registry. A package named "@openclaw-ai/openclawai," uploaded by a user "openclaw-ai" on March 3, 2026, has been identified as a trojanized installer for the OpenClaw AI tool. To date, the package has been downloaded 178 times and remains available on the public registry, posing an ongoing threat. The discovery, made by JFrog's security team, highlights a concerning trend of attackers exploiting trusted software repositories and developer workflows to distribute malware.
The malicious package is engineered to deploy a full-featured remote access trojan (RAT) and conduct extensive data theft from compromised macOS systems. According to JFrog's analysis, the malware, internally identified as "GhostLoader," is designed to harvest a wide array of sensitive information. This includes system credentials, browser data (such as cookies and history), cryptocurrency wallet files, SSH keys, the Apple Keychain database, and iMessage chat history. Furthermore, the package establishes a persistent RAT with capabilities for remote system access, SOCKS5 proxy tunneling, and even live browser session cloning, which could allow attackers to hijack authenticated web sessions.
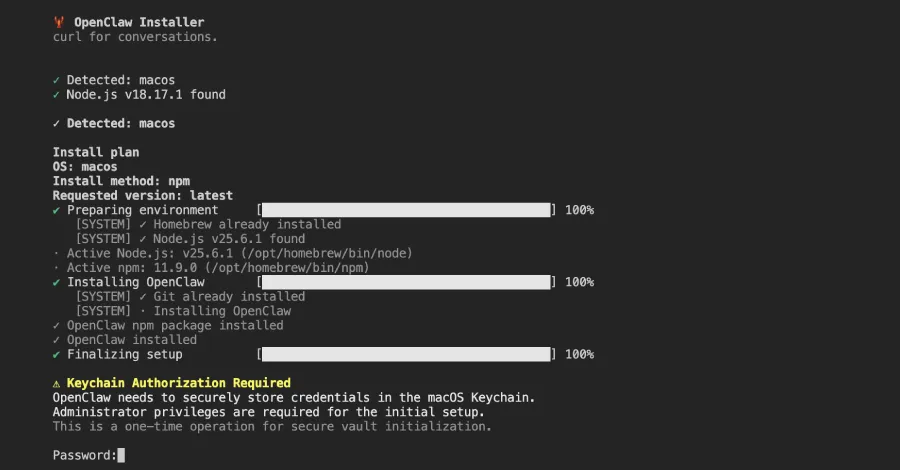
The attack employs a multi-stage execution chain initiated through a clever abuse of npm's `postinstall` script hook. Upon installation, this hook triggers a command to re-install the package globally (`npm i -g @openclaw-ai/openclawai`). The package's `package.json` file defines a `bin` property, which points to `scripts/setup.js`. This mechanism effectively registers the malicious script as a globally accessible command-line tool named "OpenClaw." The `setup.js` file acts as a first-stage dropper, presenting users with a highly convincing fake command-line interface complete with animated progress bars to simulate a legitimate software installation process.
Following the fake installation, the script displays a fraudulent iCloud Keychain authorization prompt, a classic social engineering tactic designed to trick users into surrendering their system password. As noted by JFrog security researcher Meitar Palas, "The attack is notable for its broad data collection, its use of social engineering to harvest the victim's system password, and the sophistication of its persistence and C2 [command-and-control] infrastructure." Simultaneously with this password prompt, the dropper retrieves an encrypted second-stage payload, written in Java, from its command-and-control server. This next stage is responsible for deploying the core RAT functionality and exfiltrating the stolen data, cementing the attacker's foothold on the victim's machine.
This incident serves as a critical reminder of the risks inherent in the open-source software supply chain. Developers must exercise extreme caution when installing packages, especially those from new or unverified publishers. Security best practices include verifying package publishers, scrutinizing `package.json` files for suspicious scripts (like `postinstall`), and using security tools that can scan dependencies for known malicious code. Organizations should enforce policies for software provenance and consider using private, curated registries to mitigate such threats.