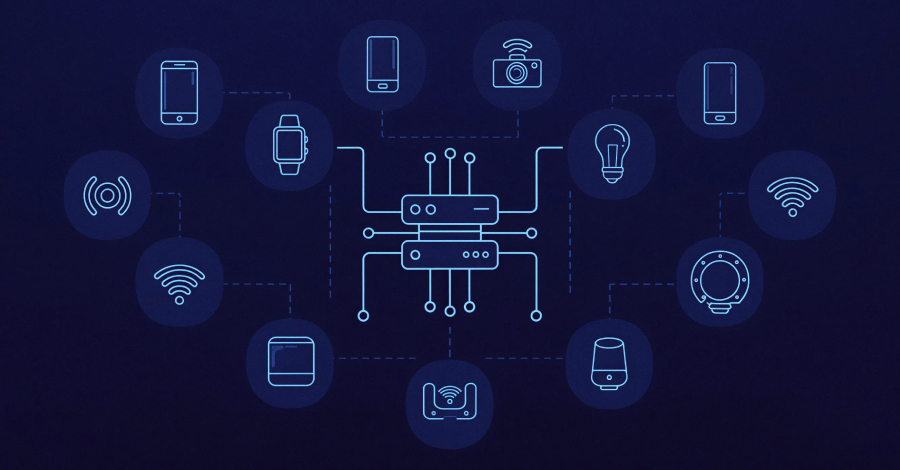
In a significant international law enforcement operation, the U.S. Department of Justice (DoJ) has successfully disrupted the command-and-control (C2) infrastructure of several prolific Internet of Things (IoT) botnets. The targeted botnets, identified as AISURU, Kimwolf, JackSkid, and Mossad, were responsible for launching some of the largest distributed denial-of-service (DDoS) attacks ever recorded. The operation, authorized by a U.S. court, involved coordinated efforts with authorities in Canada and Germany and received critical support from a coalition of leading private sector firms, including Akamai, Amazon Web Services, Cloudflare, Google, and PayPal.
According to the DoJ, these botnets executed global DDoS campaigns with staggering scale, including attacks measuring approximately 30 Terabits per second (Tbps). This aligns with a recent Cloudflare report attributing a record-breaking 31.4 Tbps attack in November 2025 to the AISURU/Kimwolf botnet. The same infrastructure was linked to a series of hyper-volumetric attacks averaging 3 billion packets per second (Bpps), 4 Tbps, and 54 million requests per second (Mrps). These attacks, though sometimes lasting mere seconds, represent a new frontier in volumetric assault capabilities, leveraging millions of compromised IoT devices to generate unprecedented traffic floods.
Investigations into the botnet operators have revealed key suspects. Independent security journalist Brian Krebs traced the Kimwolf administrator to a 23-year-old Canadian individual, Jacob Butler (aka "Dort"), who claims his old online persona was compromised and is being impersonated. Butler stated he struggles with autism and largely stays home to assist his mother. Another prime suspect is identified as a 15-year-old residing in Germany. As of this announcement, no arrests have been made public. The botnets' infrastructure primarily consisted of compromised, off-brand Android smart TVs and set-top boxes, with Kimwolf alone conscripting over 2 million Android devices, as first documented by QiAnXin's XLab in December 2025.
This takedown underscores the persistent and escalating threat posed by poorly secured IoT devices, which are easily weaponized into powerful botnets. The successful operation highlights the growing necessity for cross-border collaboration between law enforcement and the technology industry to dismantle cybercriminal infrastructure. For organizations worldwide, the incident serves as a critical reminder to implement robust DDoS mitigation strategies, maintain stringent device security hygiene, and assume that any internet-connected device is a potential vector for large-scale attacks.