EXCLUSIVE: U.S. CYBERSECURITY AGENCY SOUNDS ALARM AS IRANIAN HACKERS, IPHONE EXPLOIT KITS CONVERGE IN GLOBAL THREAT WAVE
The digital front lines are heating up. In an urgent directive, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has mandated federal agencies to patch five critical flaws by April 2026, branding them as actively weaponized in the wild. This isn't routine maintenance; it's a battlefield triage notice. The targets? Apple devices, Craft CMS, and Laravel frameworks—technologies embedded in daily life and critical infrastructure worldwide.
The core of this crisis is a multi-pronged assault. For Apple users, a sinister exploit kit dubbed "DarkSword" is leveraging three iOS vulnerabilities to deploy data-stealing malware like GHOSTBLADE. One flaw, CVE-2025-32432, was a secret zero-day exploited since February 2025, later hijacked to install crypto miners. Simultaneously, Iranian state hackers known as MuddyWater are exploiting a separate vulnerability, CVE-2025-54068, in a relentless cyber espionage campaign.
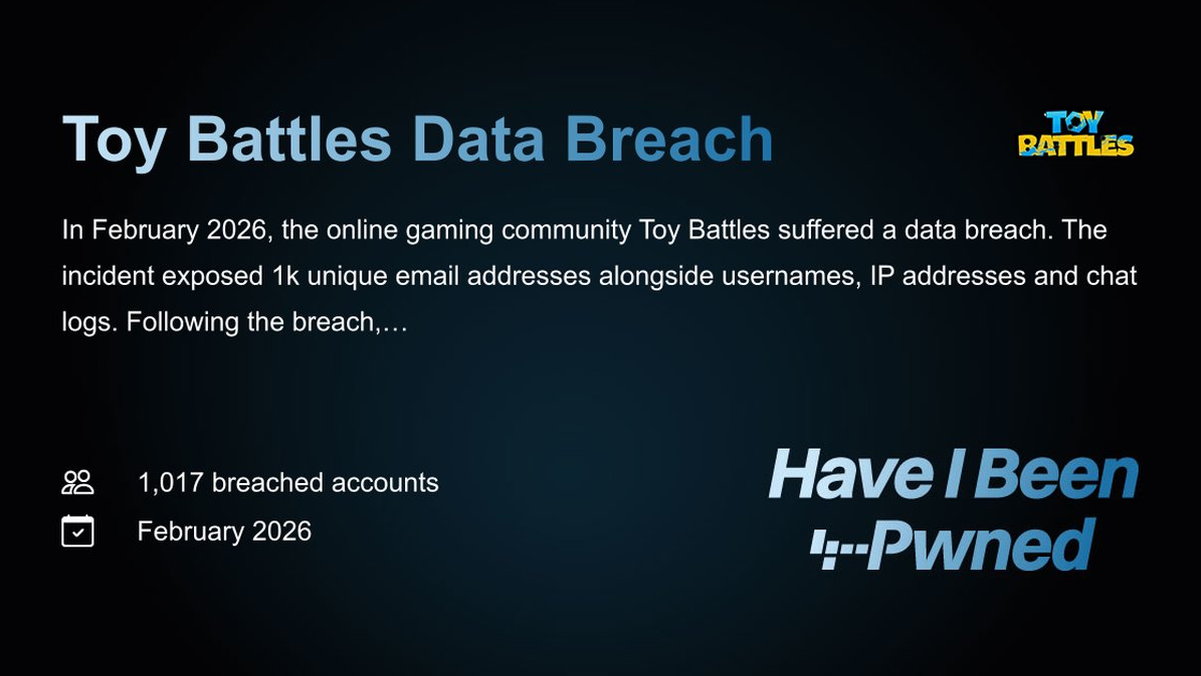
Security experts are sounding the alarm on the sophistication of these threats. "MuddyWater is no longer just a phishing operation," reveals a senior threat analyst from a top cybersecurity firm. "They are deploying AI-enhanced malware with anti-analysis techniques for long-term, silent persistence. Their custom platform automates mass phishing at an industrial scale, making every employee a potential entry point for a catastrophic data breach."
This matters because the battlefield is your pocket and your office. The Apple exploits threaten personal privacy and corporate data on millions of devices, while MuddyWater's consistent targeting of energy, maritime, and finance sectors puts global stability at risk. Their adoption of ransomware tactics, like the DarkBit persona used against a major Israeli institute, shows a blurring line between espionage and outright disruption.
We predict a surge in copycat campaigns and commodity ransomware gangs weaponizing these now-public exploits, turning targeted attacks into a widespread free-for-all. The mandated 2026 patch deadline feels like a lifetime in internet years—and the hackers know it.
The clock is ticking. Patch or perish.