A sophisticated cyber attack targeting the Microsoft corporate environment of Stryker Corporation, a leading medical technology company, successfully wiped data from employee devices without deploying any traditional malware. According to a detailed report from Google's Threat Analysis Group (TAG), the threat actors orchestrated a complex intrusion that leveraged stolen credentials and legitimate administrative tools to carry out destructive actions. This incident underscores a growing trend where attackers forgo malicious software in favor of "living-off-the-land" techniques, using an organization's own trusted systems against it to evade detection.
The attack chain began with the compromise of a corporate user's credentials, likely obtained through phishing or another form of initial access brokerage. The adversaries used these credentials to authenticate into Stryker's Microsoft Entra ID (formerly Azure AD) environment. Once inside, they performed extensive reconnaissance, enumerating user accounts, groups, and devices. The attackers then escalated their privileges by adding a compromised account to highly privileged administrative roles, specifically the "Global Administrator" and "Intune Administrator" roles within Microsoft Intune, the cloud-based endpoint management service.
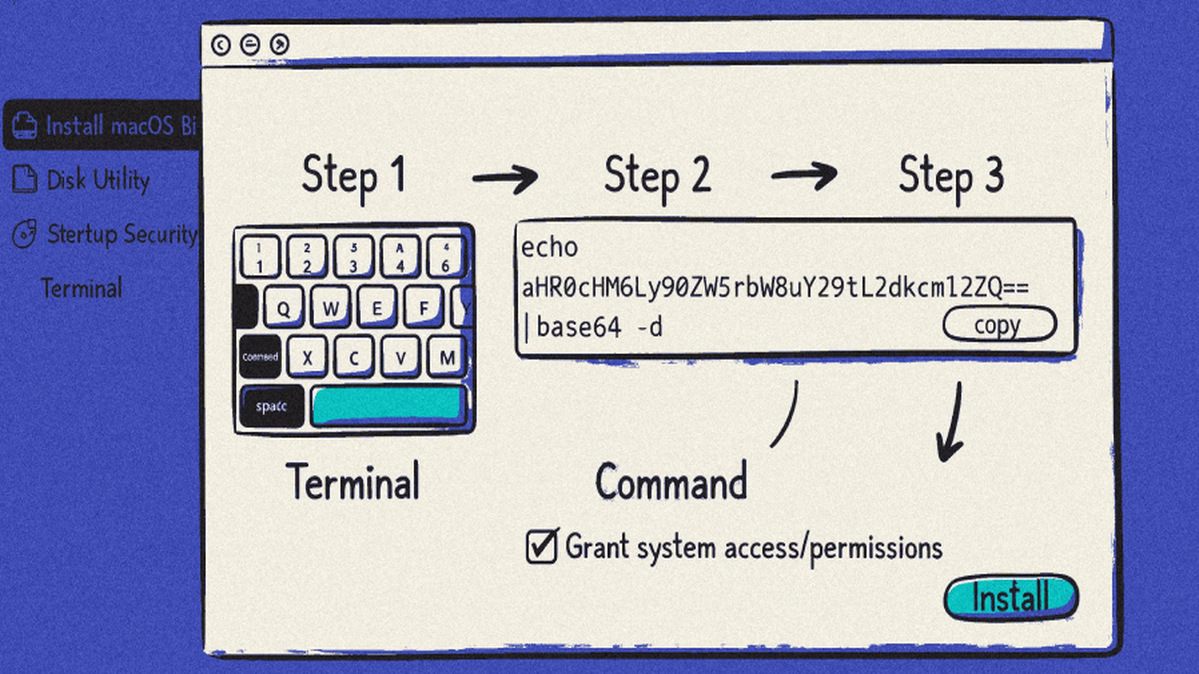
With full administrative control over Microsoft Intune, the attackers executed the destructive phase of the operation. They abused the legitimate "Remote Help" feature and other Intune functionalities to push a series of malicious configurations to enrolled corporate devices, primarily Windows laptops. These configurations included a "Device Restriction" policy that disabled critical security features like Microsoft Defender, and a script that forced a factory reset, irrecoverably wiping the device's primary drive. Because these actions were performed through official, trusted administrative channels and tools, they bypassed traditional antivirus and endpoint detection solutions that look for signature-based malware.
The attack highlights critical security gaps in modern, cloud-centric IT environments. Over-provisioning of administrative privileges, lack of robust multi-factor authentication (MFA) enforcement, and insufficient monitoring of administrative tool usage created a perfect storm. Security teams must shift their focus from solely hunting for malware to monitoring for anomalous use of legitimate administrative functions. Key mitigations include enforcing phishing-resistant MFA for all privileged accounts, implementing strict conditional access policies, regularly auditing role assignments, and employing advanced detection for unusual administrative activity in tools like Intune and Entra ID.
This incident serves as a stark warning for organizations worldwide. The convergence of compromised identities and the immense power of cloud administration consoles presents a severe risk. Defenders must assume that attackers are already inside their perimeter and focus on hardening identity systems, segmenting administrative access, and ensuring that the ability to perform destructive actions like remote wipes is tightly controlled and audited. The line between legitimate tool and weapon has blurred, requiring a fundamental rethink of cybersecurity postures in the age of cloud and identity-centric attacks.