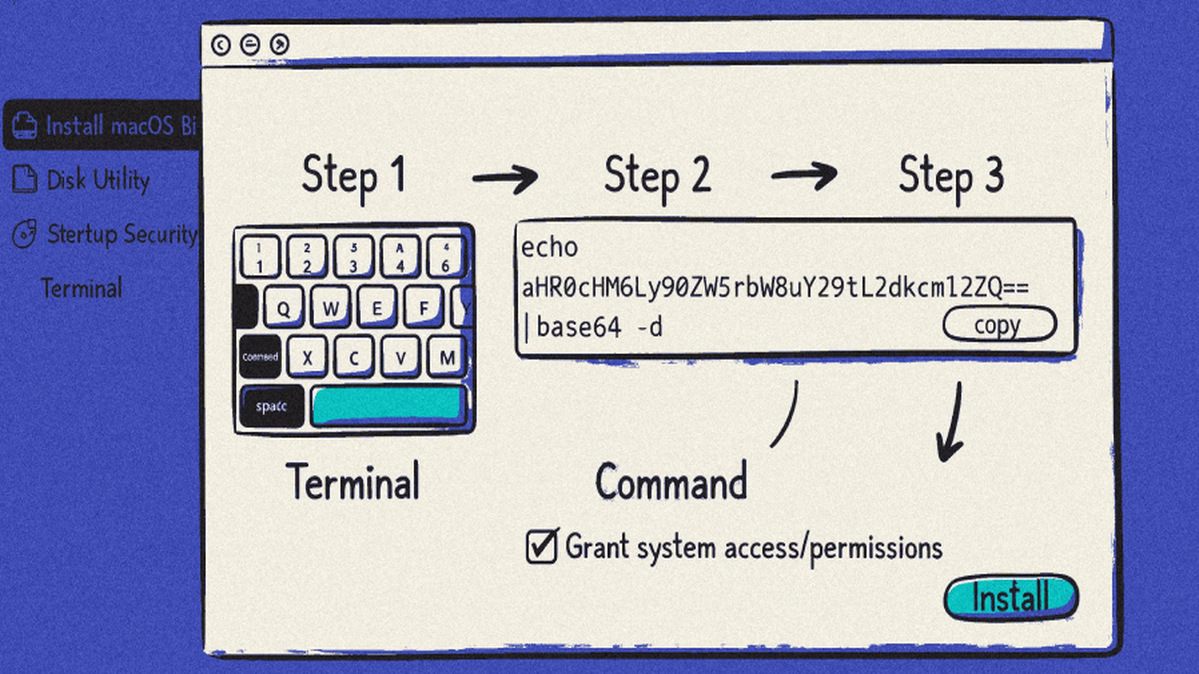
Cybersecurity researchers from Sophos have uncovered a series of three distinct "ClickFix" campaigns actively distributing a macOS information stealer known as MacSync. These campaigns cleverly masquerade as installation guides for popular AI-powered developer tools, such as Anthropic's Claude Code, to deceive users. The attacks are notable for their complete reliance on social engineering, eschewing traditional software exploits. Instead, they manipulate users into manually copying and executing malicious terminal commands, a tactic that proves highly effective against individuals who may not grasp the severe risks of running obfuscated commands from an untrusted source.
The operational mechanics of the attack are methodical. Once a user is lured to a fraudulent tutorial page hosted on legitimate platforms like Cloudflare Pages, Squarespace, or Tencent EdgeOne, they are instructed to run a specific command in the macOS Terminal. This shell script then contacts a hard-coded command-and-control server to retrieve the final payload—an AppleScript-based infostealer. Concurrently, the script takes steps to cover its tracks and remove evidence of the intrusion. The MacSync stealer is a potent threat, capable of harvesting a vast array of sensitive data from infected Macs, including stored credentials, personal files, the entire keychain database, and cryptocurrency wallet seed phrases.
This campaign represents a significant evolution in social engineering tactics. As noted by Sophos researchers Jagadeesh Chandraiah, Tonmoy Jitu, Dmitry Samosseiko, and Matt Wixey, the threat actors are weaponizing the inherent trust users place in conversations about and tutorials for generative AI tools like ChatGPT. By adapting their methods to bypass security software that focuses on exploit detection, they maintain a step ahead of defenders. The emergence of a new variant in the most recent campaign suggests the malware developers are continuously refining their code to counteract operating system security enhancements and maintain the stealer's effectiveness.
The persistence and adaptation of these ClickFix campaigns underscore a troubling trend. Initially flagged by Jamf Threat Labs in December 2025, their continued operation indicates a successful model for threat actors. Sophos warns that future evolution will likely involve further refinements to these social engineering lures. For users, the primary defense is heightened skepticism: never run terminal commands from unverified sources, especially those promising easy access to coveted AI or developer tools. Organizations should reinforce security awareness training, emphasizing that legitimate software never requires the execution of obscure, copied-and-pasted shell commands.