EXCLUSIVE: GLASSWORM SUPPLY-CHAIN ATTACK EXPLOITS TRUST, HIJACKS 72 DEVELOPER TOOLS IN MAJOR ESCALATION
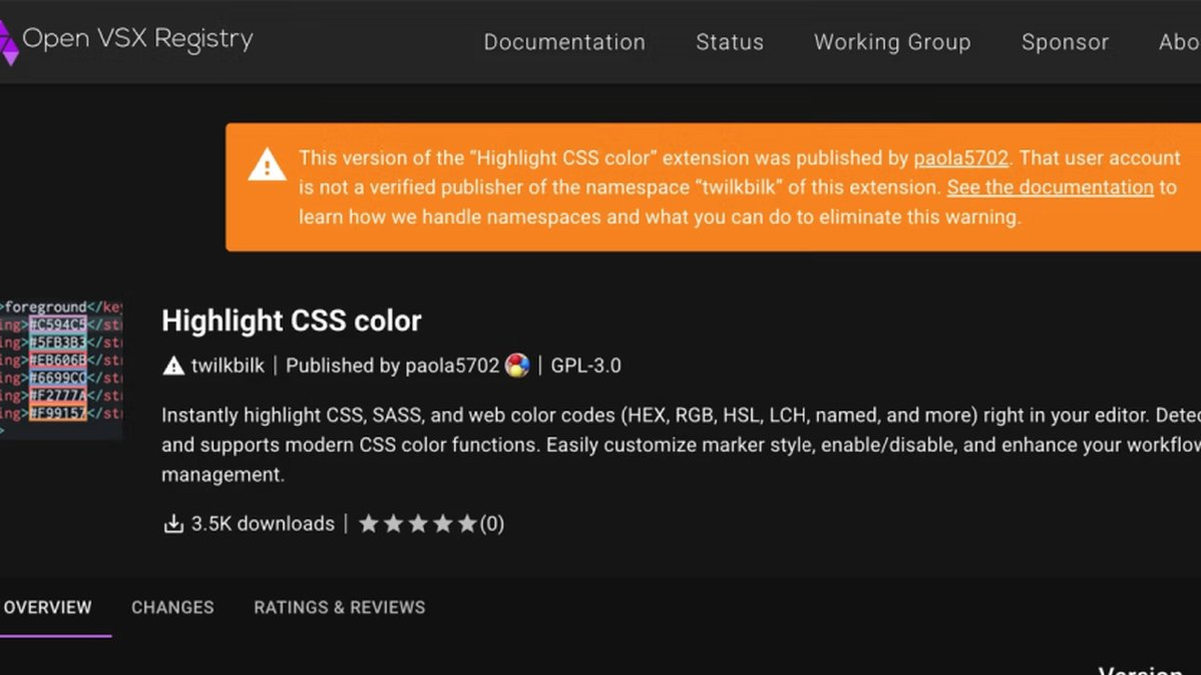
A critical software supply chain attack has dramatically evolved, weaponizing the very trust developers place in their tools. Cybersecurity researchers are sounding the alarm on a new, highly sophisticated phase of the GlassWorm campaign, which has now compromised at least 72 extensions on the Open VSX registry. This represents a "significant escalation" in malware propagation, directly targeting the global developer community through mimicked linters, code formatters, and AI-powered assistant utilities.
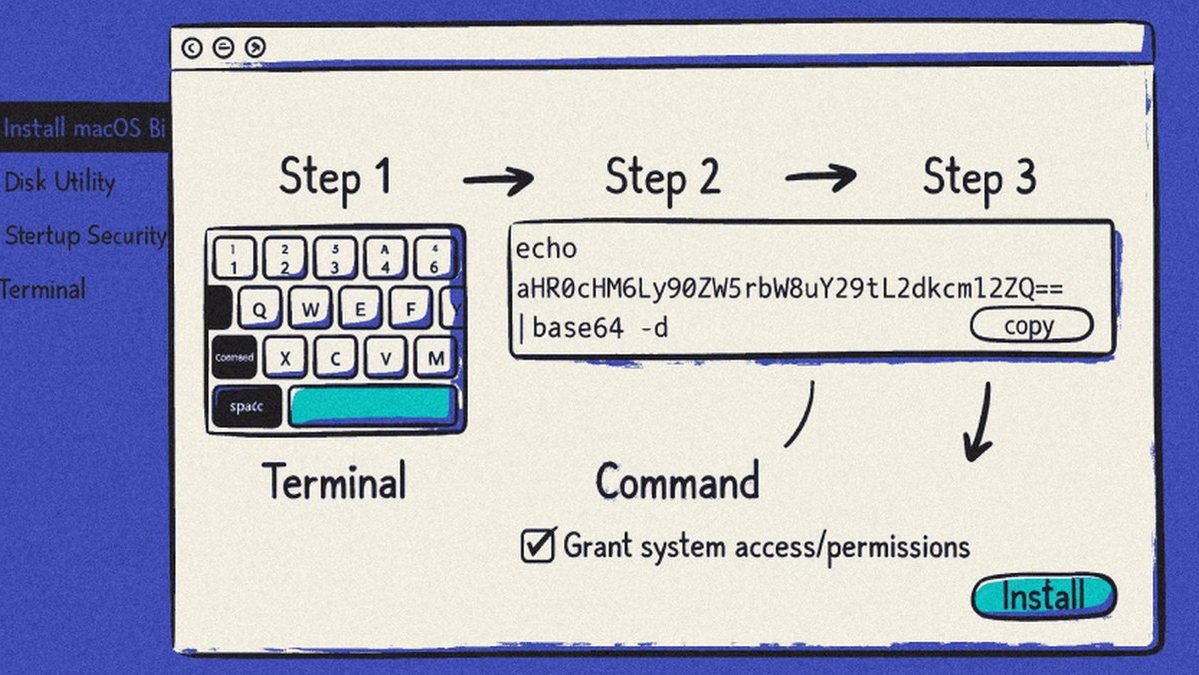
The core of this data breach lies in a devious abuse of trust. Threat actors are no longer just uploading blatantly malicious extensions. Instead, they are uploading seemingly benign packages that later, via updates, silently pull in separate GlassWorm-linked extensions as dependencies. This transitive delivery method means a developer's environment can be compromised only after initial trust in a harmless-looking tool is established. It’s a masterclass in social engineering within a technical ecosystem.
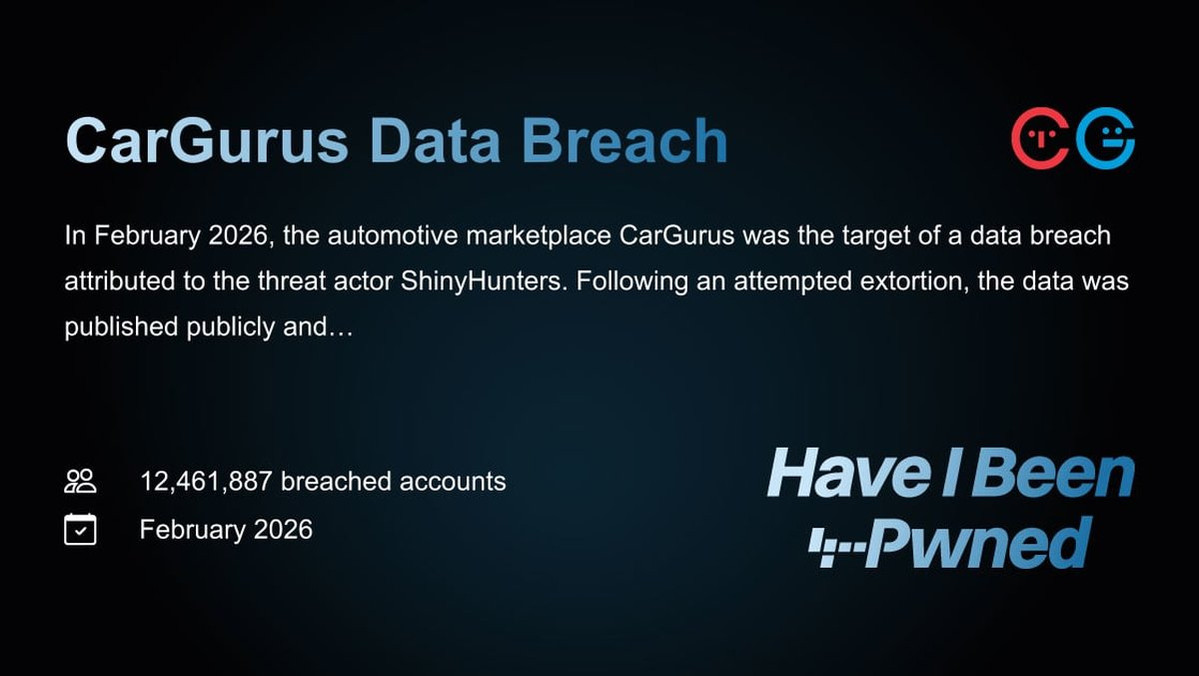
This campaign is squarely aimed at theft and resource hijacking. GlassWorm malware is designed to steal secrets, drain cryptocurrency wallets, and turn infected systems into proxies for further criminal activity. The latest iteration uses heavy obfuscation and rotates Solana wallets for command-and-control, leveraging blockchain security complexities to evade detection. It also checks for Russian system locales to avoid infecting certain regions, a hallmark of its previous operations.
"Threat actors are exploiting fundamental trust mechanisms in developer ecosystems," explains a senior analyst at a supply chain security firm. "By abusing extension dependencies, they've created a phishing scheme on an industrial scale. One installed utility becomes a silent installer for a catastrophic payload. This is a severe vulnerability in the process of trust establishment."
Every developer using open-source registries is now on the front line. This isn't just about a single malware infection; it's about the integrity of the entire software development lifecycle. A single compromised system can lead to massive intellectual property theft, crippling ransomware deployment, or the loss of crypto assets. The exploit of these extension relationships mirrors tactics long seen in npm, proving no ecosystem is safe.
We predict this sophisticated dependency confusion tactic will be copied rapidly by other cybercriminal groups, leading to a wave of similar supply chain attacks across all open-source platforms in the coming months. The zero-day for trust has been exploited.
The toolchain you rely on is now a potential Trojan horse.