A critical security vulnerability has been identified in Docker Engine, posing a significant risk to containerized environments. Tracked as CVE-2026-34040 with a high CVSS score of 8.8, this flaw allows a malicious actor to bypass configured authorization (AuthZ) plugins under specific conditions. This bypass could enable an attacker to execute unauthorized Docker commands, potentially leading to a full compromise of the underlying host system. The vulnerability represents a regression, as it stems from an incomplete fix for CVE-2024-41110, a maximum-severity flaw in the same authorization plugin mechanism that was disclosed in July 2024.
The core of the issue lies in the interaction between Docker's API request processing and its authorization plugin framework. Authorization plugins are designed to intercept and validate API requests before they are executed, enforcing custom security policies. The incomplete patch for the previous vulnerability left a logical gap in this validation chain. Under a specific, yet-to-be-publicly-detailed set of circumstances, an attacker can craft API requests that evade the AuthZ plugin's inspection entirely. This allows commands that should be blocked or restricted to proceed directly to the Docker daemon for execution.
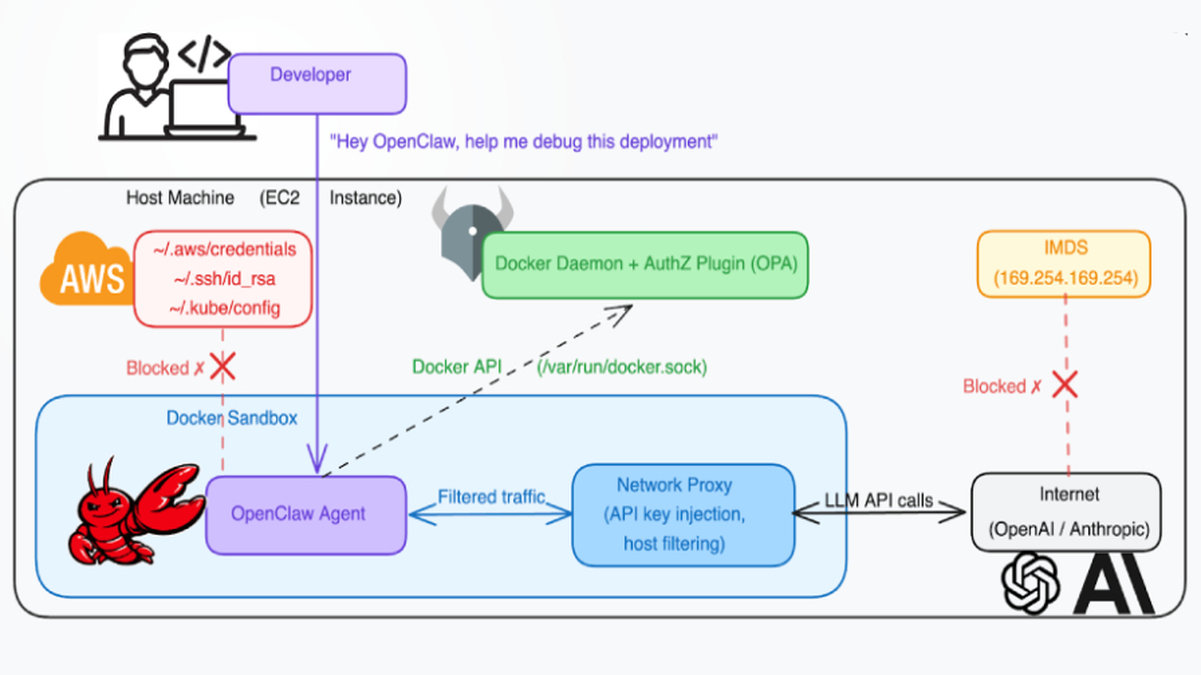
The implications of a successful exploit are severe. By bypassing authorization controls, an attacker with initial access to the Docker API could escalate privileges within the container environment. The most critical outcome would be the ability to execute commands on the host operating system itself, often achieved by mounting the host's filesystem into a new container with elevated privileges. This provides a direct pathway to steal sensitive data, deploy persistent malware, or pivot to attack other systems on the network. Organizations using Docker Engine in multi-tenant environments or where the Docker API is exposed to some level of untrusted access are at heightened risk.
Docker has released patches to fully address this vulnerability. Security teams are urged to prioritize updating all Docker Engine installations to the latest patched versions immediately. As a critical mitigation step, administrators should also review and restrict access to the Docker daemon socket and API, ensuring it is not exposed to unauthorized networks or users. Furthermore, a comprehensive review of container and host logs for any anomalous activity following the disclosure of CVE-2024-41110 is recommended, as attempted exploits against the original flaw may have leveraged the same incomplete patch vector. This incident underscores the critical importance of thorough regression testing when patching complex security mechanisms in core infrastructure software.