EXCLUSIVE: THE EDR KILLER ECOSYSTEM EXPOSED — YOUR CYBERSECURITY IS UNDER SIEGE
A new front has opened in the digital arms race, and your corporate networks are the battlefield. ESET researchers have pulled back the curtain on the massive, industrialized ecosystem of "EDR killers," tools that are now a PREDICTABLE stage in nearly every major ransomware attack. This isn't about a single vulnerability; it's about a systematic playbook to dismantle your defenses.
The core fact is terrifying in its simplicity. Attackers first gain a foothold, then deploy these specialized tools to disable Endpoint Detection and Response software. Only after your digital guards are blindfolded do they launch the final encryptor. While abusing vulnerable drivers is common, the research reveals a surge in driverless techniques and the abuse of legitimate security utilities. Nearly 90 distinct EDR killers are actively tracked in the wild, forming a commercialized toolkit for cybercriminals.
One unnamed senior threat intelligence analyst told us, "The consistency is the real threat. These tools behave predictably, which makes them the go-to choice for ransomware affiliates. The focus on drivers has been a distraction. The real story is the operational playbook." This shift means old attribution models are broken. Groups frequently swap and reuse driver code across unrelated attacks, making forensic finger-pointing dangerously unreliable.
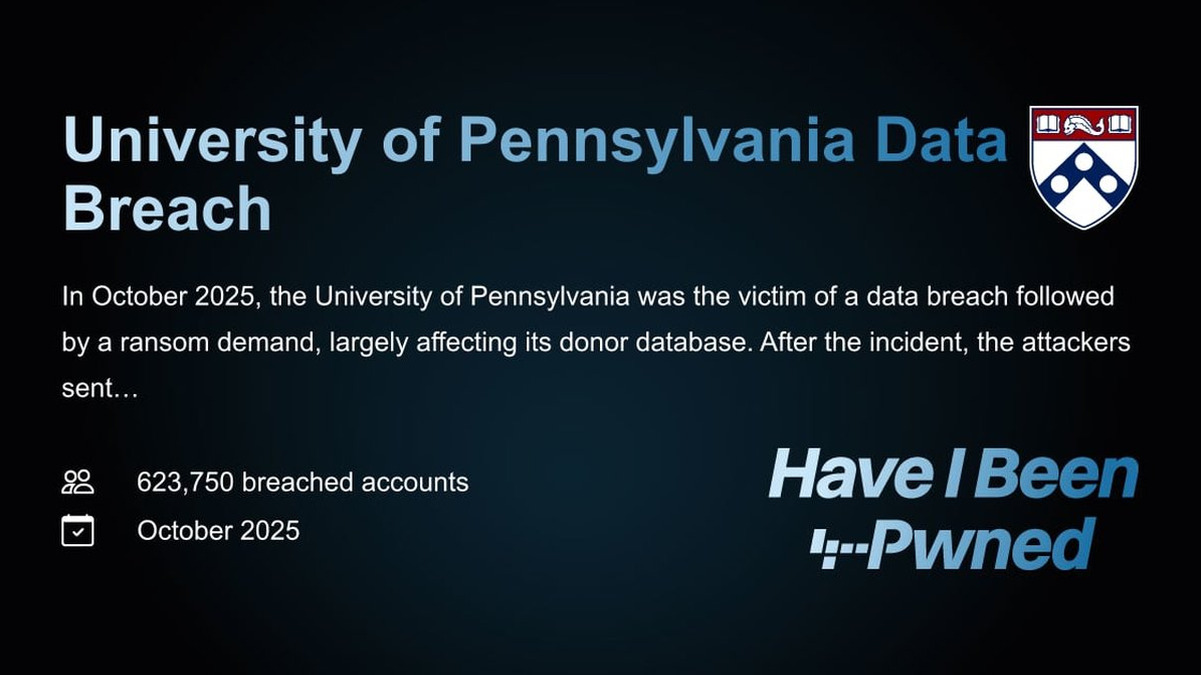
You should care because this turns a technical weakness into a business-ending event. The chain is clear: a phishing email leads to an initial exploit, which leads to an EDR killer neutralizing your security, which enables a catastrophic data breach. Your last line of defense is being systematically eliminated before the main event even begins.
We predict a sharp rise in fileless and driverless EDR killing techniques, pushing further into kernel-level attacks that tools struggle to even see. The integration of crypto payment systems and discussions of blockchain security for command channels will only make these campaigns harder to trace and disrupt.
The malware is the finale; killing your EDR is the main act. Are you watching for the right threat?