NORTH KOREAN HACKERS INFILTRATE CRITICAL CODE FOR WEEKS IN BOLD SUPPLY CHAIN ATTACK
A brazen, state-sponsored cyberattack has successfully hijacked one of the internet's most fundamental open-source projects. Security experts confirm this was no smash-and-grab operation but a patient, weeks-long campaign of social engineering, culminating in a devastating software supply chain compromise. The target: the ubiquitous Axios project, used by millions of developers worldwide to connect applications to the web.
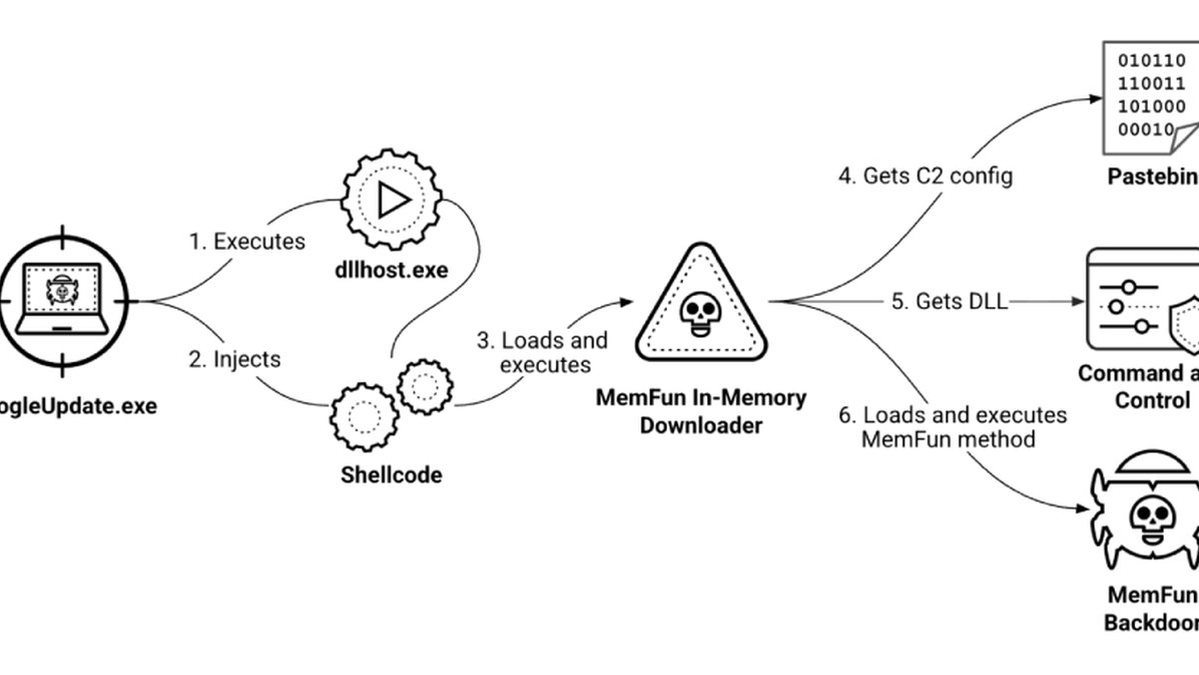
The attack's sophistication is a chilling escalation. Posing as a legitimate company, North Korean operatives built a complete fake corporate front, including a Slack workspace and employee profiles, to lure the project's maintainer. After establishing trust, they invited him to a web meeting, tricking him into downloading malware disguised as necessary software. This granted them remote access to his system—a classic move often used to steal cryptocurrency from high-value targets.
This incident exposes a critical vulnerability in our digital infrastructure: the trusted maintainers of essential open-source code are now prime targets. "This is a textbook APT operation," an unnamed senior cybersecurity analyst told us. "They didn't just exploit a zero-day; they engineered a human vulnerability. The phishing was flawless, the pretext airtight. This bypasses all traditional blockchain security and network defenses."
Every developer and company using open-source dependencies should be on HIGH ALERT. This wasn't a random data breach; it was a calculated attempt to plant malware directly into the software supply chain, potentially creating a backdoor into millions of applications. The malicious packages were live for hours, leaving a window for widespread infection and future ransomware deployment.
We predict this attack will trigger a massive review of maintainer security protocols across all major open-source platforms. The era of trusting code based solely on its source is OVER. The frontline of cybersecurity has shifted from the server room to the developer's direct messages.
If they can hijack Axios, no project is safe.