EXCLUSIVE: CHINESE CYBER ESPIONAGE UNIT INFILTRATES ASEAN MILITARIES IN YEARS-LONG ZERO-DAY CAMPAIGN
A clandestine Chinese cyber espionage operation, tracked as CL-STA-1087, has successfully breached multiple Southeast Asian military networks in a campaign of surgical precision dating to 2020. This is not a smash-and-grab data breach; this is a state-sponsored intelligence harvest targeting the very core of regional defense. The threat actors deployed custom malware, including the AppleChris backdoor and MemFun, to maintain persistent, undetected access for years, searching exclusively for files on military strategy, Western collaborations, and advanced C4I systems.
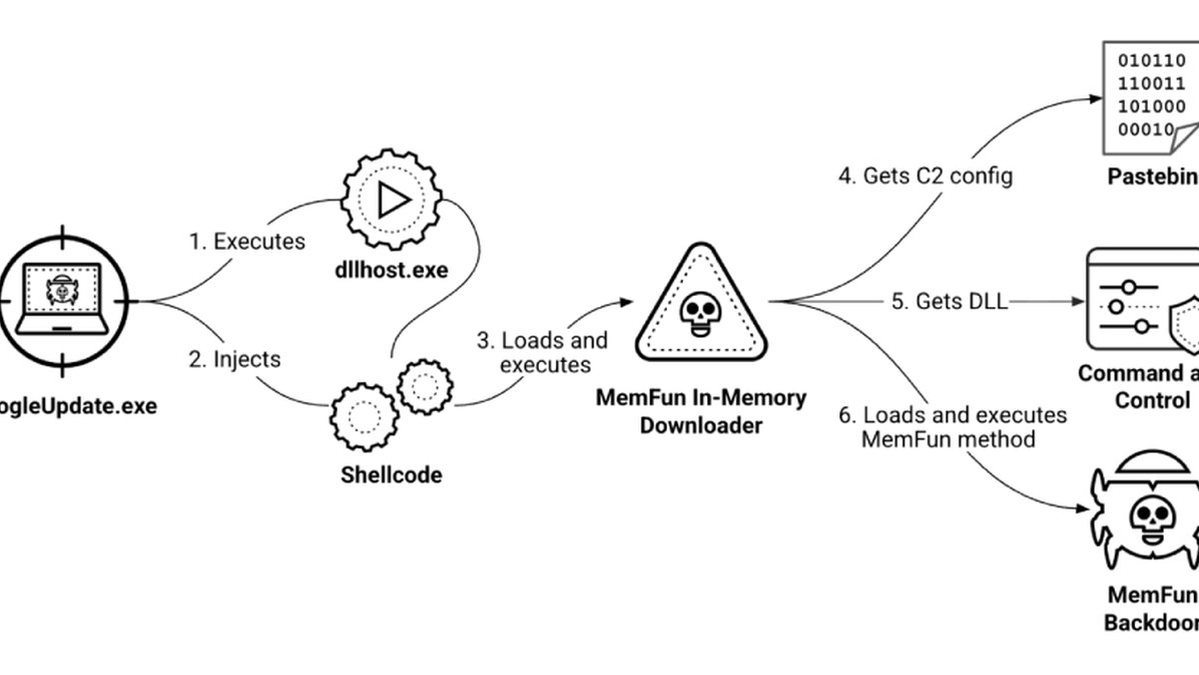
The operation's sophistication is a masterclass in cyber warfare tradecraft. The attackers used strategic operational patience, often letting scripts sleep for hours before activating. Their malware employed a cunning evasion technique, using Pastebin and Dropbox as dead drop resolvers to fetch command-and-control server addresses, effectively hiding in plain sight. The initial access vector remains a mystery, pointing to a potentially undisclosed vulnerability or a highly effective phishing scheme.
"These are not criminal ransomware gangs looking for a crypto payout. This is a nation-state executing a long-term intelligence mission," a senior cybersecurity analyst familiar with the investigation told us. "The focus on specific military documents shows this campaign was about mapping capabilities and alliances, not financial gain. The use of shared public services for C2 is a stark reminder that blockchain security for communications isn't just for crypto; it's a frontline defense need."
This should be a five-alarm fire for every government in the region and their Western partners. The stolen intelligence on joint military exercises and operational assessments doesn't just compromise one nation; it exposes collective security postures. Every piece of pilfered data on command structures and weapons systems alters the strategic balance of power.
We predict this cluster's activities are merely the visible tip of the spear. The tools and techniques will evolve, targeting critical infrastructure and leveraging zero-day exploits with increasing frequency. The era of cyber espionage as a silent, persistent shadow war is over; it's now a decisive front in geopolitical conflict.
Your military secrets are already on a server you don't control.