The cybersecurity landscape is witnessing a dangerous convergence of threats as the fallout from the TeamPCP supply chain attack campaign expands. Initially a focused operation, the incident has escalated into a murky, multi-actor crisis. Organizations are now disclosing breaches linked to the initial compromise, while notorious threat groups ShinyHunters and Lapsus$ are inserting themselves into the situation. This involvement, characterized by claims of credit and potential data theft, is significantly complicating incident response and attribution, leaving victim enterprises navigating a perilous and confused threat environment.
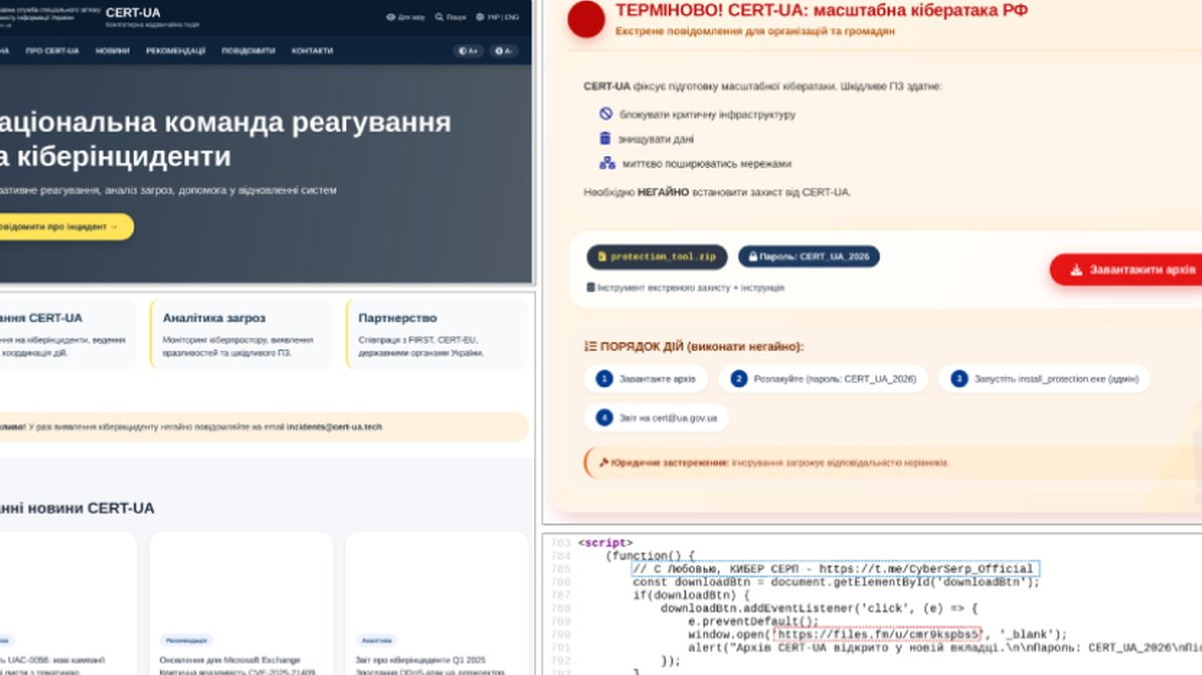
The core of the crisis remains the supply chain attack attributed to TeamPCP. By compromising a trusted software vendor or component, attackers can achieve a "force multiplier" effect, breaching dozens or hundreds of downstream customers in a single operation. As these victims—often managed service providers (MSPs) or IT firms—identify the intrusion, the public disclosure of incidents has created a target-rich environment. This has drawn the attention of other financially motivated cybercriminal syndicates who see an opportunity for exploitation.
Enter ShinyHunters and Lapsus$, two groups with proven track records of high-profile data theft and extortion. Their involvement manifests in several disruptive ways: claiming responsibility for breaches they may not have originally executed, exfiltrating data from already-compromised networks, and potentially selling or leaking that data independently. This behavior transforms a single incident into a persistent threat, as victim data may be traded across multiple criminal forums or leaked in stages, maximizing extortion pressure and prolonging the operational impact.
For enterprises, this infighting and overlapping claims create a nightmare scenario for threat intelligence and recovery. The primary imperative remains containing the initial supply chain compromise and ejecting the adversary. However, security teams must now also assume that multiple distinct threat actors may have accessed their networks or could be in possession of their data. This necessitates broader password resets, more extensive forensic analysis, and complex communications to customers and regulators regarding the scope of data exposure. The blurring of attribution also hampers law enforcement efforts and makes strategic countermeasures more difficult to implement.
Ultimately, the TeamPCP saga underscores a grim evolution in the cybercrime ecosystem: major attacks are no longer isolated events but become catalysts for secondary exploitation. The "blast radius" of an initial compromise is no longer limited to its direct victims but expands as other actors rush to capitalize on the chaos. This trend demands that organizations move beyond planning for a single incident response and instead adopt a posture of resilience that assumes continued pressure from multiple angles, emphasizing rapid detection, comprehensive credential cycling, and clear crisis communication protocols in the wake of any breach.