EXCLUSIVE: MILLIONS TARGETED IN BRAZEN CYBER SPOOF AS HACKERS IMPERSONATE UKRAINE'S TOP SECURITY AGENCY
In a stunning act of digital audacity, threat actors have impersonated Ukraine's own Computer Emergency Response Team (CERT-UA) to launch a massive phishing campaign, pushing malware to over one million email inboxes. This is not just another data breach; it's a targeted strike designed to shatter trust in the very institutions built to stop such attacks. The campaign, active in late March, represents a dangerous escalation in information warfare.
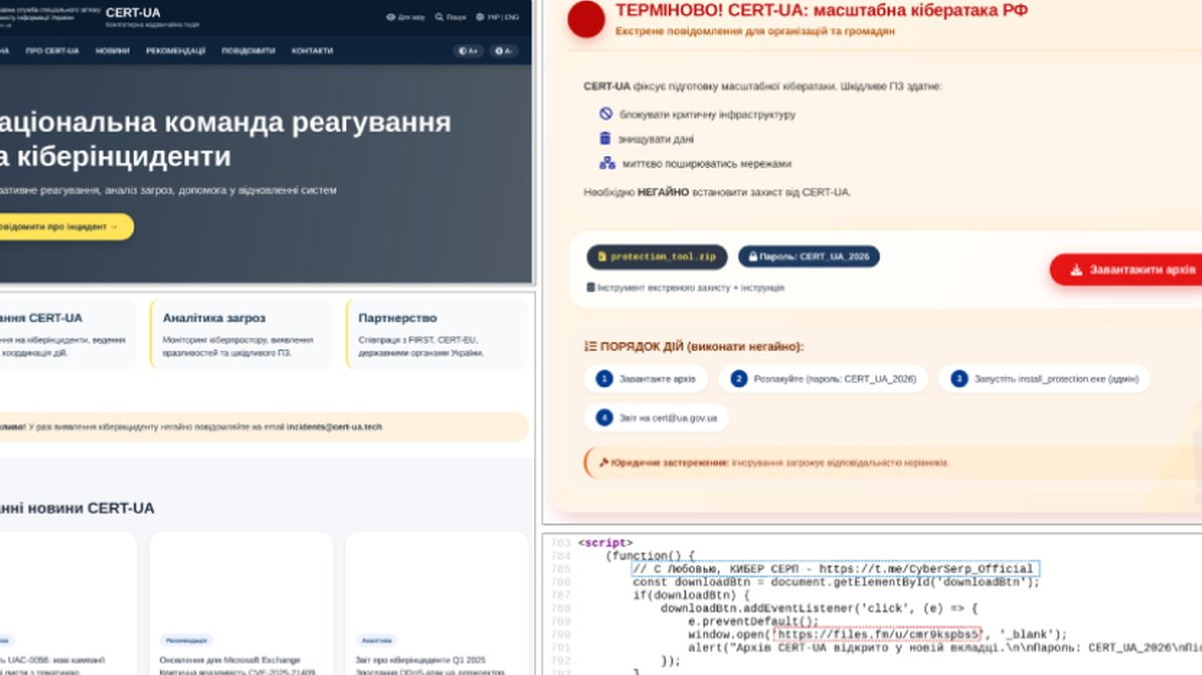
The core facts are alarming. The group, tracked as UAC-0255, sent emails posing as official CERT-UA communications. The lure was a password-protected ZIP archive, a common trick to evade automated security scanners. Inside lurked AGEWHEEZE, a powerful remote administration tool that, once installed, gives attackers complete control over a victim's system. This exploit creates an open door for ransomware deployment, data theft, and further network penetration.
Cybersecurity experts are sounding the alarm on the sophistication of this operation. "This campaign exploits a fundamental vulnerability: human trust in authority," stated one analyst familiar with the investigation. "By spoofing a national cybersecurity agency, they've crafted a near-perfect phishing lure. It bypasses technical controls by preying on psychology. The use of a crypto-locked archive shows deliberate planning to avoid detection."
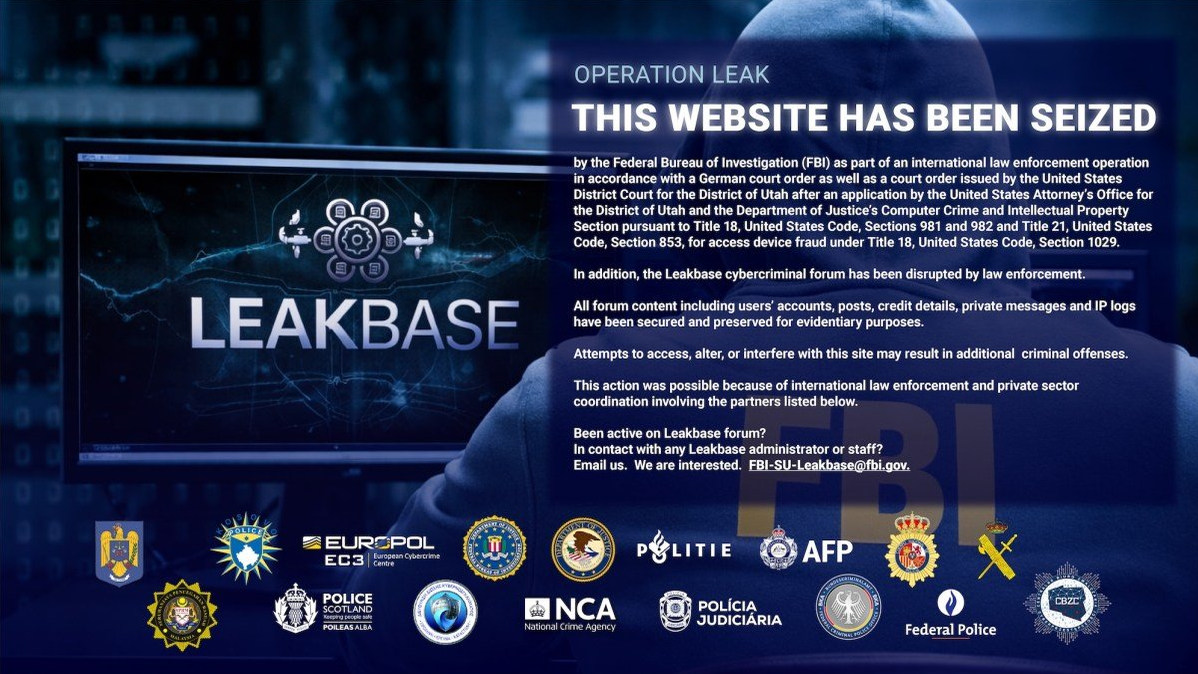
Every organization and individual is now a target. This incident proves that no entity, not even a leading CERT, is safe from impersonation. Your vigilance is the last line of defense. The AGEWHEEZE malware can lead to catastrophic data breaches, with stolen information potentially sold on darknet markets or used to enable crypto-based ransom demands. This also raises urgent questions about blockchain security and the traceability of such transactions.
We predict this will become a blueprint. State-aligned and criminal groups will increasingly mimic trusted sources—governments, banks, crisis responders—to deliver zero-day exploits and malware. The era of simple phishing scams is over; we are now in the age of the false flag cyber operation.
When the defenders themselves are forged into the weapon, where does safety lie?