EXCLUSIVE: THE CYBER SHADOW WAR TARGETING NUCLEAR CONTROL SYSTEMS
While bombs fall on physical infrastructure, a far more insidious threat is being deployed in the digital shadows. The real danger to nuclear facilities is no longer just the kinetic strike, but a coordinated campaign of CYBER-ATTACKS designed to cripple critical safety systems. This is a silent war where a single line of malicious code could be more devastating than any bunker-buster bomb.
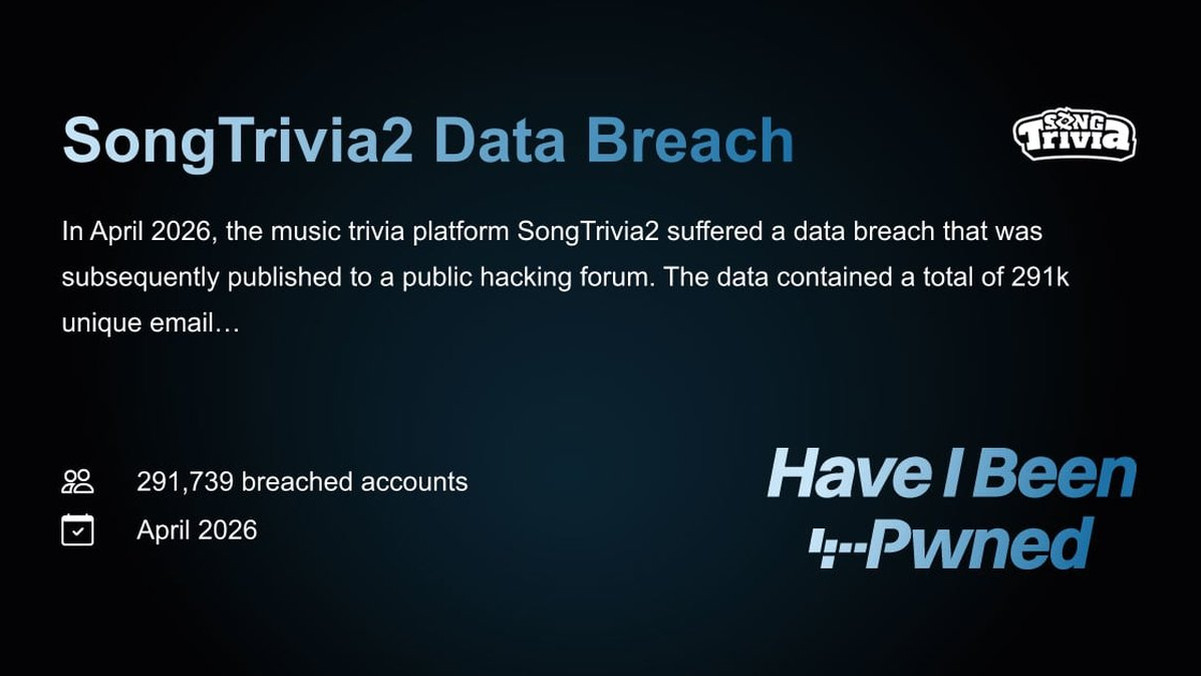
Security analysts confirm a terrifying shift in tactics. Adversaries are no longer just aiming missiles at reactors; they are deploying advanced MALWARE designed to infiltrate Industrial Control Systems (ICS). The goal? To lay dormant and create a catastrophic DATA BREACH of safety protocols, waiting for the precise moment to trigger a shutdown or, worse, a cover-up of a radiological event. This isn't speculation; it's the new battlefield.
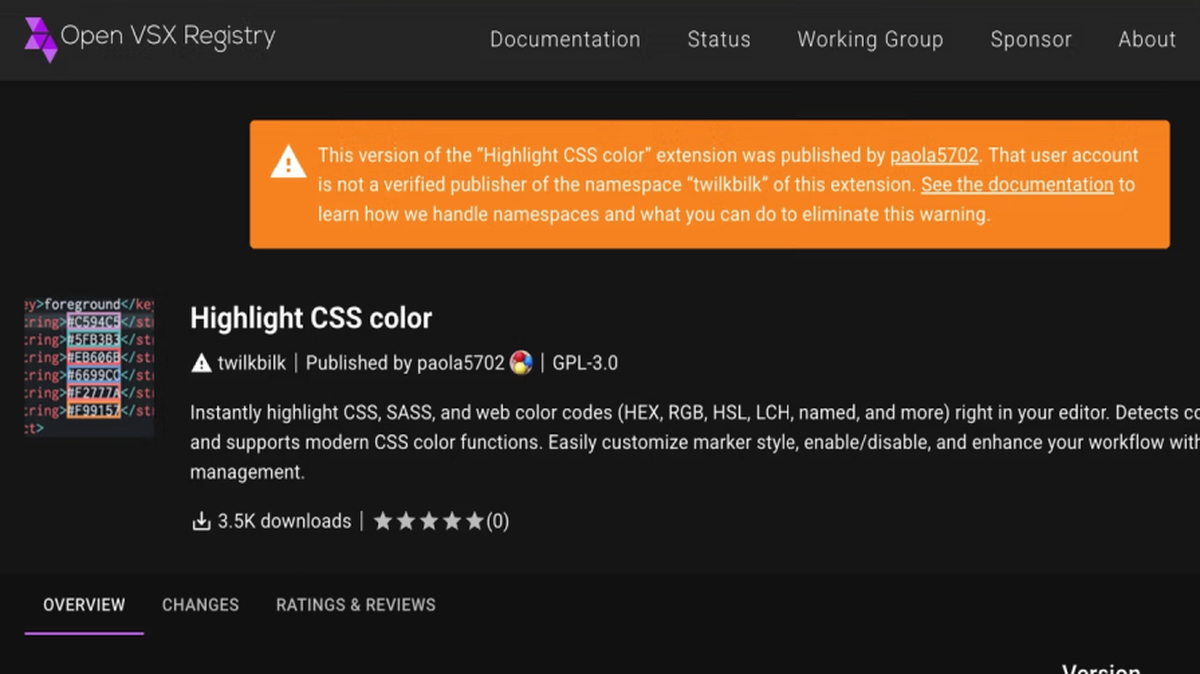
A ZERO-DAY VULNERABILITY in a plant's outdated firewall is a golden ticket. Experts we spoke to, who cannot be named due to the sensitivity of their work, state that state-sponsored groups are actively hunting for these flaws. "They use sophisticated PHISHING campaigns against engineers to gain initial access," one source revealed. "Once inside, they can deploy an EXPLOIT that gives them total control of cooling or containment systems. The risk of a digital-induced meltdown is now our primary concern."
Why should you care? Because a successful cyber-attack on a nuclear facility is a RANSOMWARE event with apocalyptic stakes. Attackers could hold entire safety systems hostage, demanding payment in untraceable CRYPTO. But this goes beyond money. It's about demonstrating that BLOCKOCKAIN SECURITY for national infrastructure is a myth and that our most dangerous sites are perilously exposed.
We predict the next major radiological incident will not be caused by a bomb, but by a keyboard. The world is fixated on explosions, while the real fuse is being lit in the code.
The fallout from a digital attack knows no borders.