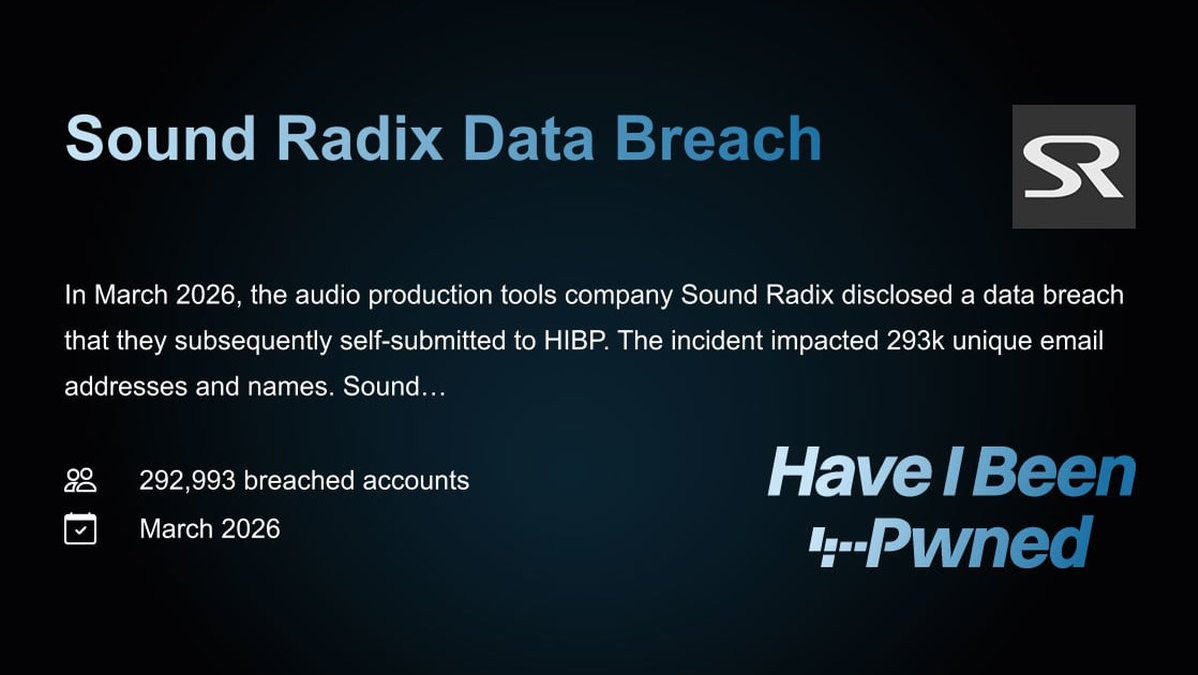
AI-POWERED PHISHING FACTORIES NOW OPERATIONAL: BUBBLE APPS BECOME THE ULTIMATE CORPORATE TRAP
A chilling new wave of sophisticated PHISHING attacks is flooding corporate inboxes, and they are being built not in dark web forums, but on a popular, legitimate AI app-building platform. Investigative sources confirm cybercriminals are now weaponizing Bubble, a no-code development tool, to generate deceptive web applications designed for one purpose: stealing high-value corporate credentials in a massive DATA BREACH campaign. This isn't a lone wolf attack; this is industrialized fraud.
The core vulnerability is breathtaking in its simplicity. Attackers use Bubble's AI to visually design and instantly generate a polished, functional web app. This app is then hosted on Bubble's own infrastructure, granting it a pristine, legitimate-looking URL ending in bubble.io. The malicious EXPLOIT is hidden within. When a target employee clicks the link from a phishing email, the app executes an automated redirect to the final credential-harvesting page. Security filters are being completely bypassed because they see a trusted domain, not a known malicious link.
This method solves multiple historic problems for ransomware gangs. Direct malicious links get blocked. QR codes cause friction. But a link to a custom, AI-generated web app? It sails through. One unnamed threat intelligence expert stated, "This is a paradigm shift. They've outsourced their development to a certified platform. The URL is clean. For defenders, this is a nightmare ZERO-DAY in trust, not just in code. It completely redefines the supply chain for phishing kits."
Every employee with a corporate login is now a target. The stakes are nothing less than total network compromise, leading directly to ransomware deployment and extortion demands paid in untraceable CRYPTO. This attack vector proves that modern cybersecurity must now scrutinize the very tools that power our digital economy. Blockchain security principles of immutable transaction logs are needed for app generation audits.
We predict a 300% surge in these attacks within the quarter as this technique is packaged and sold as a Phishing-as-a-Service offering. The age of AI is here, and the criminals have a subscription.
Your corporate login is the key to the kingdom, and the phishers just ordered a master key machine from a mainstream vendor.