Cybersecurity researchers have issued a stark warning regarding a newly discovered, high-severity vulnerability within Apple's iMessage platform. The flaw, which does not require any user interaction to be exploited—a so-called "zero-click" attack—could allow sophisticated spyware to be silently installed on a victim's device. This type of exploit is considered the holy grail for surveillance actors, as it bypasses the need for the target to click a malicious link or download a file, making detection exceptionally difficult. The potential attack vector threatens millions of iPhone users globally, underscoring the persistent threat posed by state-sponsored and mercenary spyware developers who continuously probe for weaknesses in widely used communication services.
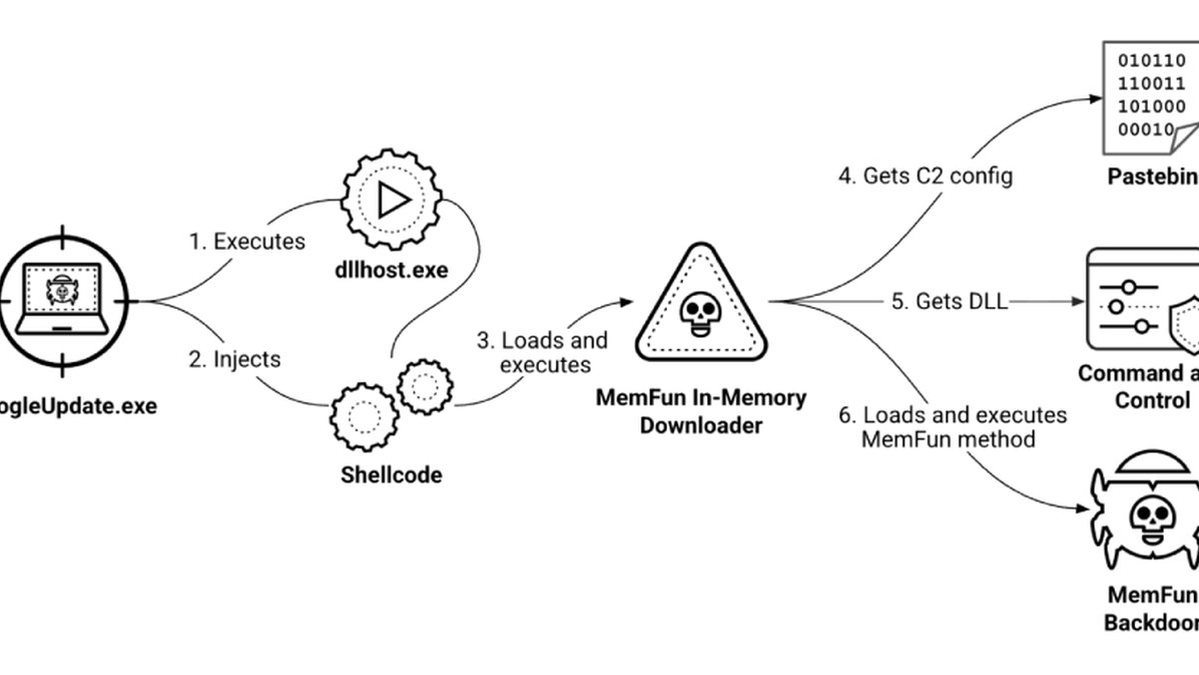
The technical mechanism of the exploit leverages a fundamental flaw in how iMessage processes a specific type of data. While Apple has not released full technical details prior to a patch, researchers indicate that a specially crafted message could trigger a memory corruption error, such as a buffer overflow or use-after-free vulnerability. This would enable an attacker to execute arbitrary code on the device with the same privileges as the iMessage service itself. Given iMessage's deep integration into iOS and its ability to access various device functions, a successful exploit could lead to the complete compromise of the device, allowing for the exfiltration of messages, photos, location data, and live microphone surveillance.
The discovery highlights the escalating threat of commercial spyware, like Pegasus from the NSO Group, which has repeatedly used similar zero-click iMessage exploits to target journalists, activists, and political dissidents. These tools are often sold to government clients under the guise of criminal and terrorism investigations but are frequently misused for illegitimate surveillance. This new vulnerability represents a potent weapon that could be added to the arsenals of such surveillance-for-hire companies, posing a significant risk to personal privacy and civil liberties on an unprecedented scale. The fact that the attack requires no user action removes the last line of behavioral defense, leaving users entirely dependent on Apple's security infrastructure.
In response to the disclosure, Apple has likely been working on a security update to address the critical flaw. Users are strongly advised to ensure their devices are updated to the latest version of iOS as soon as the patch is released. The standard security advice remains crucial: be cautious of unsolicited messages, even from known contacts, and consider disabling iMessage if absolute security is required for high-risk individuals. This incident serves as a critical reminder that no platform is impervious to attack and that the cat-and-mouse game between platform security teams and highly resourced threat actors is a continuous and evolving battle. Proactive patching and a layered security mindset are essential for all users in the modern digital landscape.