EXCLUSIVE: CONNECTWISE SCREENCONNECT FLAW IS A ZERO-DAY TICKET TO TOTAL SYSTEM HIJACKING
A critical new vulnerability in ConnectWise's ScreenConnect software is a ticking time bomb for managed service providers worldwide. This isn't just another bug; it's a cryptographic breakdown that allows attackers to bypass all signature verification. The result? Complete, unauthorized remote access and privilege escalation on any unpatched system. This is a master key handed to ransomware gangs.
The flaw, a catastrophic failure in authentication, lets threat actors create their own malicious, trusted instances of ScreenConnect. Once inside, they own the network. This exploit is a golden ticket for deploying ransomware, stealing data in a massive breach, and moving laterally with impunity. The window to patch is closing fast.
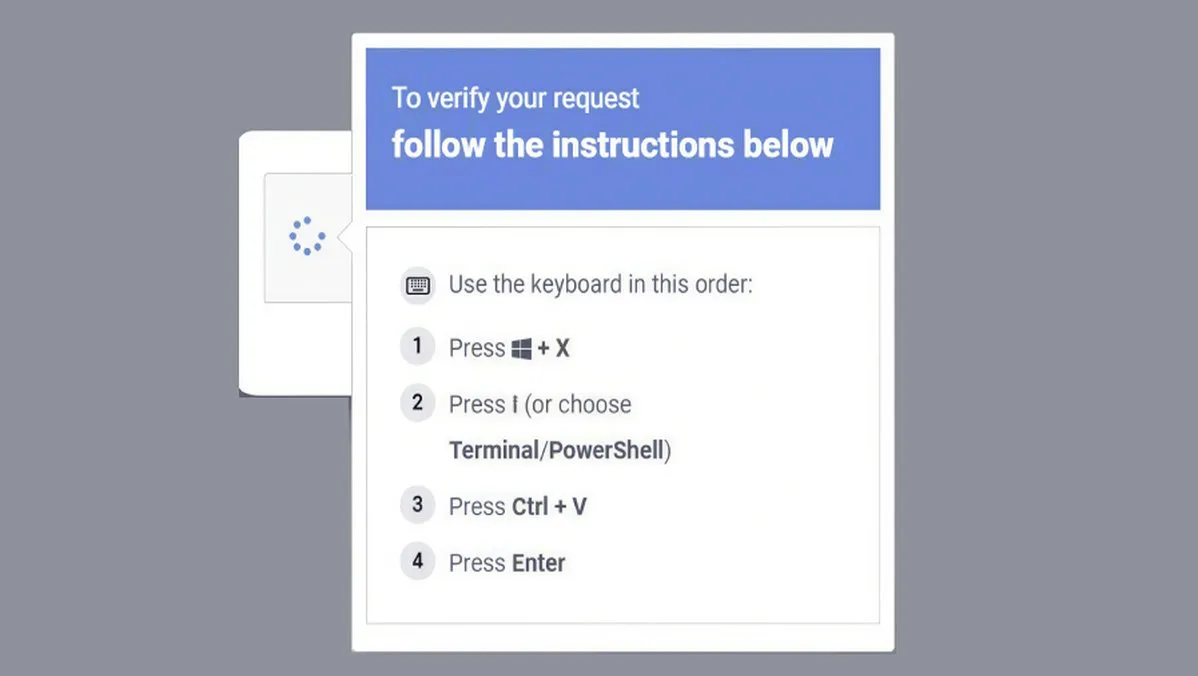
"THIS IS AS SERIOUS AS IT GETS," a top cybersecurity analyst told us. "It's a trivial exploit for a devastating outcome. We are already seeing scanning activity. This will be weaponized for phishing campaigns imitating IT support within hours, not days. The entire MSP supply chain is on red alert."
If your business relies on an MSP using ScreenConnect, you are indirectly vulnerable. This isn't just an IT problem; it's a direct business continuity threat. A single compromised MSP could lead to a cascading data breach across hundreds of its clients, with crypto-locking malware following right behind.
We predict a wave of attacks leveraging this vulnerability will hit before the weekend. The race is on, and the losers will be facing six- or seven-figure ransom demands. Blockchain security principles of immutable logging won't help you if the attackers are already in as administrators.
Patch now, or prepare to pay. The countdown has begun.