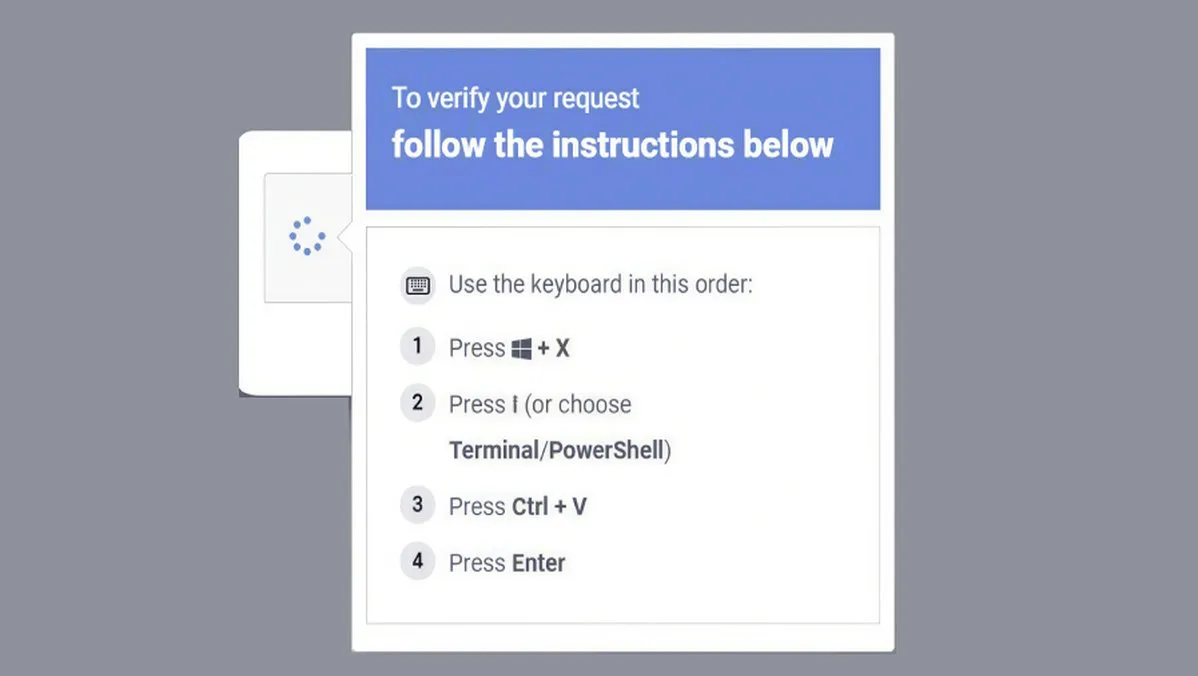
Microsoft has detailed a widespread social engineering campaign, dubbed "ClickFix," which is exploiting the Windows Terminal application to initiate a complex attack chain and deploy the Lumma Stealer malware. Observed in February 2026, this campaign deviates from traditional methods that abuse the Windows Run dialog. Instead, it instructs targets to use the Windows+X -> I shortcut to launch Windows Terminal (wt.exe) directly. Microsoft's Threat Intelligence team notes this tactic creates a privileged command execution environment that blends into legitimate administrative workflows, making it appear more trustworthy to users.
The campaign's sophistication lies in its ability to bypass security detections designed to flag Run dialog abuse. It capitalizes on the inherent legitimacy of the Windows Terminal application to deceive users into executing malicious commands. These commands are delivered through fake CAPTCHA pages, troubleshooting prompts, and other verification-style lures. Once a user pastes a hex-encoded, XOR-compressed command from the lure page into a Windows Terminal session, the attack chain begins, spawning additional Terminal and PowerShell instances to decode and execute the malicious script.
The post-compromise process is multi-staged. The decoded script leads to the download of a ZIP payload and a renamed, legitimate 7-Zip binary, saved with a randomized filename. This utility then extracts the ZIP file's contents, initiating the final stages of the attack. The Lumma Stealer malware specifically targets high-value browser artifacts like Web Data and Login Data files to harvest stored credentials, which are then exfiltrated to attacker-controlled infrastructure.
Microsoft also identified a secondary attack pathway within the same campaign. In this variant, when the compressed command is executed, it follows a similar but distinct process to achieve the same end goal of credential theft. The company's disclosure underscores a shift in attacker tactics, moving from abusing common system dialogs to leveraging trusted, built-in tools like Windows Terminal to evade detection and increase the success rate of social engineering lures.