Starbucks Corporation has officially disclosed a significant data breach impacting hundreds of its employees, referred to internally as "partners." The incident involved unauthorized access to the company's Starbucks Partner Central platform, a critical system used by staff to manage employment details, personal information, benefits, and human resources data. According to breach notification letters filed with regulatory authorities, including the Maine Attorney General's office, the company discovered the unauthorized activity on February 6, 2026. A subsequent investigation, conducted in collaboration with external cybersecurity experts, determined that threat actors had compromised approximately 889 Partner Central accounts. The attackers are believed to have gained initial access by stealing employee login credentials through phishing websites designed to impersonate the legitimate Partner Central portal.
The breach window indicates that the unauthorized parties had access to the affected accounts for a considerable period, from January 19 to February 11, 2026. Notably, Starbucks has not publicly detailed the reasons for the five-day gap between discovering the incident on February 6 and fully evicting the threat actors from its systems by February 11. The exposed personal information is reported to include sensitive employee data, though the full scope is still being assessed. This incident highlights the persistent threat of credential phishing campaigns targeting corporate portals, even at large, globally recognized organizations with substantial security resources.
As the world's largest coffeehouse chain, with over 380,000 employees and nearly 41,000 locations across 88 countries, the breach underscores the vast attack surface and high-value target that such enterprises represent. Starbucks has stated it is directly notifying affected individuals and providing them with guidance and support, which likely includes credit monitoring services and recommendations for password changes and multi-factor authentication (MFA) enablement. The company's disclosure follows a mandatory reporting timeline, but the event raises questions about the effectiveness of its current authentication safeguards and employee security awareness training against sophisticated phishing attempts.
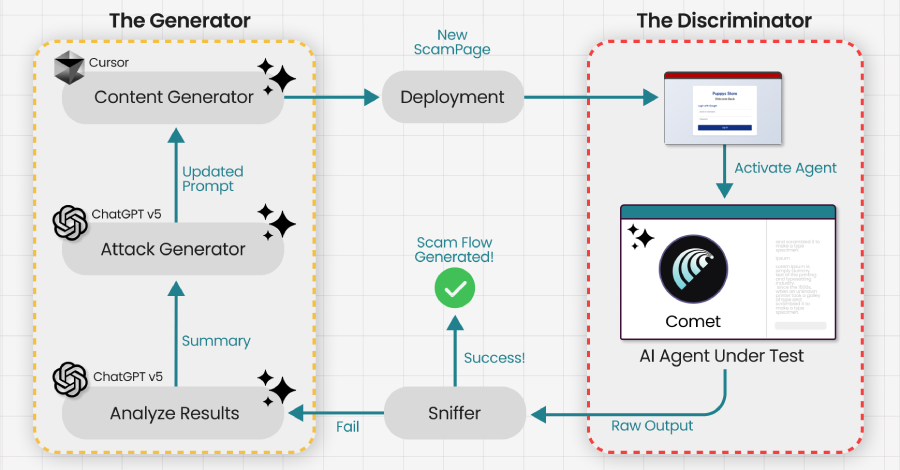
This breach occurs amidst a heightened global cybersecurity landscape, as evidenced by other major incidents reported concurrently, including new NPM package attacks, Microsoft patching critical zero-days, and ransomware attacks against organizations like England Hockey. For Starbucks and other multinational corporations, the incident serves as a critical reminder that human-centric attacks remain a primary vector for data theft. Moving forward, the company will need to reinforce its defenses, potentially by implementing phishing-resistant authentication methods, such as the passkey technology recently promoted by Microsoft, and conducting rigorous security audits of all employee-facing access points to prevent similar future compromises.