EXCLUSIVE: YOUR CYBERSECURITY TEAM IS THE TARGET IN A NEW BREED OF PHISHING WARFARE
Forget the simple email scam. The most devastating attacks today are weaponizing your own Security Operations Center against you. This isn't just about malware or a single data breach; it's a calculated siege designed to cripple your last line of defense from within.
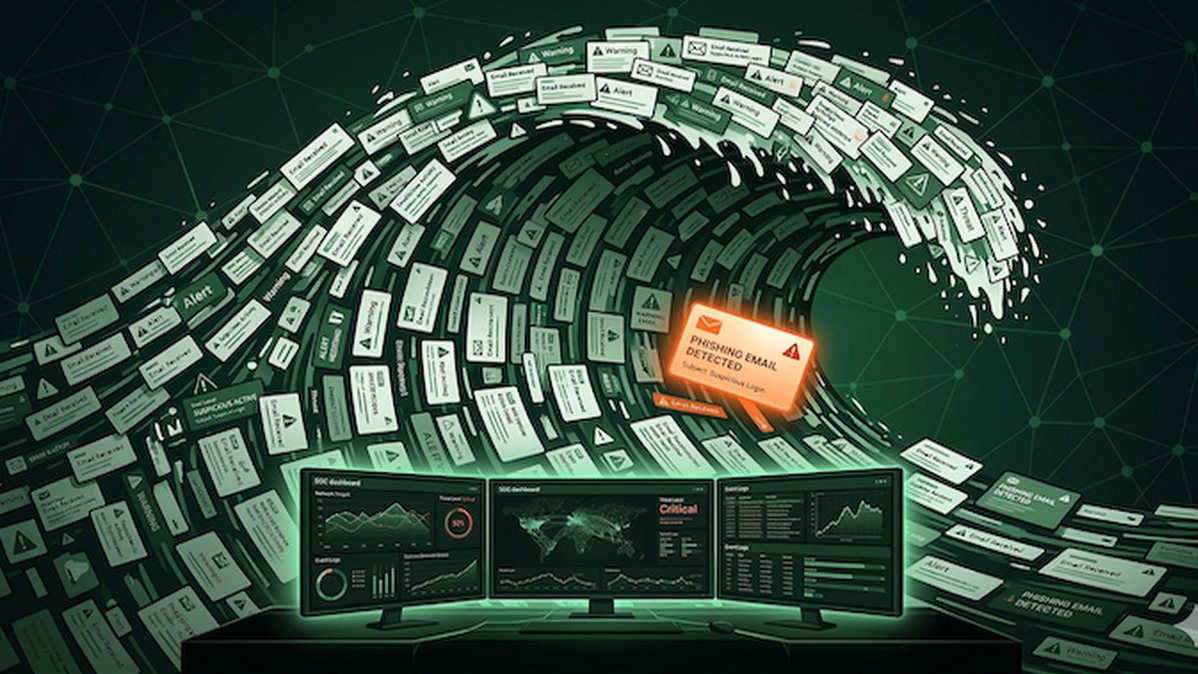
The critical vulnerability is no longer just an employee clicking a link. It's the exhausted analyst drowning in a sea of alerts. Attackers now launch massive, low-sophistication phishing waves specifically to overwhelm SOC queues. Buried in this noise are a handful of lethal, targeted spear-phishing exploits—the real payload. When an investigation stretches from five minutes to twelve hours, a contained incident explodes into a full-scale ransomware event.
"This is informational denial-of-service," explains a senior threat intelligence analyst. "They're not just probing for a zero-day; they're manufacturing one by exhausting your human analysts. Your crypto and blockchain security protocols are useless if the team monitoring them is paralyzed."
Every organization is at risk. This strategy bypasses traditional defenses by attacking the investigation process itself. The flood of decoy alerts creates the perfect cover for a targeted data breach, exploiting the finite attention of your team as the ultimate weakness.
We predict a surge in these hybrid campaigns, merging volume-based phishing with precision exploits. The industry's focus must shift from just stopping the initial email to fortifying the entire investigative chain.
Your SOC is under fire. The question is, will it hold or become the breach's point of entry?