EXCLUSIVE: MALICIOUS AI AGENTS DEPLOY INFOSTEALERS IN GLOBAL SEARCH AD CAMPAIGN
A dangerous new wave of attacks is weaponizing the public's hunger for AI tools. Threat actors are running coordinated Google Ads campaigns that push malicious installation guides for popular AI agents like Claude Code, OpenClaw, and Doubao. This is not a simple phishing scam; it's a sophisticated malware distribution network exploiting trusted search engines.
The core cybersecurity threat is twofold. For macOS users searching for these tools, the payload is the AMOS infostealer. For Windows users, it's the Amatera infostealer. Both are designed to steal sensitive data in a devastating data breach. The attackers use legitimate platforms like Squarespace to host fake documentation, easily bypassing standard anti-phishing defenses.
"These campaigns represent a strategic shift," explains a senior threat intelligence analyst. "They're exploiting the gray area of corporate policy where employees seek out unauthorized AI tools for workflow automation. The malicious ads are the perfect trap, appearing at the very moment of vulnerability." The use of Google Ads provides a veneer of legitimacy that dramatically increases the success rate of the exploit.
Every employee trying to download an unvetted AI coding assistant is now a potential entry point for ransomware. A single infection can lead to stolen credentials, compromised blockchain security wallets, and crippled networks. The lack of a zero-day vulnerability here is irrelevant; the exploit preys on human curiosity and corporate policy gaps.
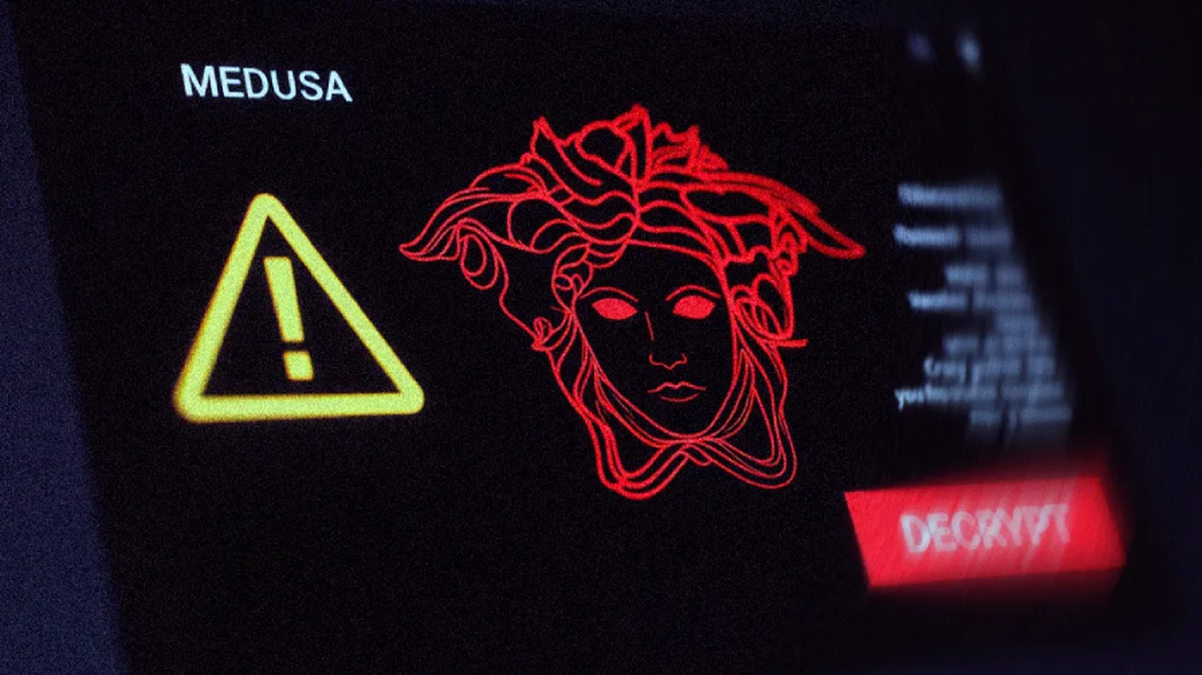
We predict a surge in similar campaigns targeting other high-demand AI platforms throughout 2024. The monetization path is clear: stolen data, crypto wallet drainers, and ransomware deployment.
The AI gold rush has a malware problem, and it's being served at the top of your search results.