Cybersecurity researchers have uncovered a sophisticated malware campaign, dubbed KadNap, that is systematically compromising edge networking devices—primarily Asus routers—to conscript them into a large-scale botnet designed for proxying malicious internet traffic. According to a detailed report from Lumen's Black Lotus Labs, the malware was first observed in the wild in August 2025 and has since expanded to infect more than 14,000 devices globally. The United States bears the brunt of this campaign, accounting for over 60% of the infected nodes. Significant infections have also been detected in Taiwan, Hong Kong, Russia, the United Kingdom, Australia, Brazil, France, Italy, and Spain, indicating a broad, international targeting strategy.
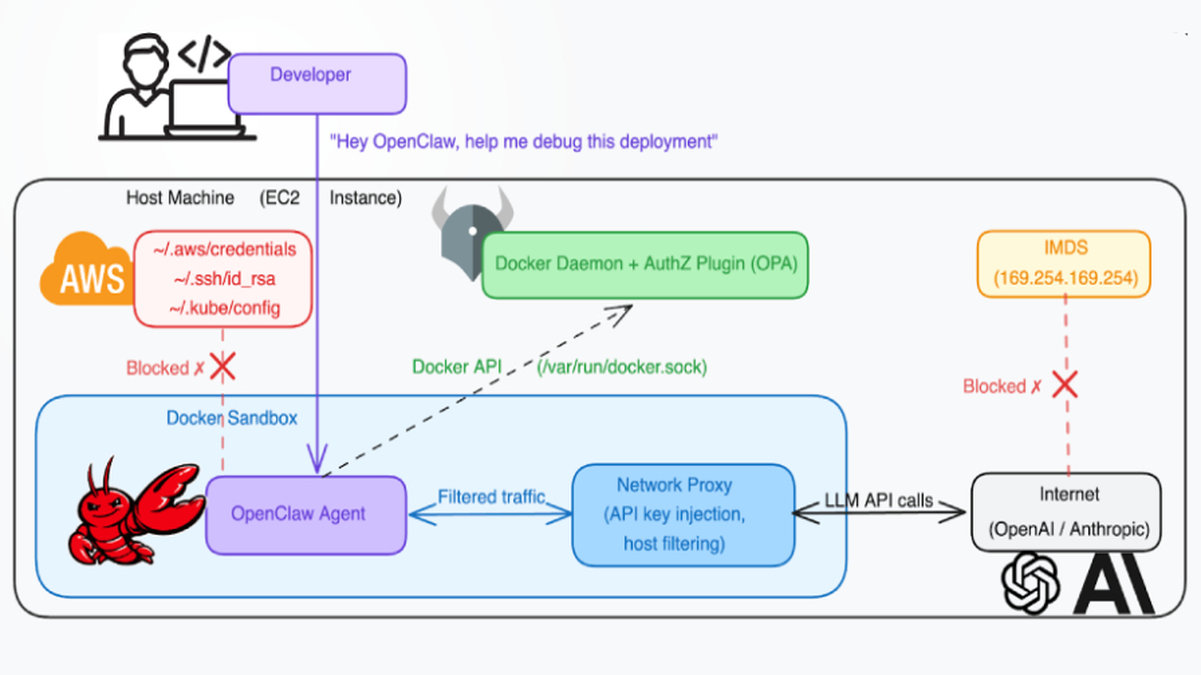
The technical sophistication of KadNap lies in its use of a custom implementation of the Kademlia Distributed Hash Table (DHT) protocol. This peer-to-peer (P2P) networking approach is typically associated with decentralized systems like file-sharing networks. KadNap repurposes it to obfuscate its command-and-control (C2) infrastructure. By embedding C2 server information within the DHT network, the malware allows compromised devices to locate and connect to controllers without relying on a static, easily blocklisted IP address or domain. This design makes the botnet highly resilient, evading traditional network monitoring and takedown efforts that target centralized C2 servers.
Once a device is successfully infected and integrated into the P2P network, it becomes a commodity for a proxy service named Doppelgänger (operating at doppelganger[.]shop). Security analysts assess this service to be a rebrand of "Faceless," a previously known proxy service linked to TheMoon malware. Doppelgänger's website, which launched around May/June 2025, advertises "resident proxies" in over 50 countries, promising "100% anonymity" for its users—likely cybercriminals seeking to hide their activities behind a veil of legitimate-looking, compromised residential IP addresses. This monetization model transforms vulnerable home and small office routers into tools for fraud, credential stuffing, ad fraud, and other illicit online operations.
The initial compromise begins with a shell script named `aic.sh`, downloaded from a C2 server at IP address 212.104.141[.]140. This script establishes persistence on the victim device by creating a cron job that executes at the 55th minute of every hour. The cron job's task is to fetch the latest version of the script from the C2 server, rename it to ".asusrouter" (a filename designed to blend in on Asus devices), and execute it. This persistent script then downloads a malicious ELF binary file, renames it to "kad," and executes it to fully enroll the device into the KadNap botnet. While Asus routers are the primary target, evidence suggests the malware's operators are actively exploiting vulnerabilities in a wider array of edge networking devices, expanding their potential pool of proxies and increasing the threat's scale and persistence.