EXCLUSIVE: HOW A ZERO-DAY VULNERABILITY AND HACKED TRAFFIC CAMS ENABLED A DECAPITATING STRIKE
The opening salvos of the conflict were not missiles, but malware. A coordinated cyber offensive, leveraging a previously unknown zero-day vulnerability, crippled Iran's national defenses hours before kinetic strikes began. This was not a supporting act; it was the opening move that made the physical bombardment possible. The era of standalone warfare is over. CYBERSECURITY is now the frontline.
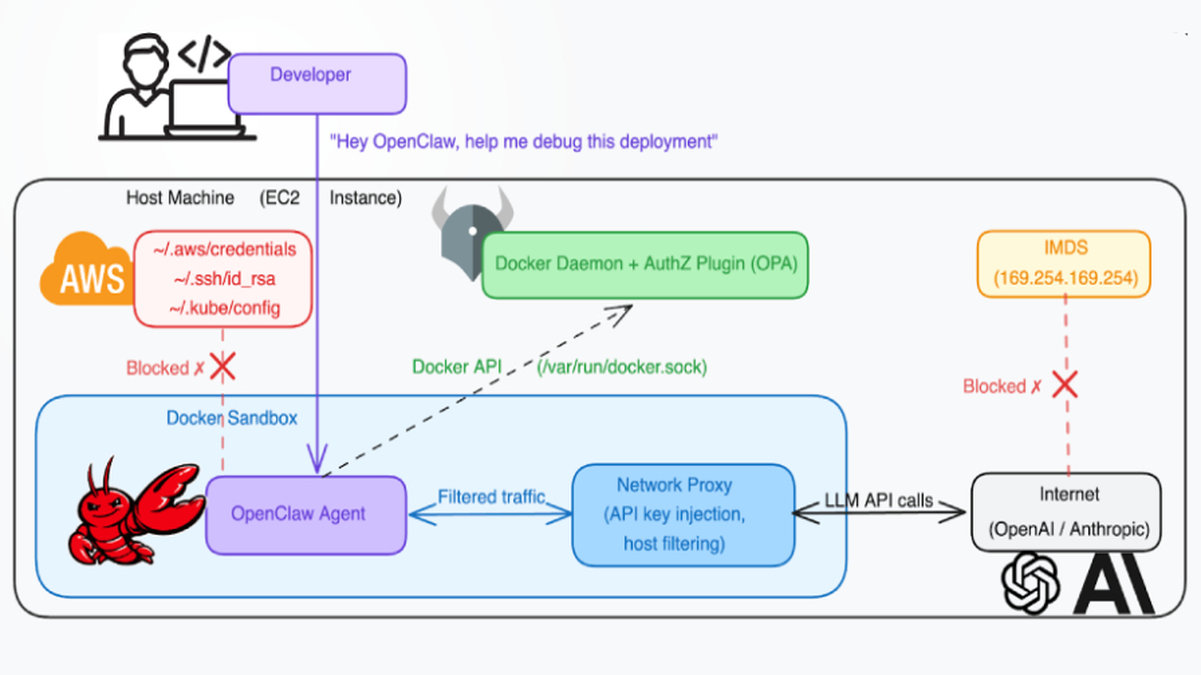
Intelligence officials confirm that the operation involved a multi-pronged digital assault. A devastating ransomware-style attack locked down critical military communication hubs, while sophisticated phishing campaigns targeted senior officials, creating chaos and obscuring the coming storm. The most chilling component, however, was the surveillance. For years, state actors had deeply penetrated Tehran's urban infrastructure, turning thousands of traffic cameras and even broadcast TVs into a live-streamed intelligence network.
"This was a paradigm shift," a former U.S. cyber command official told us. "They didn't just disrupt systems; they weaponized the city's own eyes. The data breach from the camera network provided real-time pattern-of-life tracking, making the subsequent strikes terrifyingly precise. It turned everyday infrastructure into a lethal exploit."
Why should the average citizen care? Because the digital battlefield is porous. The same techniques used to hijack a state TV broadcast or exploit a municipal camera system can be adapted by criminal gangs for extortion or by hostile actors to disrupt our own cities. The crypto payments fueling ransomware gangs and the complex blockchain security of nation-states are two sides of the same coin. Your security is tied to global digital stability.
We predict the next major conflict will begin with an even more silent, catastrophic digital exploit—one that could turn off the power, crash financial networks, or falsify critical data long before a single soldier moves. The lesson from Tehran is unambiguous: the first casualty of modern war is truth, and the first weapon is code.
The cameras are always watching. The question is, who owns the feed?