Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft
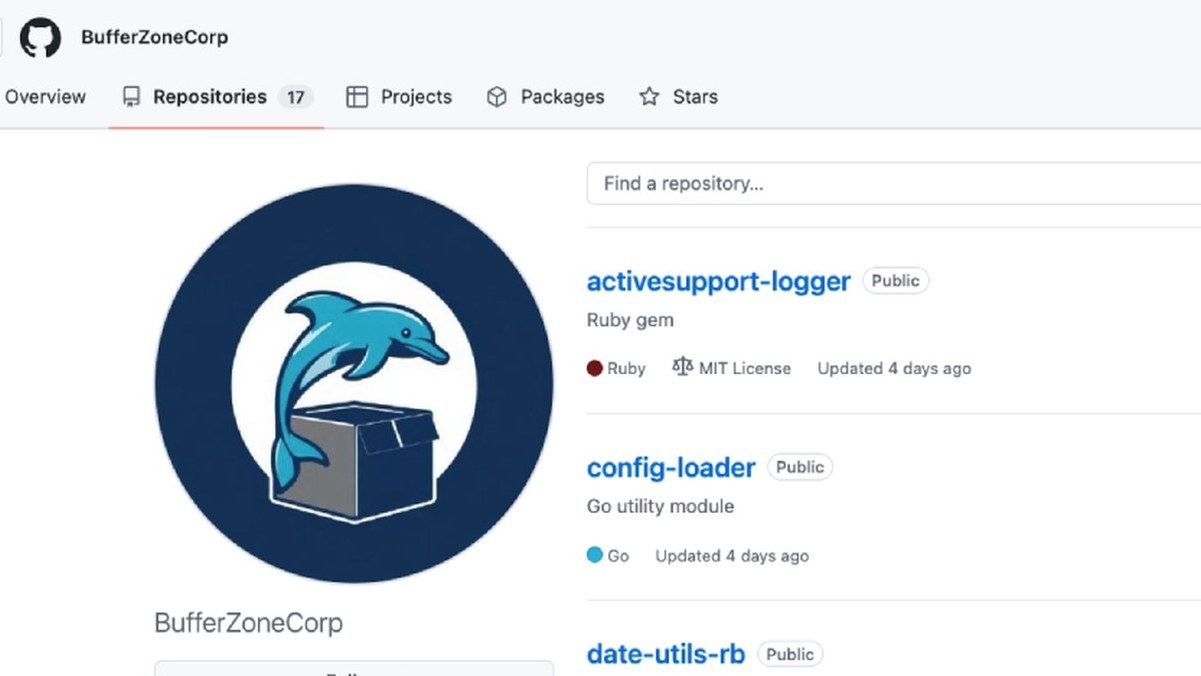
A new software supply chain attack campaign has been observed using sleeper packages as a conduit to subsequently push malicious payloads that enabled credential theft, GitHub Actions tampering, and SSH persistence. The activity has been attributed to the GitHub account "BufferZoneCorp," which has published a set of repositories that are associated with malicious Ruby gems and Go modules. As of writing, the packages have been yanked from RubyGems, and the Go modules have been blocked. The names of the libraries are listed below - The identified packages masquerade as recognizable and well-known modules like activesupport-logger, devise-jwt, go-retryablehttp, grpc-client, and config-loader so as to evade detection and trick users into downloading them. "The account is part of a software supply chain campaign targeting developers, CI runners, and build environments across two ecosystems,"
Source: https://thehackernews.com/2026/05/poisoned-ruby-gems-and-go-modules.html