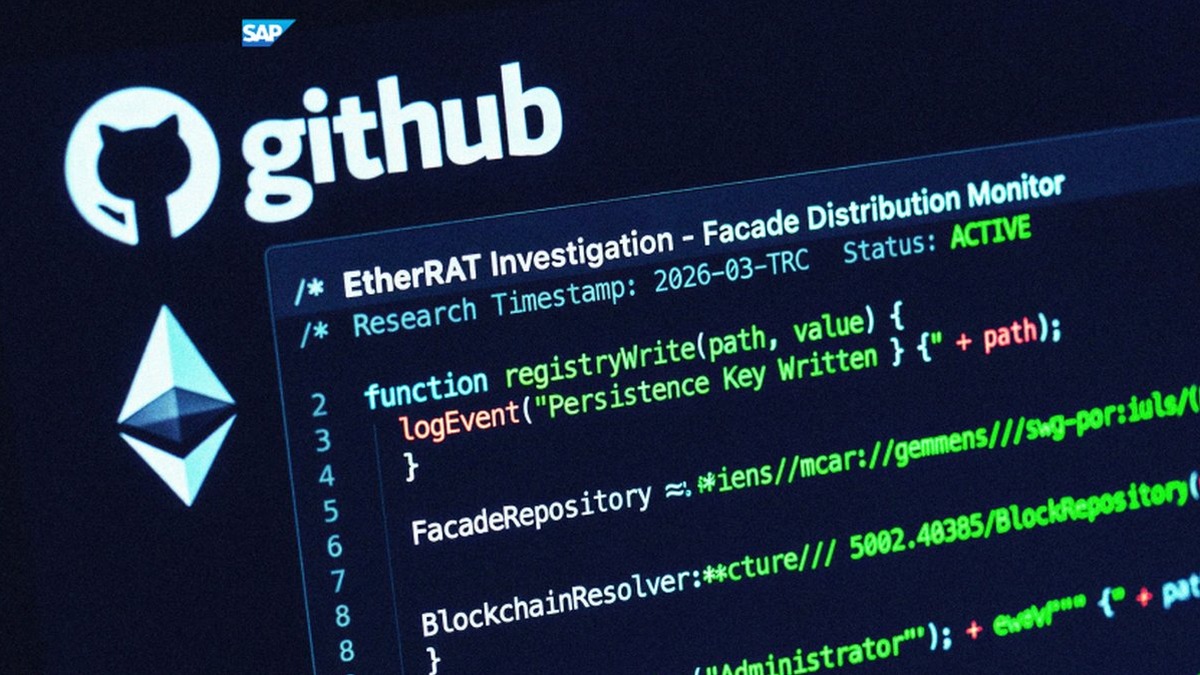
EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades
A sophisticated, high-resilience malicious campaign was identified by Atos Threat Research Center (TRC) in March 2026. This operation specifically targets the high-privilege professional accounts of enterprise administrators, DevOps engineers, and security analysts by impersonating administrative utilities they rely on for daily operations. By integrating Search Engine Order (SEO) poisoning, a dual-stage GitHub distribution architecture, and decentralized blockchain-based command-and-control (C2) resolving, Threat Actors have established a highly resilient delivery and persistence mechanism. The campaign utilizes a multi-layered delivery chain designed to evade platform-level takedowns and maintain a high search engine ranking. The attack begins with SEO poisoning on various search engines, including Bing, Yahoo, DuckDuckGo, and Yandex. That ensures that malicious results for niche IT te
Source: https://thehackernews.com/2026/04/etherrat-distribution-spoofing.html