EXCLUSIVE: DOCKER'S "FIXED" SECURITY HOLE REOPENS, EXPOSING MILLIONS OF CONTAINERS TO HOST TAKEOVER
A critical cybersecurity vulnerability, supposedly patched months ago, has violently resurfaced inside Docker Engine, creating a backdoor that lets attackers completely bypass security controls and seize control of the underlying host server. Tracked as CVE-2026-34040 with a high CVSS score of 8.8, this flaw is a direct regression of the maximum-severity CVE-2024-41110 disclosed in July. The incomplete fix means the original door to a catastrophic data breach was never fully locked.
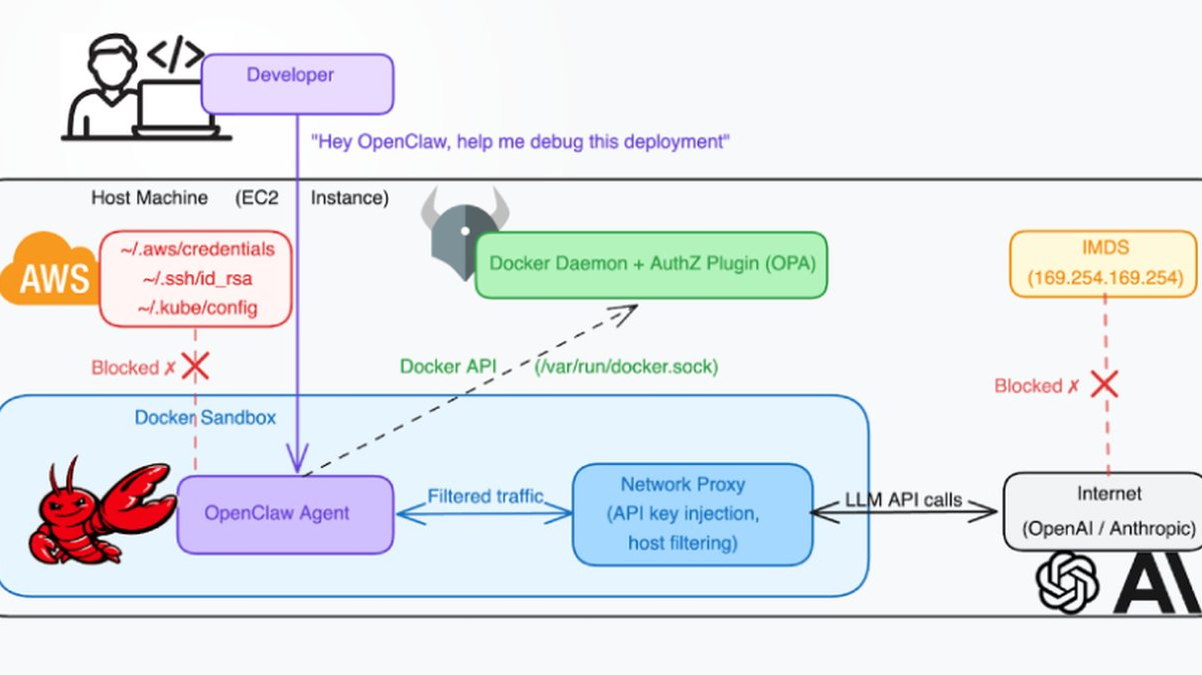
The core of the exploit targets Docker's authorization plugin (AuthZ) system, a critical gatekeeper meant to vet every command. This zero-day vulnerability allows a malicious actor to craft requests that slip past these plugins entirely. Once this authorization is bypassed, an attacker can execute commands with elevated privileges, leading directly to a full host compromise. This is not a theoretical phishing risk; it is a direct path for ransomware deployment.
"Think of it as fixing a broken lock but leaving the deadbolt unengaged," explained a senior engineer at a cloud security firm we spoke to under condition of anonymity. "Attackers now have a documented blueprint from the original CVE. They can leverage this regression to craft a reliable exploit, potentially automating host takeover across unpatched container fleets. The pivot to crypto-mining malware or a systemic ransomware attack is trivial from that position."
This matters because Docker is the backbone of modern software development, running on countless developer machines and production servers globally. A vulnerability at this level doesn't just risk a single application; it risks the entire server and every other container on it. The potential for lateral movement and massive, cascading data breaches is enormous.
We predict a surge in scanning activity and exploit attempts within weeks as the technical details circulate. This regression is a stark lesson in blockchain security principles: immutability and verification. A fix must be complete and permanent, not a temporary patch that can be rolled back by a new vulnerability.
The container revolution just sprung a lethal leak. Patch immediately or prepare to be owned.