The Russian state-sponsored advanced persistent threat (APT) group known as APT28, also tracked as Forest Blizzard, has been identified as the perpetrator behind a sophisticated and widespread cyber espionage campaign. Since at least May 2025, the group has been systematically compromising insecure small office/home office (SOHO) routers, primarily from manufacturers MikroTik and TP-Link. The campaign's objective is to hijack the devices' Domain Name System (DNS) settings, effectively converting them into malicious infrastructure under the attackers' control. This infrastructure is then used to redirect unsuspecting users to adversary-controlled servers, facilitating credential theft and surveillance.
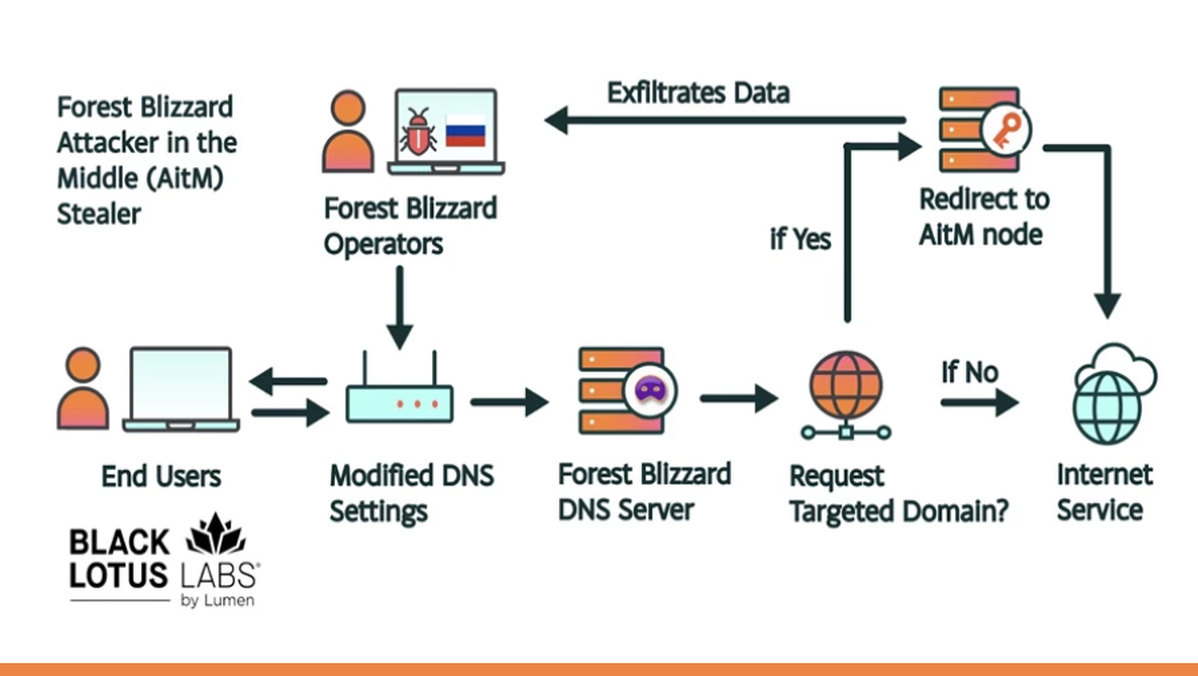
This large-scale exploitation campaign, which security researchers have codenamed, represents a significant evolution in APT28's tactics. By targeting consumer-grade network edge devices, the group bypasses traditional enterprise security perimeters. These routers are often overlooked in security postures, frequently running outdated firmware with known vulnerabilities and weak default credentials. Once compromised, APT28 modifies the DNS server settings. Consequently, when users on the network attempt to visit legitimate websites, their traffic is silently redirected to malicious lookalike sites designed to harvest login credentials or to servers that intercept and manipulate their communications.
The global nature of the campaign underscores a strategic shift towards leveraging "living-off-the-land" techniques within network infrastructure. Instead of deploying custom malware directly on target endpoints, APT28 is weaponizing the very hardware that facilitates internet connectivity. This method provides them with a persistent foothold, allows for traffic interception across all devices on the local network, and can be remarkably difficult to detect for the average user or even small businesses without dedicated IT security. The hijacked routers essentially act as a covert man-in-the-middle (MitM), enabling espionage against a broad range of victims whose traffic passes through them.
The implications of this campaign are severe for both individual and organizational cybersecurity. Compromised DNS means that even encrypted HTTPS connections can be subverted if users are tricked into connecting to fraudulent sites. This campaign likely supports broader intelligence-gathering operations, targeting government entities, NGOs, and corporations globally. Defenders are urged to immediately audit their SOHO router security, enforce strong unique passwords, disable remote management features, and diligently apply firmware updates. This incident serves as a critical reminder that network infrastructure itself is a prime target and must be included in comprehensive security hardening protocols.