EXCLUSIVE: THE END OF BREACH MONITORING AS WE KNOW IT — INFOSTEALERS ARE WINNING THE CYBER WAR
Forget the old playbook. A new wave of credential-based attacks is rendering traditional cybersecurity defenses utterly obsolete. The era of simple breach monitoring is over, and a silent data breach epidemic is already underway.
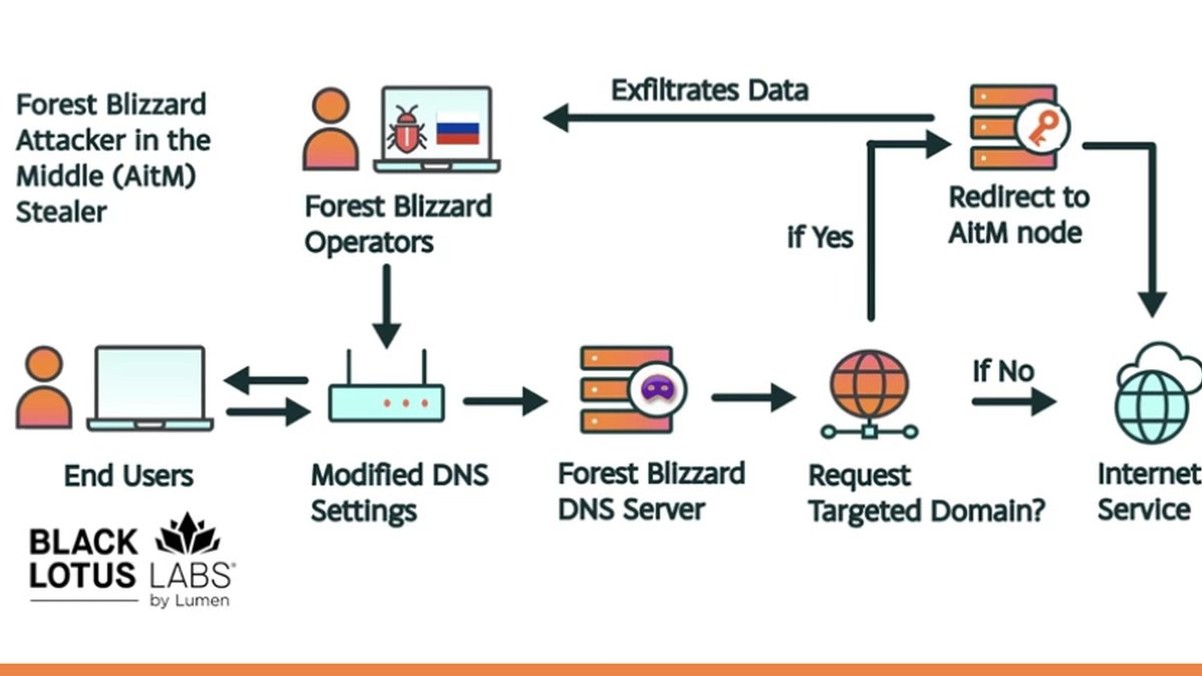
Security firm Lunar has revealed a chilling new reality: sophisticated infostealer malware is now harvesting credentials and session cookies at an industrial scale. This isn't just about stealing passwords; it's about stealing entire authenticated sessions, allowing attackers to bypass multi-factor authentication and walk right through the front door. These attacks exploit human vulnerability through targeted phishing campaigns and leverage unpatched software flaws, including dangerous zero-day vulnerabilities, to gain initial access.
"Traditional security perimeters are crumbling," warns a senior threat analyst who requested anonymity. "We're seeing a direct pipeline from these infostealer infections to devastating ransomware payloads and massive data breaches. The criminals are several steps ahead, using these stolen credentials to move laterally with legitimate access." The tools for these exploits are increasingly traded on darknet markets, often paid for with untraceable crypto.
This matters because your company's crown jewels—financial data, intellectual property, customer information—are now directly tied to the login credentials of your most junior employee. A single phishing email can compromise an entire network, making blockchain security for internal systems a future necessity, not a luxury.
We predict a seismic shift in the cybersecurity industry within 18 months, moving from passive monitoring to active, identity-centric defense. Companies that fail to adapt will become headlines.
The password is dead. Your session is the new battleground.