EXCLUSIVE: CRYPTO AND CORPORATE SECRETS VACUUMED IN AUTOMATED ZERO-DAY SIEGE
A ruthless new cyber threat is conducting a silent, automated massacre of corporate servers, and your company's blockchain security keys could be next. Dubbed UAT-10608, this sophisticated cluster is exploiting a critical vulnerability in exposed Next.js applications, turning them into open doors for a devastating data breach.
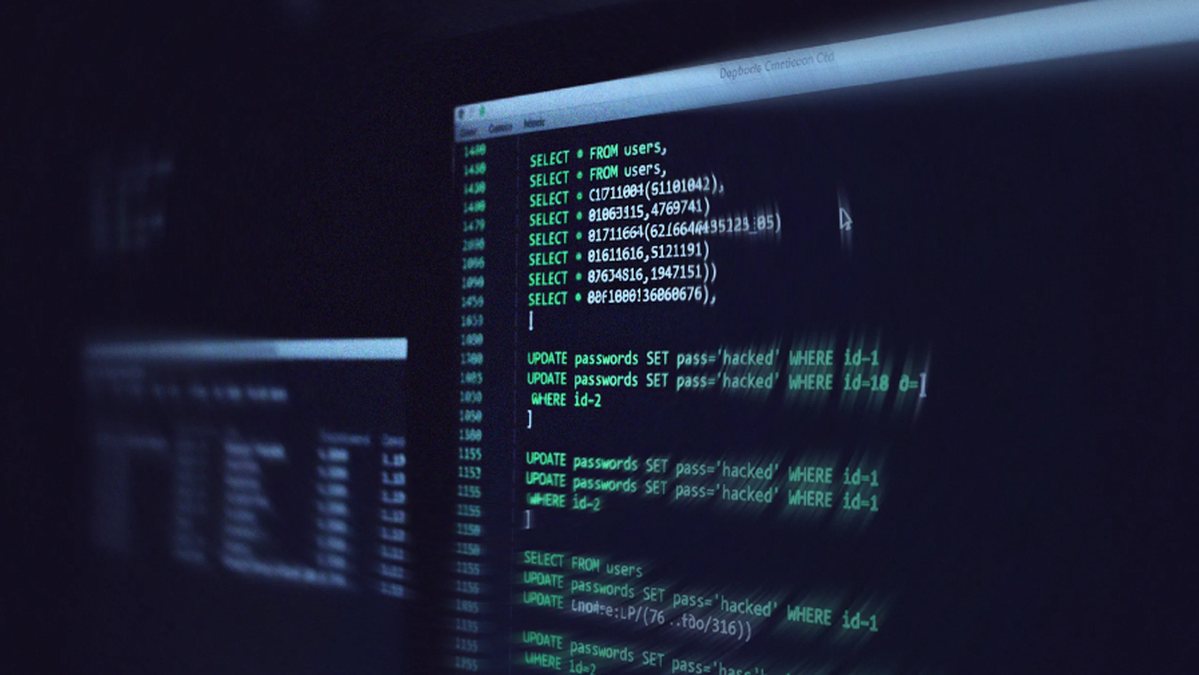
The operation is chillingly efficient. Using a tool that automates the exploitation of what experts are calling the React2Shell flaw, the attackers are not just stealing passwords. They are conducting systematic raids, exfiltrating high-value secrets, API keys, and sensitive internal data at an industrial scale. This is not a smash-and-grab; it's a calculated extraction.
"This is a malware delivery platform disguised as a credential harvester," warns a senior cybersecurity analyst familiar with the investigation. "They establish a beachhead using this phishing-style exploit, but their toolkit is built for escalation. The end goal is often full system compromise and ransomware deployment."
The implications are severe. Any organization using Next.js for customer portals, internal tools, or—critically—crypto wallet interfaces is vulnerable. This zero-day exploit bypasses traditional defenses, making a successful phishing attack look like child's play. The stolen credentials provide immediate access, while the pilfered secrets enable lateral movement across cloud networks.
We predict a wave of targeted ransomware attacks stemming from this campaign within weeks, as UAT-10608 cashes in on its stolen access. The quiet phase of credential harvesting is over; the loud phase of extortion is imminent.
Your digital vault is being case right now by a machine that never sleeps.