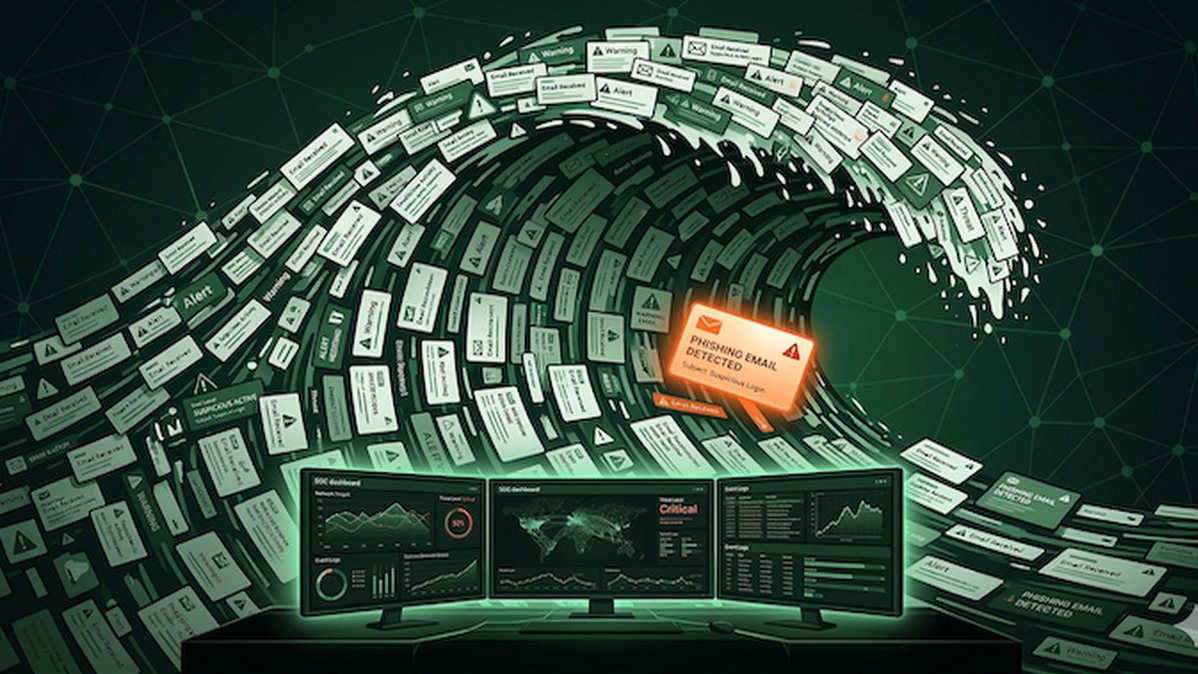
A hacktivist group with assessed ties to Iranian intelligence has claimed responsibility for a large-scale data-wiping cyberattack against Stryker, a leading global medical technology corporation headquartered in Michigan. The attack has caused significant operational disruption, with news reports from Ireland—Stryker's largest operational hub outside the United States—indicating the company sent home over 5,000 employees. Furthermore, a voicemail message at the company's main U.S. headquarters confirmed it was experiencing a "building emergency," a term often used during major IT outages. This incident highlights the severe real-world consequences when critical infrastructure, even in the healthcare sector, is targeted by sophisticated, state-aligned threat actors.
In a detailed statement published on Telegram, the group known as Handala (or the Handala Hack Team) asserted it had successfully erased data from more than 200,000 systems, servers, and mobile devices, forcing the shutdown of Stryker's offices across 79 countries. Stryker, a Fortune 500 company [NYSE:SYK] specializing in medical and surgical equipment with $25 billion in annual sales, has not yet released an official public statement confirming the scope of the breach. The Handala manifesto framed the attack as an act of digital retaliation, explicitly linking it to a February 28 missile strike on an Iranian school that killed at least 175 people, predominantly children. The group claimed, "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption," though the primary impact reported is data destruction, not theft.
The attribution of this attack carries significant weight due to prior cybersecurity industry analysis. Handala was recently profiled by Palo Alto Networks' Unit 42 threat intelligence team, which assesses the group as an online persona operated by Void Manticore, a cyber threat actor affiliated with Iran's Ministry of Intelligence and Security (MOIS). This connection suggests the attack is part of a broader pattern of Iranian state-aligned cyber activity, which has increasingly utilized hacktivist personas to conduct disruptive operations while maintaining plausible deniability. The targeting of a major Western medical technology firm represents a notable escalation, moving beyond traditional espionage or financially motivated crime to destructive attacks that can impact global healthcare supply chains and patient care.
The Stryker incident serves as a critical case study for the cybersecurity community and corporate leaders. It underscores the vulnerability of even well-resourced, multinational corporations to destructive wiper malware, which is designed to render systems inoperable by deleting critical data. For the healthcare and life sciences sector, which is already a high-value target for ransomware gangs, this attack introduces a more dangerous threat vector focused on pure disruption and geopolitical signaling. Organizations must now prioritize not only data protection and ransomware resilience but also robust, isolated backups and rapid recovery protocols to withstand destructive state-sponsored attacks. This event is a stark reminder that in modern geopolitical conflicts, cyber operations are a primary tool, and no industry is considered off-limits.