COOKIE MONSTERS: HACKERS NOW USING YOUR BROWSER'S COOKIES TO CONTROL ENTIRE SERVERS
A chilling new cyberattack technique is turning a fundamental piece of web technology against itself. Microsoft security researchers have exposed a stealthy campaign where hackers are using HTTP COOKIES—the very data that remembers your login—as a secret remote control for servers. This isn't just another MALWARE variant; it's a paradigm shift in stealth, leaving traditional defenses blind.
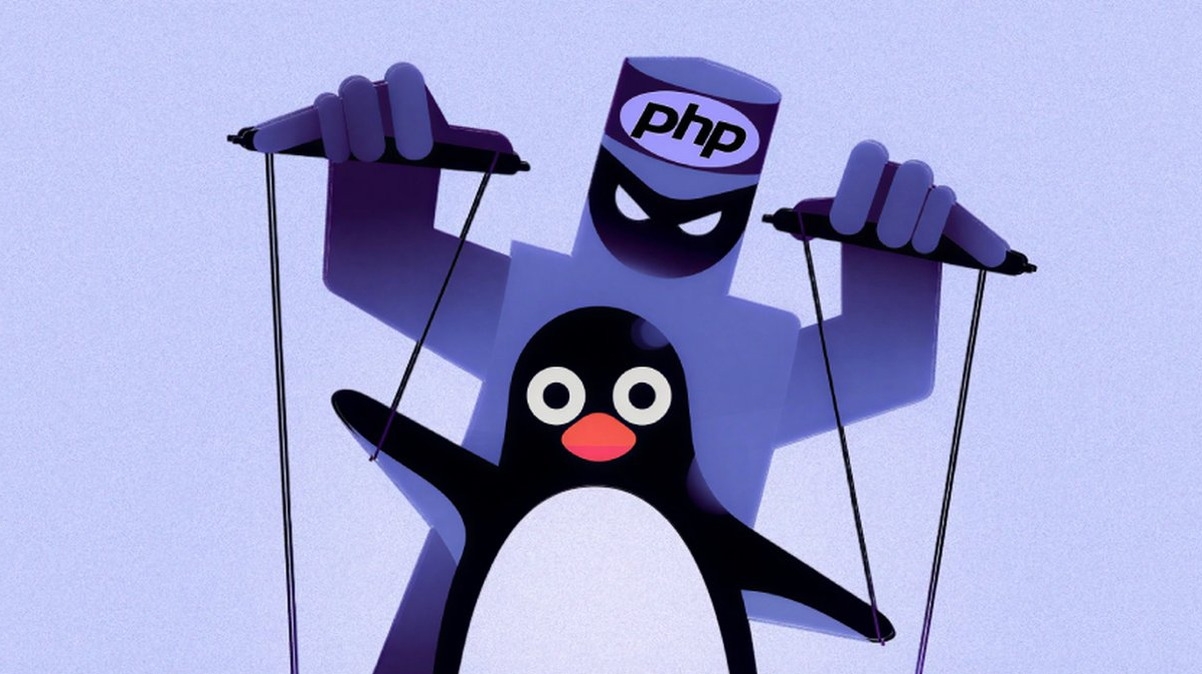
The attack deploys a PHP-based WEB SHELL on LINUX servers, but with a sinister twist. Instead of using obvious channels like URL parameters, the backdoor lies dormant until it reads specific commands hidden inside the COOKIE values of an incoming HTTP request. This allows threat actors to achieve full REMOTE CODE EXECUTION while blending their malicious traffic seamlessly into normal web activity. It’s persistence through deception.
"THIS METHOD IS A NIGHTMARE FOR DETECTION," explains a senior cybersecurity analyst familiar with the investigation. "It bypasses standard signature-based tools and turns a common, trusted protocol into an attack VECTOR. We are looking at a potent new EXPLOIT framework." The technique highlights a critical VULNERABILITY in how we monitor authenticated web traffic.
For any business, this is a DATA BREACH waiting to happen. A successful intrusion using this method gives attackers the keys to the kingdom, enabling everything from data theft to deploying RANSOMWARE. The use of CRYPTO in ransom demands is a near certainty. This attack chain could also be used to compromise related BLOCKCHAIN SECURITY infrastructure if servers are involved in transaction validation.
This discovery signals a move towards "living-off-the-land" attacks that misuse legitimate functions. PHISHING campaigns will likely evolve to plant these cookie-controlled shells. The industry must brace for copycats. ZERO-DAY hunters are now scouring web application code for similar oversights.
Your website's remember-me function is now a potential backdoor. The age of invisible threats is here.