EXCLUSIVE: LINKEDIN'S SECRET BROWSER SCAN EXPOSES MILLIONS TO CYBER ATTACKS
A bombshell "BrowserGate" report reveals Microsoft-owned LinkedIn is running a covert surveillance operation on every visitor. Hidden JavaScript scripts are actively scanning your browser for over 6,000 Chrome extensions and harvesting sensitive device data without clear consent. This isn't just about ads; it's a corporate-sanctioned data breach waiting to be exploited.
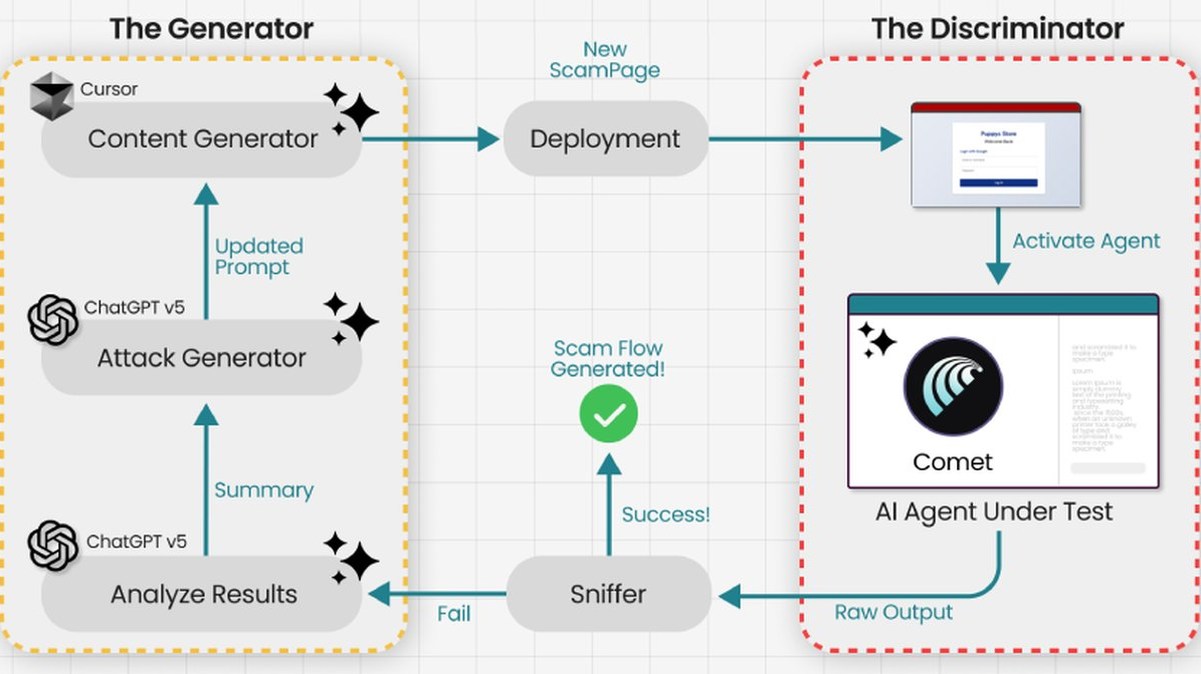
The core facts are chilling. This automated scan creates a unique digital fingerprint of every user. Cybersecurity experts warn this treasure trove of data could be reverse-engineered by threat actors to identify software versions, pinpoint zero-day vulnerabilities, and craft hyper-targeted phishing campaigns. Your professional network is now a potential backdoor.
"Imagine a hacker cross-referencing this extension data with known exploits," states a senior threat intelligence analyst we spoke to. "They can identify users with vulnerable extensions and deliver tailored malware or ransomware payloads. LinkedIn has built a targeting database for cybercriminals." The line between analytics and an attack vector has vanished.
Why should you care? This practice fundamentally undermines your cybersecurity at the very moment you're trying to enhance your career. The collected data could reveal your password manager, crypto wallet extensions, or blockchain security tools—painting a bullseye on your digital assets. Your browser's privacy is now compromised by the platform demanding your professional trust.
We predict regulatory firestorms and a new wave of class-action lawsuits. In an era of rampant data breaches, this corporate overreach sets a dangerous precedent. If a platform this powerful can probe your browser with impunity, no one's digital life is safe.
LinkedIn just turned your resume into a risk assessment for hackers.