EXCLUSIVE: THE VPN AUDIT GAP — YOUR 'NO-LOGS' PROMISE COULD BE A CYBERSECURITY TIME BOMB
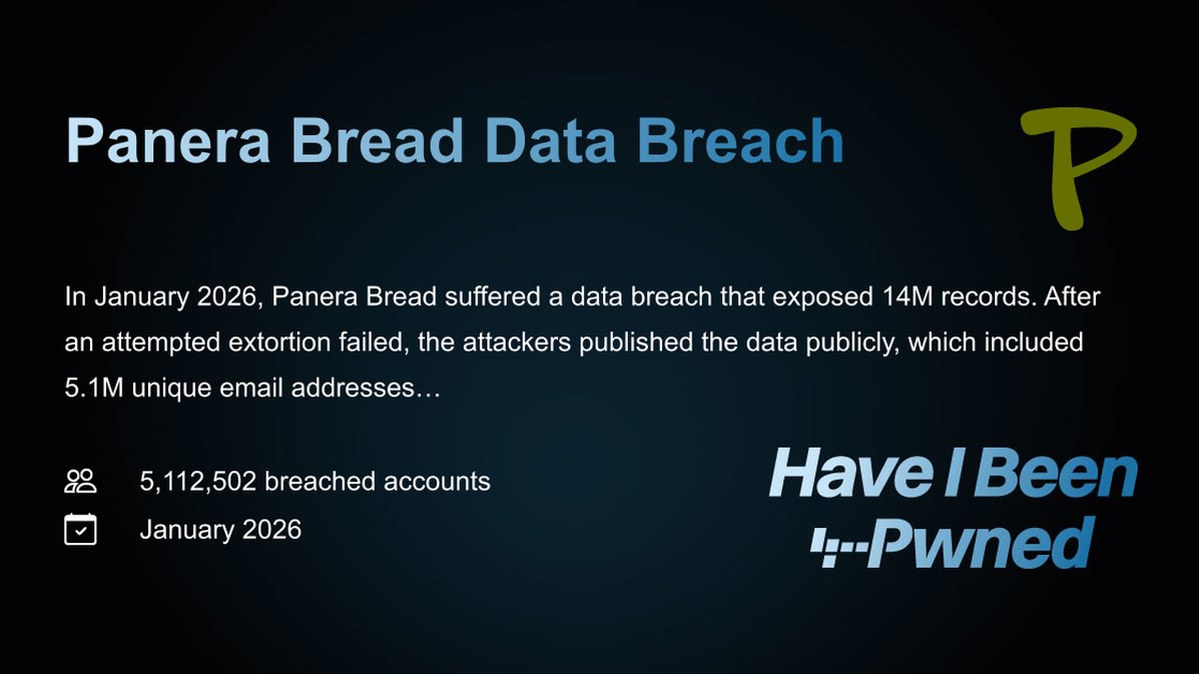
In a digital world saturated with threats, from sophisticated ransomware to targeted phishing campaigns, we blindly trust VPNs as our last line of defense. But what if that very shield is riddled with unseen vulnerabilities? A rare third-party audit of a major provider’s infrastructure has exposed the terrifying truth: the privacy tech guarding millions is operating on a prayer, not proof.
The audit of Malwarebytes Privacy VPN, following its acquisition of AzireVPN, scrutinized the core software powering both services. While the final report praises a "strong security level," this framing is a dangerous distraction. The real story is in the methodology—the hunt for critical zero-day exploits and misconfigurations that could lead to a catastrophic data breach. Every unexamined line of code is a potential backdoor for malware.
"An audit is a snapshot, not a vaccine," warns a senior cybersecurity analyst familiar with the report. "The moment it's completed, the race begins again. Adversaries are constantly developing new exploits. A clean bill of health today means nothing for the phishing attack or novel ransomware strain deployed tomorrow." This underscores a systemic failure in the privacy industry: transparency is an event, not a culture.
This matters because your encrypted tunnel is only as strong as its weakest point. You use a VPN to protect financial crypto transactions, sensitive communications, and personal data from interception. If the infrastructure itself has an unpatched vulnerability, you are not anonymous; you are a target. Your data isn't just hidden—it's potentially pooled on a server ripe for exploitation.
We predict a reckoning. As blockchain security principles of verifiability become the standard, consumers will demand continuous, brutal audits, not marketing checkboxes. VPN providers that refuse will be exposed as part of the problem.
Your privacy should not be a leap of faith. Demand proof, or prepare for a breach.