EXCLUSIVE: GALAXY DIGITAL TESTNET HACK EXPOSES CRYPTO'S HIDDEN VULNERABILITY PIPELINE
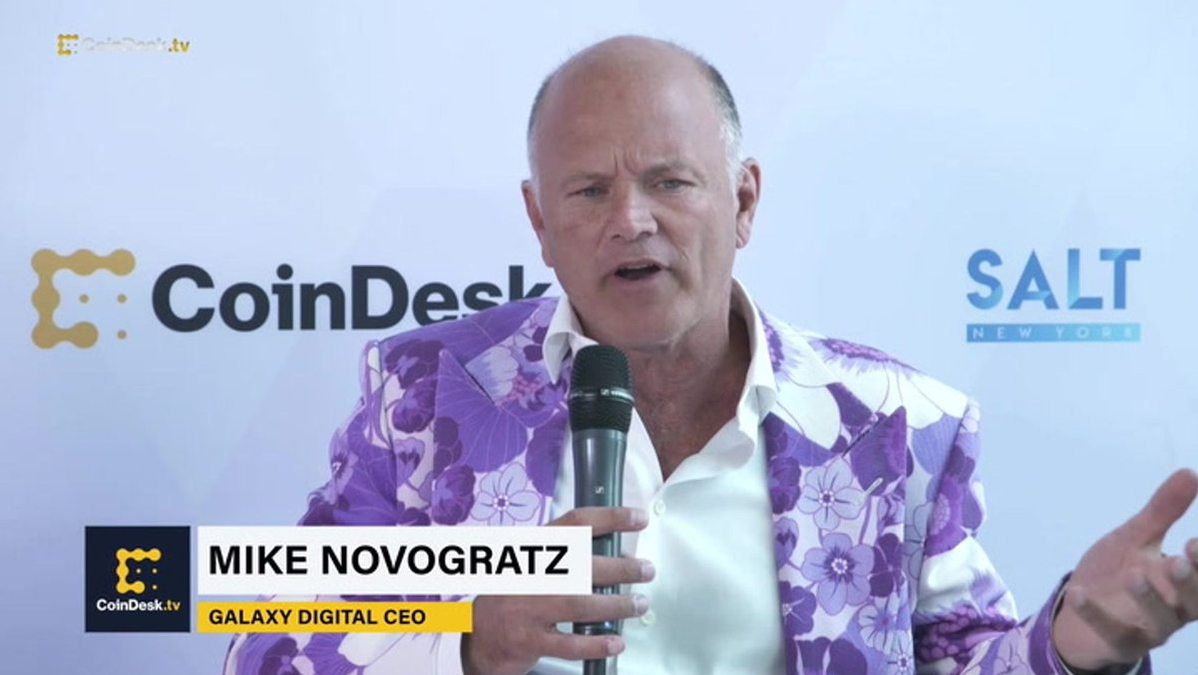
A covert breach inside Mike Novogratz's Galaxy Digital has ripped open a new front in the crypto security war. While the firm scrambles to label it "immaterial," this was a direct hit on an R&D testnet—the very laboratory where future blockchain security protocols are born. The intruders made off with less than $10,000 in test funds, but the real prize was potential intellectual property and a blueprint of internal systems. This isn't just a minor incident; it's a warning shot targeting the industry's innovation engine.
The company confirms unauthorized access was strictly limited to a segregated development workspace, with core trading systems and client accounts untouched. No client funds or data were breached. But the chilling fact remains: hackers are now systematically probing the soft underbelly of crypto firms—their development and testing environments. These zones, often considered low-risk, are treasure troves for discovering zero-day vulnerabilities before they ever hit production.
"Every testnet contains the DNA of a company's security posture," warns a senior cybersecurity consultant who advises major exchanges. "Access here can reveal architectural weaknesses, proprietary code, and testing methodologies. It's a reconnaissance mission for a much larger future attack. Calling this 'immaterial' misses the point entirely."
For every investor and user, this underscores a brutal reality: the perimeter of risk is expanding. The threat is no longer just a direct phishing attack on your wallet or a smart contract exploit. It's a multi-stage campaign that starts deep inside corporate infrastructure, seeking any vulnerability, no matter how seemingly isolated, to gain a foothold. The integrity of the entire ecosystem depends on the security of every link in the chain, including the backroom labs.
We predict a surge in similar targeted attacks on developer environments across the sector as attackers shift tactics. The race is on to lock down the entire software development lifecycle.
The next major data breach may not start in your wallet—it starts in the code that hasn't even been deployed yet.