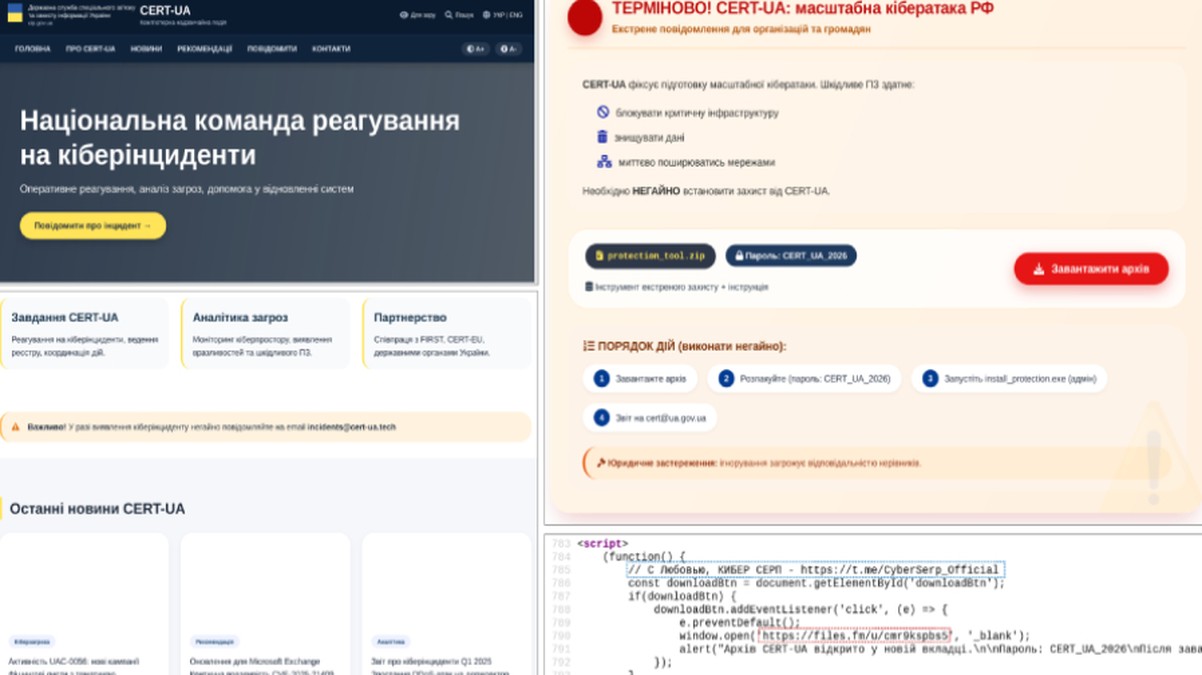
The Computer Emergency Response Team of Ukraine (CERT-UA) has issued a critical warning regarding a sophisticated and large-scale phishing campaign in which threat actors have brazenly impersonated the national cybersecurity agency itself. The operation, attributed to a group tracked as UAC-0255, involved the distribution of a remote administration tool (RAT) known as AGEWHEEZE. The attackers sent a wave of malicious emails on March 26 and 27, 2026, posing as legitimate communications from CERT-UA. The emails contained a password-protected ZIP archive, a common tactic to evade automated email security scanners, which, once opened, deployed the AGEWHEEZE malware onto victims' systems.
The scale of this campaign is particularly alarming, with initial reports suggesting the malicious emails were sent to approximately one million addresses. The impersonation of a trusted national cybersecurity entity like CERT-UA represents a significant escalation in social engineering tactics. By masquerading as a source of authority and critical security information, the attackers dramatically increase the likelihood of recipients lowering their guard and interacting with the malicious payload. The use of a password-protected archive adds another layer of deception, as recipients may believe the content is sensitive and requires an extra step for protection, thereby bypassing initial suspicion and automated detection mechanisms.
AGEWHEEZE is a powerful remote access trojan capable of granting attackers full control over a compromised system. Once installed, it can exfiltrate sensitive data, deploy additional malware, log keystrokes, and provide a persistent backdoor into corporate or government networks. The targeting of such a wide email list suggests the campaign's objectives were likely broad-spectrum espionage, credential harvesting, and the establishment of a large botnet for future attacks. The choice of impersonating CERT-UA, especially in the current geopolitical context, indicates a highly calculated effort to exploit organizational trust and the heightened state of alert within Ukrainian and potentially international entities monitoring the region.
This incident underscores several critical lessons for organizational cybersecurity. First, it highlights that no entity, not even a leading national CERT, is immune to being impersonated in phishing schemes. Security awareness training must evolve to include warnings about sophisticated impersonation of internal and trusted external agencies. Secondly, the technical controls around email security must be robust, capable of analyzing archive file contents through sandboxing or other advanced techniques, even when password-protected. Finally, organizations should establish and communicate clear, verified channels for official CERT communications, so employees can easily distinguish between legitimate alerts and malicious impersonations. The UAC-0255 campaign is a stark reminder that in the digital age, trust is a primary attack vector.