EXCLUSIVE: FORGOTTEN 2011 GAMING FORUM BREACH IS A CYBERSECURITY TIME BOMB — YOUR OLD PASSWORD COULD BE THE KEY
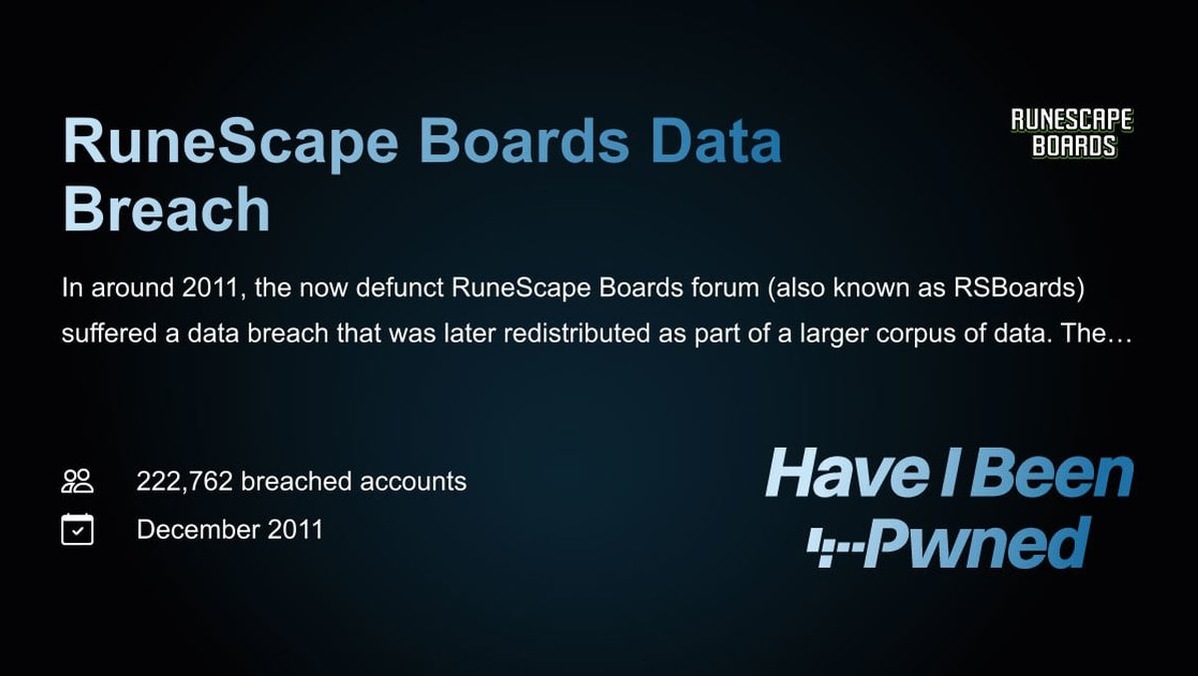
A dormant data breach from a defunct gaming forum is an active threat today. The 2011 compromise of RuneScape Boards, exposing 222,762 user records, was not an isolated event. This cache of emails, usernames, IPs, and salted MD5 password hashes has circulated for years in criminal datasets, providing fuel for credential stuffing attacks, sophisticated phishing campaigns, and identity theft. This is not a relic; it's raw material for modern cybercrime.
The breach exploited a vulnerability in the vBulletin software, a common platform at the time. While the hashes were salted, the use of MD5 is now considered cryptographically weak. This means determined attackers can crack these hashes, turning an old forum password into a master key for your current digital life. This incident underscores a brutal truth: there is no statute of limitations on exposed data. A breach from over a decade ago can be weaponized as a critical zero-day against your present-day security.
"These old, recycled datasets are gold mines for attackers," explains a veteran threat analyst. "They automate attacks using these credentials across thousands of sites. If you reused that 2011 password anywhere, you are at extreme risk of a follow-on data breach or ransomware attack. It's not about hacking in; it's about logging in."
Why should you care? Because human nature is the ultimate vulnerability. We reuse passwords. That credential from a gaming forum in 2011 might guard your email, your crypto exchange account, or your work network today. Blockchain security for your crypto wallet means nothing if you use the same password you leaked on a forum. This breach is a stark reminder that your security is only as strong as your oldest, weakest password.
We predict a surge in account takeovers linked to this and other "zombie" breaches as automated tools become more accessible. The advice is urgent and non-negotiable: CHANGE THAT PASSWORD EVERYWHERE. Enable two-factor authentication (2FA) on every possible account. Use a dedicated password manager to generate and store unique, complex passwords for every service. Your digital past is hunting your present.