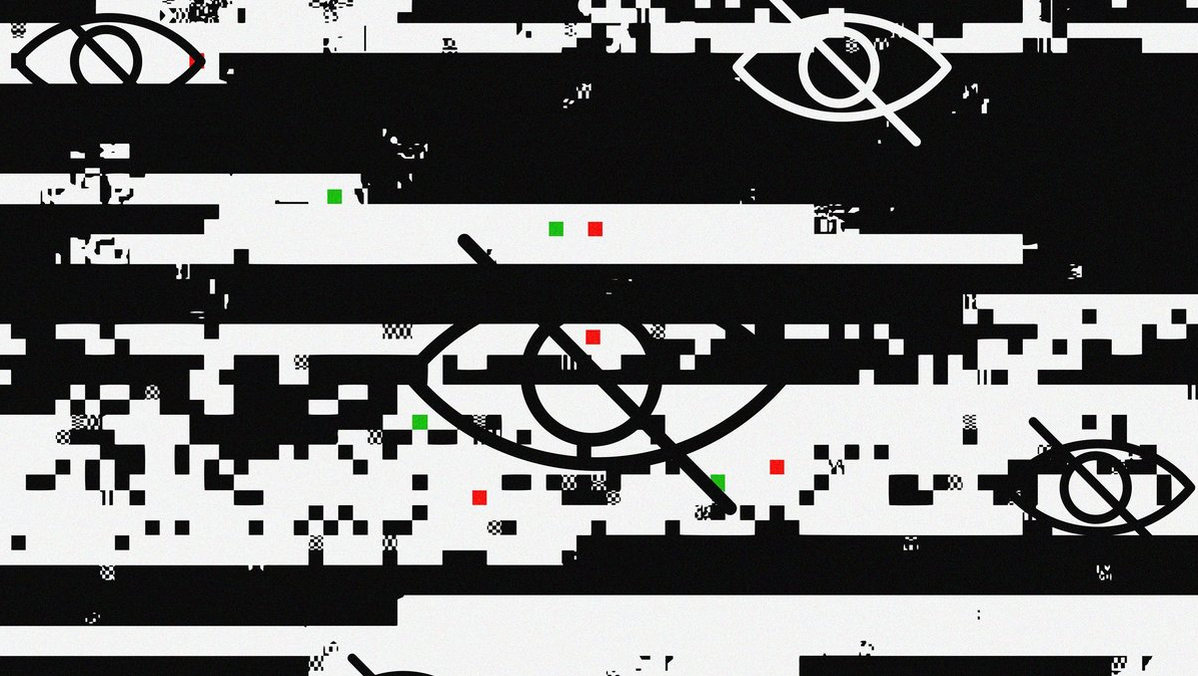
EXCLUSIVE: CANISTERWORM CYBER WEAPON DEPLOYED IN SHADOW WAR, TARGETING IRAN WITH DATA-ANNIHILATING MALWARE
A dangerous new front has opened in cyber warfare. A financially motivated cybercrime syndicate, TeamPCP, has weaponized its infrastructure to launch a targeted wiper attack against Iran, marking a perilous escalation where criminal tools are repurposed for geopolitical sabotage. Dubbed 'CanisterWorm,' the malware autonomously spreads through misconfigured cloud services, but its final payload is brutally selective: it permanently destroys data only on systems using Iran's time zone or Farsi language settings.
This is not a typical ransomware shakedown; it's a targeted digital scorched-earth campaign. The group's modus operandi involves industrial-scale exploitation of known vulnerabilities and cloud misconfigurations, not sophisticated zero-day exploits. They automate attacks on exposed Docker APIs, Kubernetes clusters, and cloud control planes, turning vast swaths of the internet into a self-propagating criminal ecosystem. Their recent supply chain attack against a popular vulnerability scanner, Trivy, demonstrated their capability to steal SSH keys, cloud credentials, and even cryptocurrency wallets at scale.
A senior threat intelligence analyst, speaking on condition of anonymity, stated, "This is a paradigm shift. TeamPCP has built a cloud-native exploitation platform. Their strength isn't in novelty, but in ruthless automation and integration of recycled attack techniques. They've now added a politically-motivated wiper to their arsenal, blurring the line between crime and cyberwar." The deployment of this wiper from the same infrastructure used in their financial attacks suggests a chilling diversification of intent.
Every organization reliant on cloud infrastructure is now in the crosshairs of this automated threat. The group predominantly targets Azure and AWS, meaning a simple misconfiguration could invite a catastrophic data breach. Their phishing of credentials and lateral movement tactics are a blueprint for disaster, proving that foundational cybersecurity hygiene is no longer optional—it's the only defense against industrialized attacks.
We predict this event will catalyze a new wave of copycat attacks, where criminal groups auction their botnets and malware to the highest geopolitical bidder. The fusion of financial cybercrime with state-aligned disruptive actions creates a volatile, unaccountable force in global conflicts.
The cloud has become the battlefield, and the worms are now learning who to spare and who to destroy.