EXCLUSIVE: GLOBAL CYBER TAKEDOWN UNCOVERS SHOCKING VULNERABILITY IN YOUR HOME
A massive international sting has just shattered the world's most dangerous IoT botnet armies. In a covert operation, authorities from the US, Germany, and Canada seized the Command and Control infrastructure for the Aisuru, KimWolf, JackSkid, and Mossad botnets. These networks turned millions of smart devices—from cameras to routers—into weapons for devastating DDoS attacks. This is not just a win; it's a terrifying reveal of our collective insecurity.
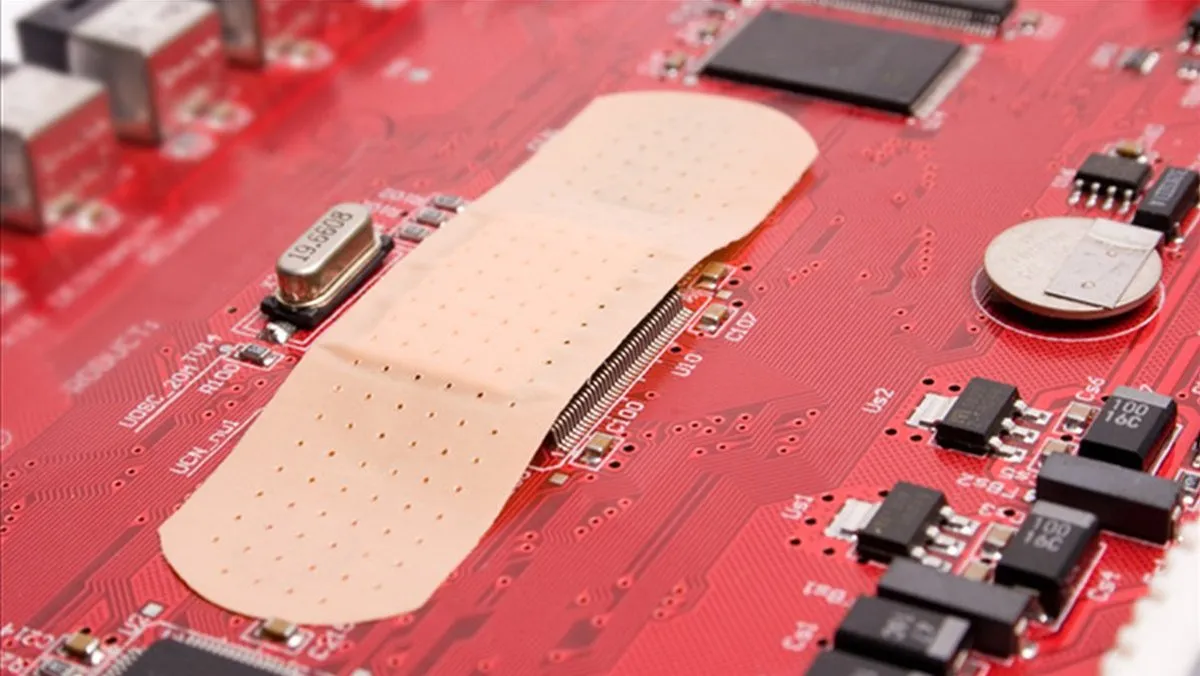
The core fact is chilling: these botnets preyed on default passwords and unpatched vulnerabilities in everyday Internet of Things devices. This operation stopped one wave of attacks, but the underlying zero-day exploits and malware kits used to build these armies are still for sale in darknet markets. Every unsecured device is a potential soldier in the next ransomware campaign or data breach.
"These takedowns are surgical strikes on symptoms, not the disease," warns a former intelligence official involved in cyber operations. "The criminal ecosystem that creates this phishing and exploit infrastructure is more resilient than ever, often funded by crypto ransoms and adapting within hours." The focus now must shift to blockchain security to trace these illicit payments and dismantle the financial incentives.
Why should you care? Because your smart thermostat or baby monitor could be the next target. This disruption proves that the devices we invite into our homes are the weakest link in global cybersecurity. Consumers and manufacturers have been asleep at the wheel, and criminals have been driving.
We predict a brutal surge in new, more sophisticated IoT malware within months, as threat actors rebuild using lessons learned from this takedown. The next wave will be harder to stop.
The bots are down, but the war for your devices is just heating up.