The City of Foster City, California, has announced plans to declare a local state of emergency in response to a significant ransomware attack that has disrupted municipal services. The attack, which encrypted critical city systems, underscores the growing threat ransomware poses to local government infrastructure nationwide. City officials confirmed the incident to CBS News, stating that the declaration is a procedural step to unlock state and federal resources, streamline emergency procurement, and facilitate a faster recovery. While the full scope of the data breach is under investigation, the attack has already impacted online payment systems, business license portals, and other digital services, forcing staff to revert to manual, paper-based processes.
Ransomware attacks on municipalities have become a disturbingly common occurrence, exploiting often underfunded IT security postures and the critical nature of public services. These attacks typically involve malicious software that locks access to computer systems or data until a ransom is paid, often in cryptocurrency. For cities like Foster City, the immediate consequences are operational paralysis and a direct threat to citizen services, from permit applications to public records access. The decision to declare a state of emergency is a stark indicator of the severity of the incident, moving it from an IT issue to a full-blown civic crisis requiring coordinated emergency management protocols.
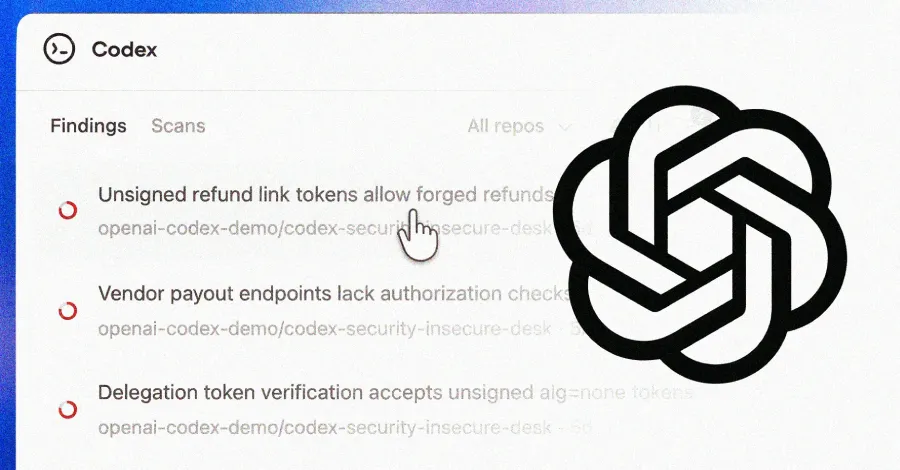
The cybersecurity implications of this attack are profound. It highlights the urgent need for local governments to prioritize robust cybersecurity defenses, including comprehensive offline backups, employee phishing training, network segmentation, and updated incident response plans. Paying ransoms is generally discouraged by law enforcement agencies like the FBI, as it funds criminal enterprises and does not guarantee data recovery. Instead, the focus for Foster City and similar entities must be on resilience and restoration from secure backups. This incident will likely trigger a post-mortem analysis to identify the attack vector, whether through a phishing email, unpatched software vulnerability, or compromised third-party service.
As Foster City works with cybersecurity experts to restore systems and investigate the breach, the event serves as a critical warning to other municipalities. The attack on Foster City is not an isolated event but part of a broader trend targeting the public sector. It reinforces the necessity for continuous investment in cybersecurity infrastructure and proactive threat hunting. For residents, the advice remains vigilant: monitor official city communications for updates, be cautious of potential phishing scams that may exploit the news, and understand that personal data provided to the city could be at risk. The road to recovery will be measured in weeks or months, not days, demonstrating the long-tail cost of such cyber intrusions on public trust and operational continuity.