THE GENTLEMEN'S GAMBIT: HOW A $48,000 DISPUTE UNLEASHED A GLOBAL FORTIGATE CRISIS
This isn't a loud breach; it's a silent siege. The cybersecurity landscape is under a quiet, sustained pressure where old exploits refuse to die and new threats operate with chilling practicality. The background noise of digital conflict is rising, and this week's bulletin reveals a perfect storm of negligence and innovation that every enterprise must heed.
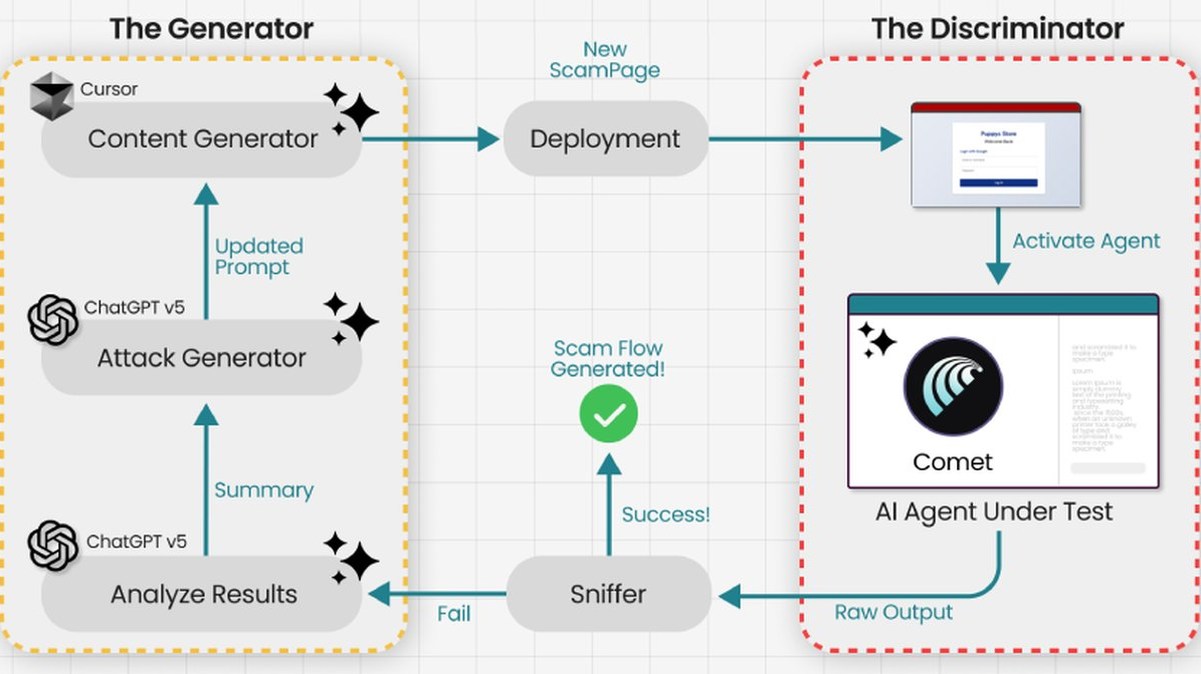
At the epicenter is "The Gentlemen," a Ransomware-as-a-Service operation born from a $48,000 payment dispute on the dark web. This isn't just another malware group; it's a case study in modern cybercrime efficiency. They weaponize a critical FortiOS zero-day vulnerability, CVE-2024-55591, for initial access. More alarmingly, they sit on an operational database of 14,700 ALREADY exploited FortiGate devices globally, with nearly 1,000 validated, brute-forced VPN credentials queued for attack. Their use of BYOVD techniques to kill security processes at the kernel level shows a sophisticated grasp of defense evasion.
Parallel to this, a quartet of critical flaws in BMC FootPrints ITSM software demonstrates how chained vulnerabilities—an authentication bypass leading to remote code execution—create devastating exploits. It’s a masterclass in how phishing lures can lead to total system compromise through seemingly minor unpatched entry points.
"These groups are not just breaking in; they are moving in," warns a senior threat analyst familiar with the briefing. "They exploit foundational vulnerabilities in perimeter and service management software that many assume are secure. The pre-positioned access in the FortiGate ecosystem is particularly egregious—it's a standing army at the gate."
Why should you care? Because this is the new normal. It’s the avoidable data breach waiting to happen. It’s the phishing email that leverages an unpatched zero-day. It underscores a glaring gap in blockchain security for ransom payments and exposes how crypto fuels this entire criminal economy. Your network's background noise is now the threat.
We predict the convergence of these tactics—the targeted exploitation of network appliances paired with the abuse of common business software—will trigger the next wave of cascading enterprise breaches. The quiet pressure is building to a breaking point.
Ignoring the subtle warnings is now the greatest vulnerability of all.