A sophisticated cyber espionage campaign attributed to the suspected India-linked threat actor SideWinder is significantly expanding its operations across Southeast Asia. Security researchers have identified a marked increase in the group's activities, which now systematically target government entities, telecommunications firms, and critical national infrastructure. The campaign's primary objective is the establishment of persistent, long-term access to sensitive networks to facilitate intelligence gathering and surveillance.
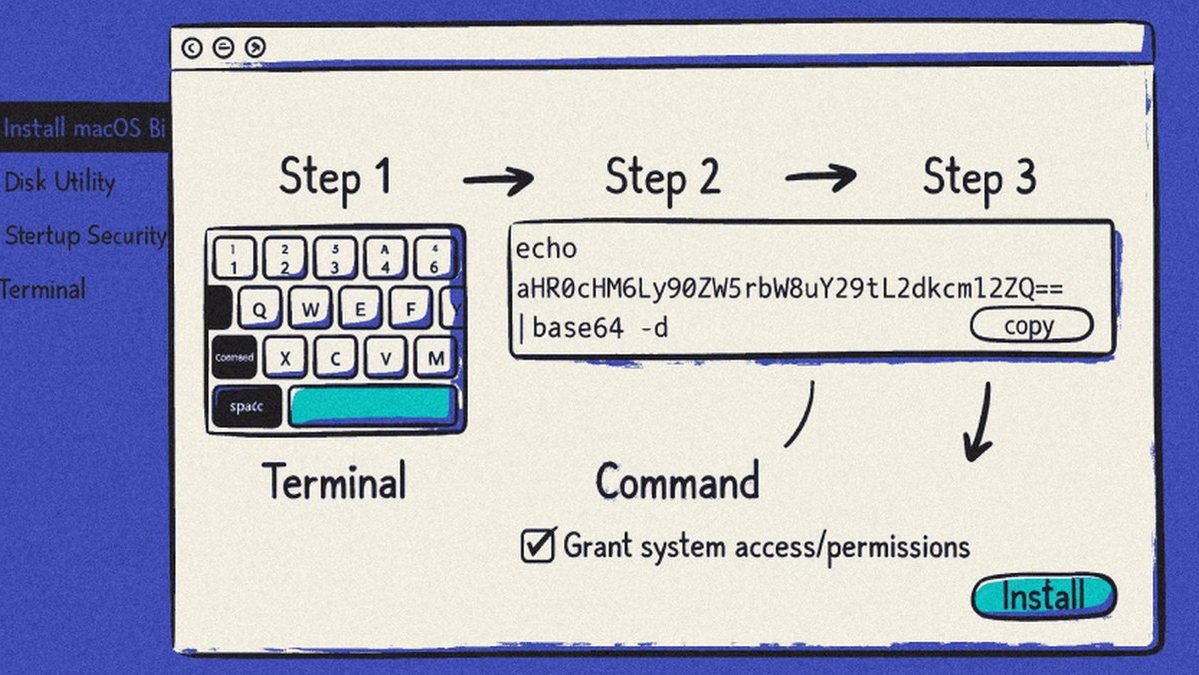
The group employs a multi-faceted attack methodology to achieve its goals. Initial compromise is frequently achieved through highly targeted spear-phishing emails, often impersonating legitimate government or military bodies to trick recipients into opening malicious attachments or links. Once a foothold is established, SideWinder leverages a combination of older, unpatched software vulnerabilities and custom-developed malware to move laterally through networks. A key hallmark of their operational security is the use of rapidly rotating command-and-control (C2) infrastructure, frequently employing compromised websites and short-lived domains to evade detection and blacklisting by security defenses.
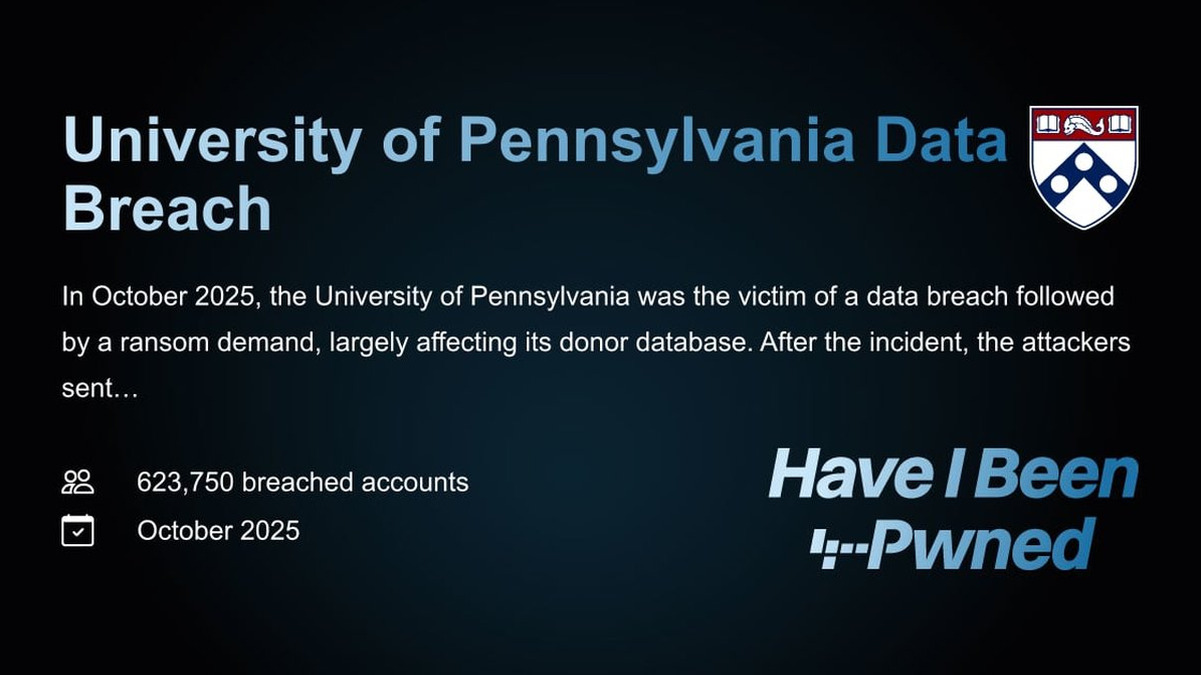
The expansion of SideWinder's campaign represents a serious threat to regional security and economic stability. By targeting telecom operators, the group potentially gains access to vast amounts of communications metadata and user data, enabling sophisticated surveillance. Attacks on critical infrastructure sectors could pave the way for disruptive or destructive operations in the future. The group's focus on governmental bodies directly threatens state secrets, diplomatic communications, and national security planning.
Defending against such a persistent and evolving threat requires a proactive and layered security posture. Organizations, particularly in the targeted sectors and regions, must prioritize patching known software vulnerabilities, even those considered older, as these remain a favored exploitation vector. Advanced email security solutions and continuous user awareness training are critical to countering the initial spear-phishing vector. Furthermore, network monitoring for anomalous outbound traffic and the use of threat intelligence feeds to track the group's rotating C2 infrastructure are essential for early detection and mitigation of these stealthy intrusions.