EXCLUSIVE: AMAZON UNCOVERS CYBERESPIONAGE BLUNDER AS INTERLOCK RANSOMWARE'S ZERO-DAY SIEGE EXPOSED
A catastrophic data breach campaign is underway right now, leveraging a secret weapon: a Cisco firewall zero-day flaw rated a perfect 10.0 for severity. Amazon Threat Intelligence has exposed the Interlock ransomware gang's month-long head start, exploiting the critical vulnerability, CVE-2026-20131, to seize root control of corporate networks globally. This isn't a hypothetical threat; it's an active cyber war.
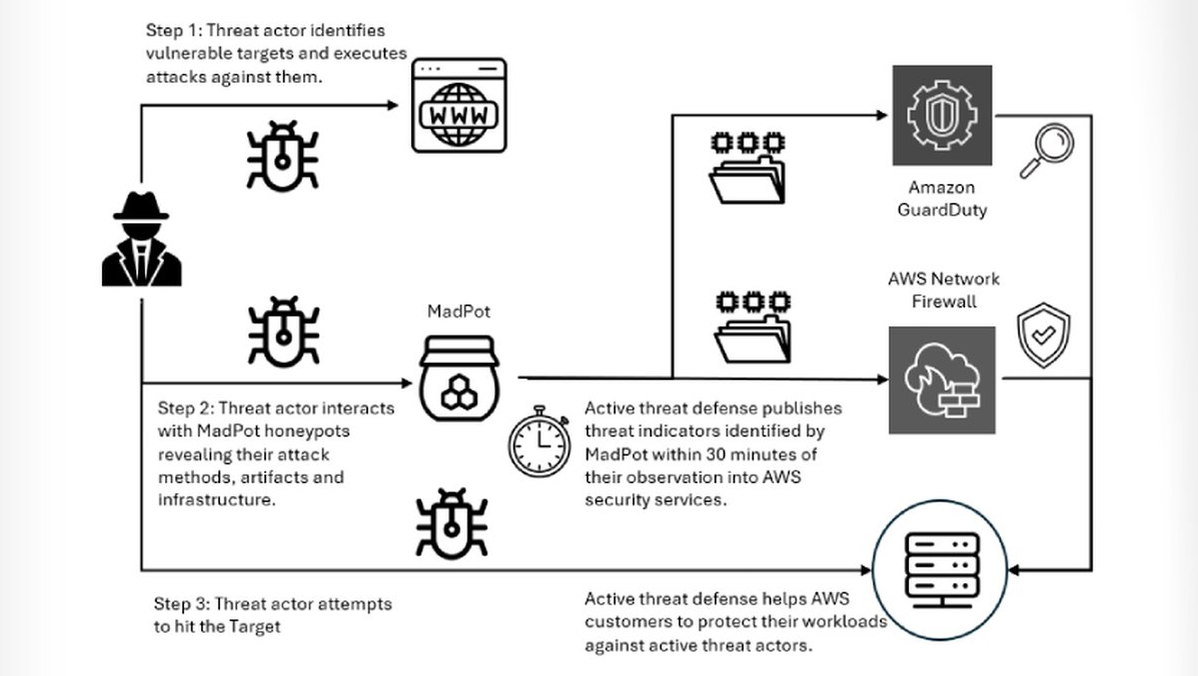
The vulnerability is a nightmare for cybersecurity teams: insecure deserialization allowing unauthenticated attackers to run any Java code as root. Amazon's sensors confirmed the exploit was used as a zero-day since late January, a full month before Cisco's public disclosure. This gave the criminals a devastating window to plant malware and establish deep, persistent access.
"The attackers had a week's head start before defenders even knew to look," revealed a senior Amazon security executive. The breakthrough came from a stunning operational security blunder by the threat actors themselves. A misconfigured server leaked their entire toolkit, exposing a multi-stage attack chain, custom remote access trojans, and sophisticated evasion techniques designed to bypass traditional defenses.
Why should every executive care? This campaign moves beyond simple phishing. It uses a reliable exploit chain to deploy ransomware, directly threatening operational continuity and extorting crypto payments. The implications for blockchain security and digital asset protection are severe, as these networks become prime targets for infiltration and sabotage.
We predict a surge in copycat attacks targeting unpatched Cisco systems in the coming weeks. The blueprint is now public, and the digital gold rush is on for other criminal groups.
Your firewall just became your greatest vulnerability. Patch it today or prepare to pay tomorrow.