EXCLUSIVE: THE INVISIBLE SKIMMER - HOW A FAVICON'S HIDDEN DATA BYPASSES ALL AI SECURITY SCANS
A new breed of CYBERSECURITY threat is operating in plain sight, exploiting the precise boundary where AI-powered code analysis ends and the browser begins. Investigative findings reveal a sophisticated MALWARE campaign, a RANSOMWARE-adjacent DATA BREACH operation, where the entire attack payload is hidden not in code, but within the EXIF metadata of a simple website favicon. This technique represents a catastrophic failure of traditional security models, exploiting a critical VULNERABILITY in how we perceive defense.
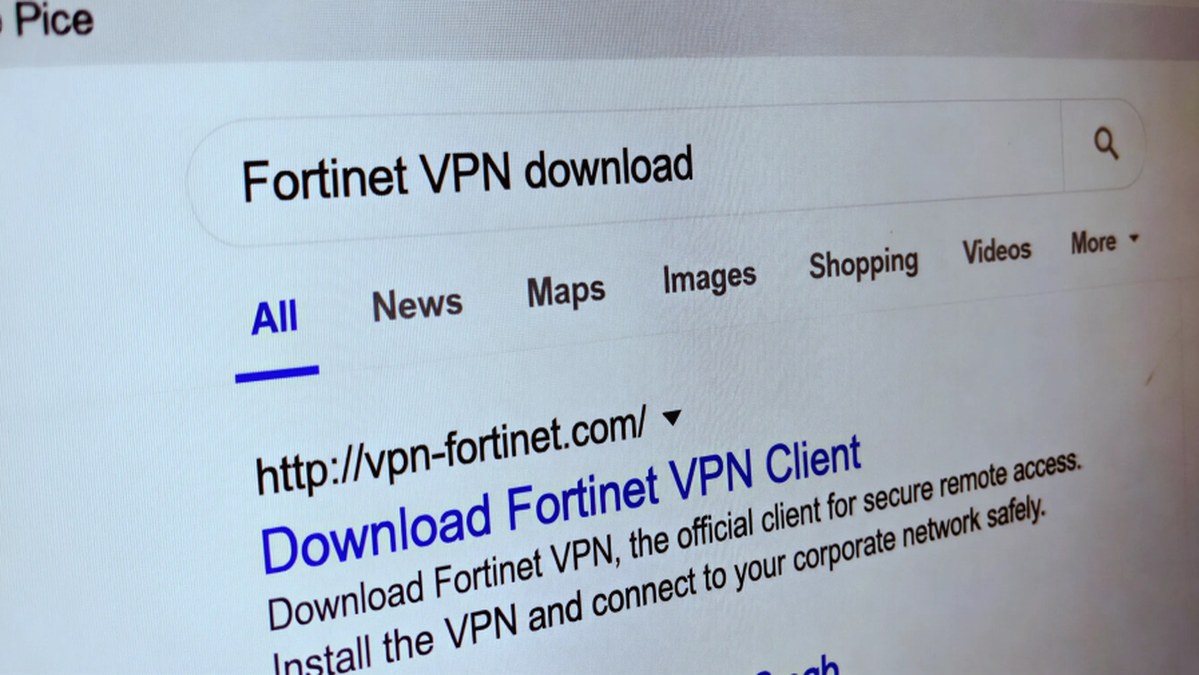
The attack chain is a masterclass in evasion. A compromised third-party script loads what appears to be a standard favicon from a seemingly legitimate content delivery network. The real PAYLOAD, however, is smuggled inside the image's own metadata—a space no repository scanner ever examines. The malicious JavaScript is extracted and executed directly in the user's browser at the precise moment of checkout. This is not a PHISHING lure; this is a direct supply chain EXPLOIT. The skimmer never touches the merchant's source code, rendering static analysis tools completely blind. It's a ZERO-DAY against the security process itself.
"Organizations are being sold a false sense of security," warns a senior threat analyst specializing in financial cybercrime. "They deploy AI scanners on their repositories and think they're covered, but this entire attack surface—the dynamic, client-side execution of third-party assets—exists outside that scope. The tool isn't broken; the threat model is. This is where runtime monitoring is non-negotiable."
For every business operating online, this is a wake-up call. Your checkout page is only as secure as the weakest script it loads, and attackers are no longer just hacking your code—they're hijacking your trusted dependencies. The promise of BLOCKCHAIN SECURITY for transactions means nothing if the page collecting the data is already compromised. This technique could easily be adapted to target CRYPTO wallet interfaces and exchanges, making the financial stakes astronomical.
We predict a dramatic surge in these "in-memory" skimmers throughout the year, forcing a painful and expensive reckoning for e-commerce and SaaS platforms. The age of trusting your supply chain is over.
The malware is in the pixels, and your scanner is looking at the wrong picture.