EXCLUSIVE: NORTH KOREAN HACKERS WEAPONIZE TRUST IN LATEST CYBER SIEGE, TURNING VICTIMS INTO UNWITTING MALWARE DISTRIBUTORS
A chilling new campaign from the notorious North Korean Konni hacking group is exploiting human trust as its primary vulnerability, turning compromised victims into pawns to attack their own contacts. This is not just another data breach; it's a sophisticated social engineering operation using a trusted messaging platform as a digital Trojan horse.
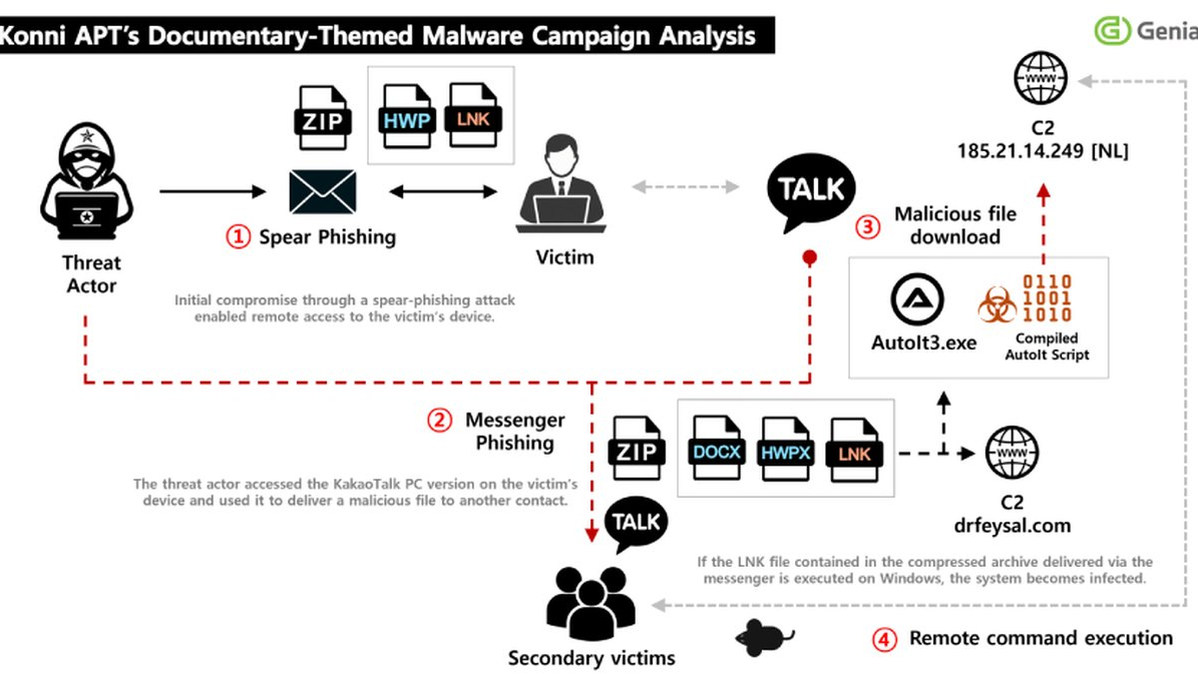
South Korean intelligence firm Genians has exposed the operation, where spear-phishing emails disguised as official "North Korean human rights lecturer" appointments deliver the initial blow. The hook is a malicious ZIP file. Once opened, it deploys a Windows LNK file that silently fetches a powerful remote access trojan called EndRAT. The malware hides in plain sight, displaying a decoy PDF while establishing deep persistence on the endpoint.
The real escalation is what happens next. After lurking for weeks to steal sensitive documents, the hackers seize control of the victim's desktop KakaoTalk application. They then selectively send malicious payloads directly to the victim's own contacts, abusing inherent trust to propagate the infection virally. This method transforms every compromised device into a new launchpad for malware distribution.
"This is a masterclass in psychological exploitation," a senior cybersecurity analyst told us, speaking on condition of anonymity. "They are not just exploiting a software zero-day; they are exploiting a 'trust-day' vulnerability in human behavior. The use of a signed-in, legitimate app like KakaoTalk bypasses countless modern security controls designed to stop phishing and malware from external sources."
For anyone using messaging platforms for work or personal communication, this is a dire warning. Your digital identity can be weaponized against your closest colleagues, friends, or family. The Konni group's use of crypto-themed lures and their history of remote device wipes shows a ruthless, multi-faceted threat actor with endless ambition. Where is the blockchain security for our social graphs?
We predict this "trust-hijacking" tactic will be copied by ransomware gangs and state-sponsored actors worldwide within months, creating a new wave of hyper-personalized, nearly undetectable breaches.
Your contact list is now a potential exploit. Guard it accordingly.