The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has escalated its warning regarding a security flaw in the Wing FTP Server software, adding it to its Known Exploited Vulnerabilities (KEV) catalog. Tracked as CVE-2025-47813 with a CVSS score of 4.3, this medium-severity information disclosure vulnerability can leak the full installation path of the application under specific conditions. According to CISA, the flaw exists because the server generates error messages containing sensitive information when an overly long value is supplied in the `UID` session cookie. This vulnerability impacts all versions of Wing FTP Server up to and including version 7.4.3.
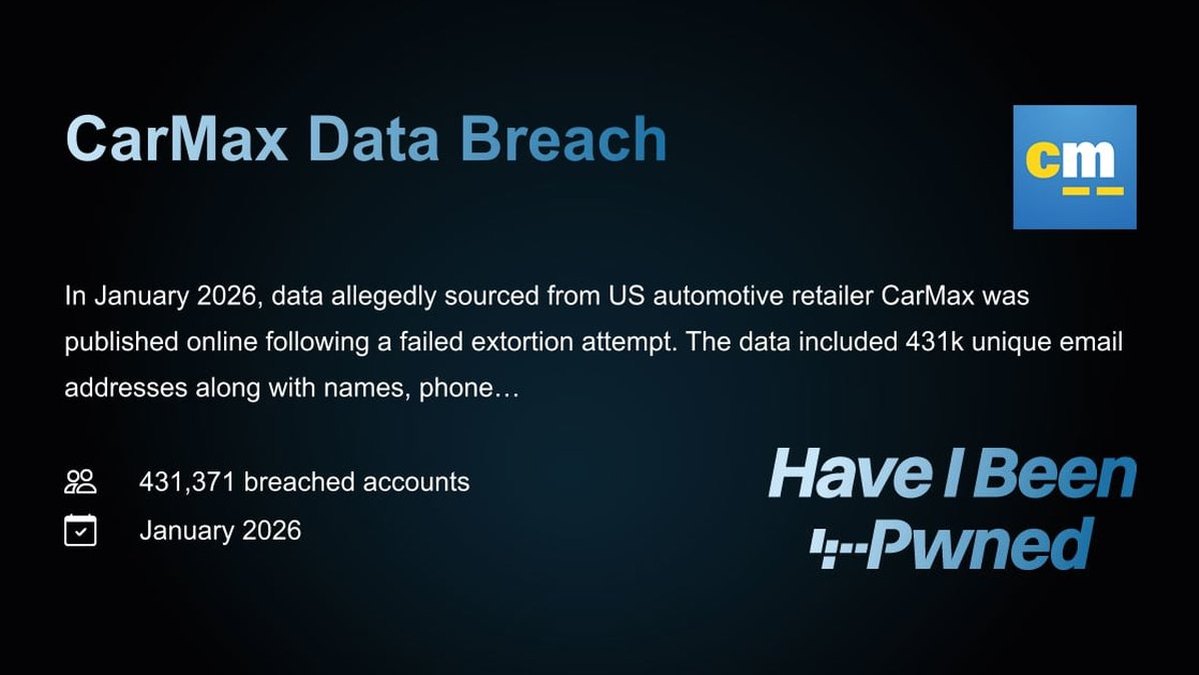
The vulnerability was responsibly disclosed by researcher Julien Ahrens of RCE Security and was patched by the vendor in version 7.4.4, released in May 2025. Notably, this same update also addressed a separate, critical remote code execution flaw, CVE-2025-47812 (CVSS score: 10.0). Technical analysis reveals that the `/loginok.html` endpoint fails to properly validate the length of the `UID` cookie value. If an attacker supplies a value exceeding the operating system's maximum path length, it triggers an error that inadvertently reveals the complete local file system path where the Wing FTP application is installed.
While the path disclosure itself is rated as medium severity, it poses a significant threat as a precursor to more severe attacks. As researcher Julien Ahrens noted, knowledge of the exact server path can be instrumental for an authenticated attacker in successfully exploiting other vulnerabilities, such as the critical CVE-2025-47812, which allows for remote code execution. Evidence suggests that CVE-2025-47812 has already been exploited in the wild since at least July 2025, with attackers using it to download malicious Lua scripts, perform reconnaissance, and deploy remote access tools.
In response to confirmed active exploitation, CISA has mandated that all U.S. Federal Civilian Executive Branch (FCEB) agencies apply the vendor-provided patch by a specified deadline to secure their networks. Although specific details of the in-the-wild attacks leveraging CVE-2025-47813 are not public, its addition to the KEV catalog underscores the practical risk. Cybersecurity professionals are strongly advised to immediately upgrade Wing FTP Server to version 7.4.4 or later. For organizations unable to patch immediately, implementing strict network segmentation and monitoring for anomalous requests to the `/loginok.html` endpoint are critical interim defensive measures.