EXCLUSIVE: STORM-2561'S SEO POISONING TRAP IS THE ULTIMATE BETRAYAL OF TRUST
Imagine searching for critical enterprise software, only to have a search engine you trust deliver you straight into the hands of hackers. That is the chilling reality of a massive new credential theft campaign, where the very tools meant to protect your business become the weapon used to destroy it. Microsoft has pulled back the curtain on a sophisticated operation run by the threat actor Storm-2561, revealing a systemic exploitation of our faith in search rankings and software brands.
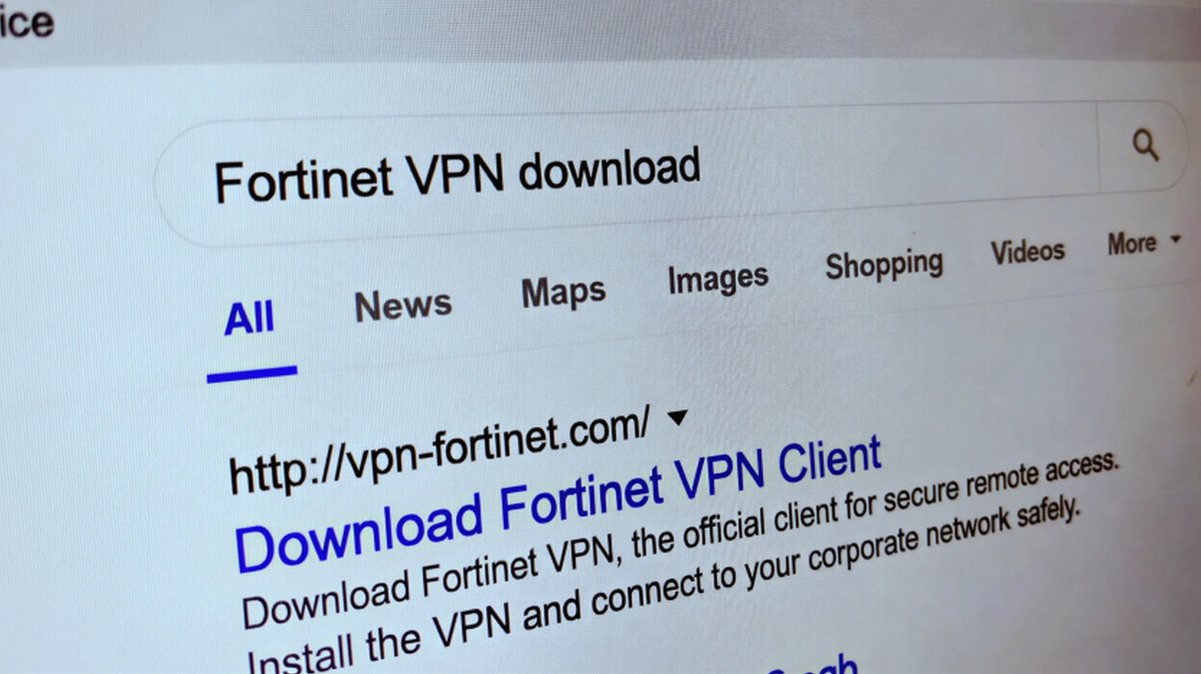
The campaign is a masterclass in social engineering, using SEO poisoning to hijack searches for legitimate VPN clients from major vendors. Users are redirected to malicious, attacker-controlled websites and tricked into downloading digitally signed trojan installers. These fake VPN clients are wolves in sheep's clothing, perfectly mimicking trusted software while silently deploying information-stealing malware. The ultimate prize? Your corporate VPN credentials, granting attackers a direct tunnel into the heart of your network.
"This represents a fundamental weaponization of the software supply chain and user trust," explains a senior cybersecurity analyst familiar with the investigation. "The actors are not just exploiting a technical vulnerability; they are exploiting the human instinct to trust a familiar brand name and a high search result. It's psychological warfare." The malware establishes persistence on infected machines, ensuring it survives reboots and continues its clandestine mission.
This is not just another data breach. This is a direct assault on the perimeter of thousands of organizations. With stolen VPN credentials, attackers can bypass firewalls, move laterally undetected, and launch devastating ransomware attacks or orchestrate massive data exfiltration. In an era where remote work is standard, a compromised VPN is a skeleton key to the entire kingdom. The abuse of platforms like GitHub to host the malicious installers adds a further veneer of legitimacy, making traditional security warnings useless.
We are witnessing the evolution of the zero-day. The exploit is no longer just a flaw in code; it is a flaw in our digital ecosystem—the inherent trust we place in search engines and software signatures. As blockchain security promises a future of verified transactions, this campaign shows our present is dangerously malleable. The next phase will see this model applied to crypto wallet software and financial platforms, with phishing lures becoming indistinguishable from reality.
Your search bar is now a threat vector. Guard it accordingly.