A sophisticated cyber espionage campaign, suspected to be state-sponsored and originating from China, has been systematically targeting military organizations across Southeast Asia since at least 2020. Tracked by Palo Alto Networks Unit 42 under the designation CL-STA-1087, the operation demonstrates a high degree of strategic patience and precision, focusing on intelligence collection rather than broad data theft. Security researchers Lior Rochberger and Yoav Zemah noted that the attackers specifically sought out highly sensitive documents related to military capabilities, internal organizational structures, and details of collaborative efforts with Western armed forces. This targeted approach aligns with the hallmarks of an Advanced Persistent Threat (APT) group, characterized by long-term, stealthy operations designed for sustained access to high-value targets.
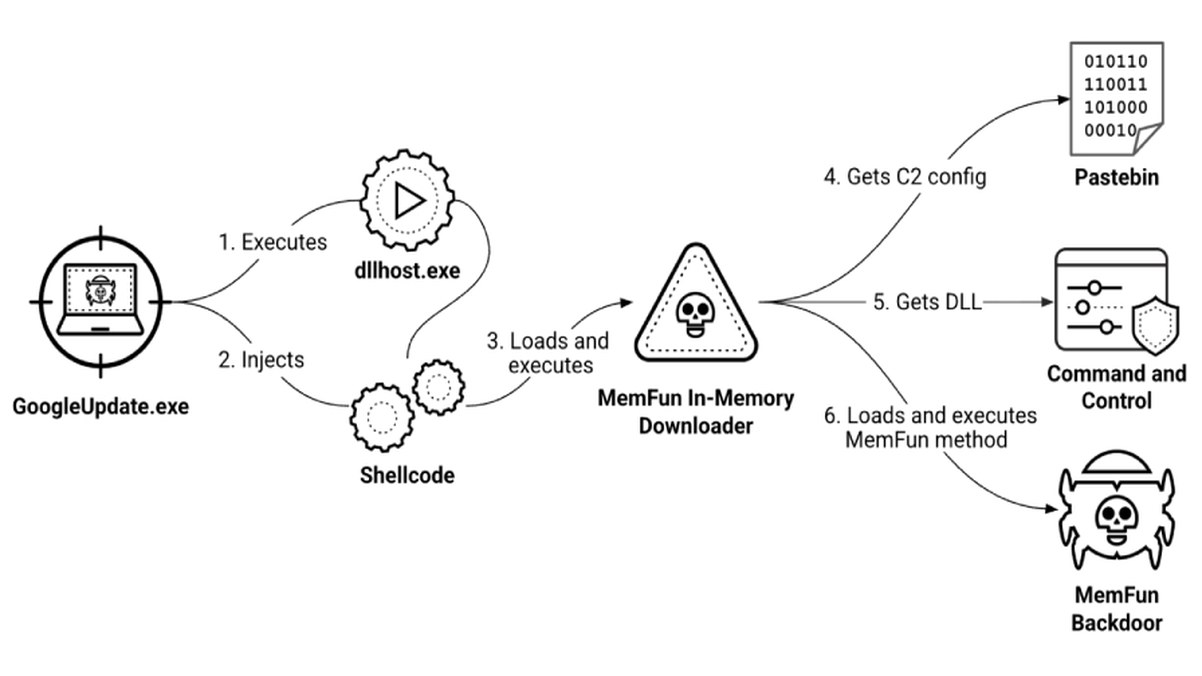
The campaign's technical execution reveals a mature and evasive threat actor. The initial infection vector remains unclear, but researchers detected the intrusion through suspicious PowerShell activity. This script was engineered to lie dormant for six hours before establishing a reverse shell connection to a command-and-control (C2) server controlled by the attackers. The primary tools deployed in this campaign are custom backdoors named AppleChris and MemFun, alongside a credential harvesting utility called Getpass. The use of AppleChris is particularly notable; different versions of the backdoor are deployed across compromised endpoints following lateral movement within the network. This tactic helps maintain persistence and evades signature-based security detection.
The attackers' actions within the compromised networks were highly deliberate. Beyond deploying malware, they conducted extensive searches for specific, sensitive information. This included official meeting records, documentation of joint military exercises, and detailed assessments of operational capabilities. The focus on such material underscores the campaign's objective: to gather strategic intelligence on regional military posture and international defense partnerships. The operational infrastructure supporting these attacks is described as highly stable, further indicating significant resources and planning behind the campaign.
This long-running espionage operation highlights the persistent digital threats faced by governmental and military entities in geopolitically sensitive regions. The use of custom malware, strategic patience, and a clear focus on intelligence collection over disruption points to a well-resourced, state-aligned actor. For defense organizations and critical infrastructure operators, this campaign serves as a critical reminder of the need for robust network monitoring, behavioral analytics to detect anomalous activities like dormant PowerShell scripts, and a defense-in-depth strategy that goes beyond traditional signature-based detection to counter such advanced, persistent threats.